A year in cybersecurity and cybercrime: 2012 review

Stop Online Piracy Act (SOPA)... stopped
The Stop Online Piracy Act (otherwise known as "SOPA") would have been the most threatening act of legislation to the global Internet to date had it passed. Along with the PROTECT-IP ("PIPA") and OPEN acts, which ran through the Senate, these bills in singular and collectively would have threatened the very existence of the open Web as we know it.
SOPA alone would have allowed Web sites to be shuttered, no matter where they are in the world, by blocking them at server level and starving them of oxygen. Any site even to have allegedly breached copyright could be effectively shut down by the U.S. government with little oversight or process of appeal. Google-owned YouTube, for instance, could have fallen foul of the law if someone uploaded a copyright infringing video, leading to a widespread site block.
The Internet as a collective rallied around and protested in a way that had never been tested or tried before. Many major Web sites shut their doors for 12 or 24 hours during 'Black Wednesday' to protest the bill. More than 75,000 Web sites blacked out, including Wikipedia and Google. Days later, it was shelved by the U.S. House of Representatives and ultimately the geeks 'won.'
However, the White House found itself on the right side of the powerful Internet community after it said it would veto any such bill should it pass along the President's desk.
Anonymous records U.K. police/FBI call; publishes it
In February, Anonymous settled a score with anti-Anonymous police in the U.K. and the U.S., by breaching a secure conference call in which the hacking collective was discussed, along with names of alleged members who had attacked high-value infrastructure targets and companies. It was no doubt a serious embarrassment for law enforcement on both sides of the Atlantic.
Not only did they breach the cybercrime call, it was recorded and subsequently uploaded to YouTube. The call shed light on U.S. and U.K. intelligence sharing arrangements, and clearly shows that a number of law enforcement units are working together in a bid to track down those who were involved in the previous and continued hacking attacks.
CBS News' 60 Minutes covers Stuxnet
Cybercrime to cyberwarfare: from low-level criminals to high-levels of state attacking countries, government targets, and their critical national infrastructure.
CBS News "60 Minutes" detailed how the Stuxnet cyberweapon was used, and how may have been behind the cyberattack. Many pointed fingers at the U.S. working with Israel, but even to this day it remains unclear who was behind the cyberattack.
Stuxnet, one of the most famous of all cyberweapons, specifically targeted Iran's nuclear facility, among other high value plants. In attacking the facility's networks, it caused a mini-meltdown at the unit that resulted in physical damage to the nuclear centrifuges, setting the program back by many months if not years.
See you later, SOPA. Oh wait, hello CISPA
Only a few months after SOPA was defeated by the collective protest power of the Web, in spite of the White House threatening to veto such a bill should it pass across Obama's desk, the Cybersecurity Intelligence Sharing and Protection Act (CISPA) came along and threatened to do just as much -- if not more damage than SOPA and PIPA would have done.
With support from major U.S. technology firms, such as Facebook, Microsoft, Verizon, Intel -- and so on -- the bill would allow the U.S. government to remove legal barriers that currently prevent companies, though exempt from the Fourth Amendment, from handing data to the government in order to share intelligence easily across the various intelligence and law enforcement agencies, without the need for a warrant. In spite of it being a "cybersecurity" tool in the global war on terrorism and online crime, the term is not actually defined in the bill.
Later in the year, though CISPA is still under review and yet to become law, President Obama signed a classified directive that would allow federal agencies to react accordingly -- including "offensive" action -- against those who breach networks, dish out cyberattacks and hack networks.
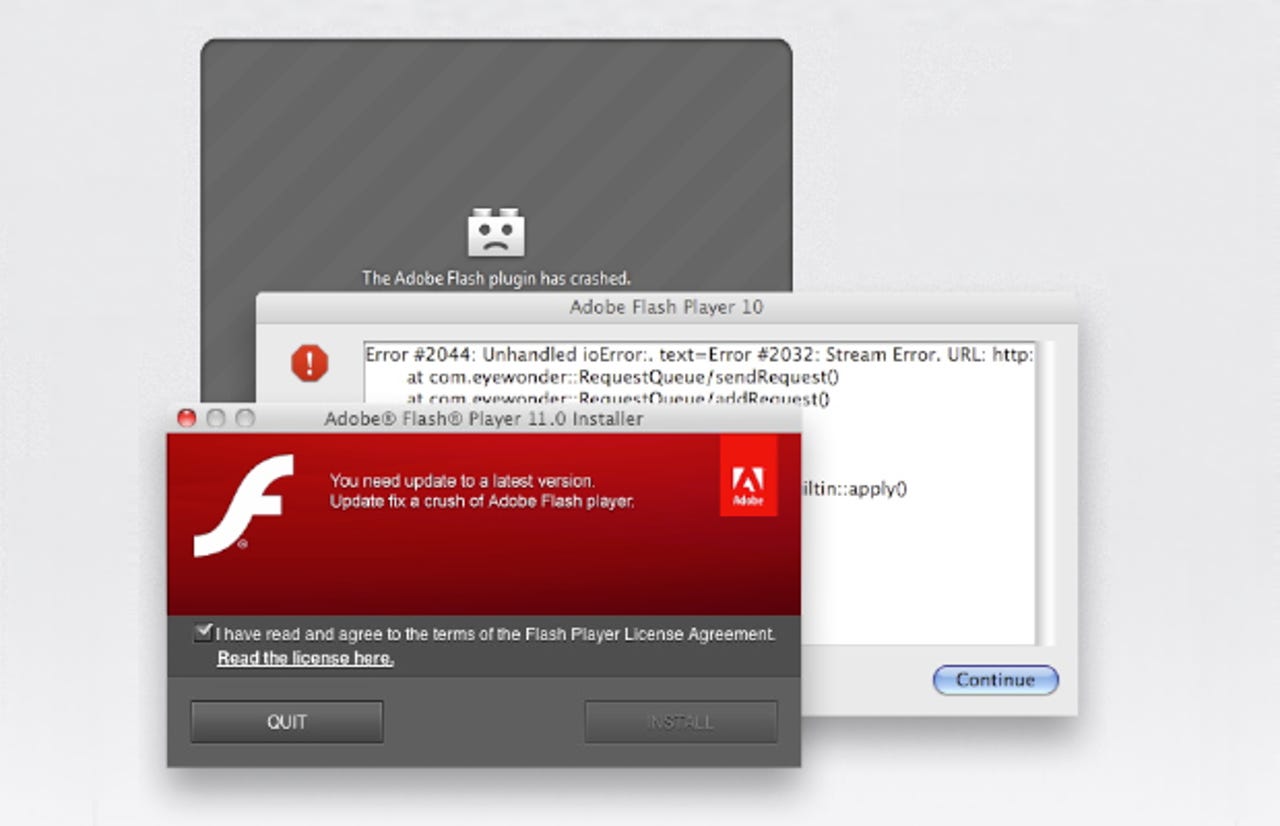
Flashback, the first major Mac attack
The Flashback Trojan was the latest malware to hit Apple Mac machines running OS X. It ultimately led to Apple removing the "virus-free" slogan from its Web site and marketing strategy after the highly publicized malware attack. More than 600,000 Macs were understood to have been infected by unknowingly installing the Adobe Flash-lookalike software.
The malware was designed to pilfer user passwords and other data through the Web browser and other applications, such as Skype. Perhaps more worryingly, some users may find that the rogue software installs itself automatically without any user intervention at all.
It was bound to happen; five years ago there was practically no malware for the Mac platform due to its all-but non-existent market share. As the Mac becomes more popular, it is increasingly becoming a target for hackers and data thieves.
Middle East gets Flame'd in cyberwarfare, round two
Not so long after Stuxnet was discovered in June 2010, another round of cyberwarfare attacks began in the Middle East. Dubbed "Flame" by the malware finder Kaspersky Lab, due to fragments of code noting the word in the source code, the sophisticated malware was about twenty-times the size of Stuxnet in file size and just as, if not even more dangerous.
It was thought to be targeting machines in Iran, the Palestinian-controlled West Bank, Sudan, Syria, and others in the region, and was far more sophisticated than Stuxnet in a number of ways. However, instead of targeting the physical infrastructure attached to the network, it was designed to steal data and collect audio and video content from webcams and microphones.
It was an intelligence-gathering piece of malware and clearly developed by a state-actor or government. But who exactly remain a mystery still.
Russia enacts Internet blacklist law
Soon after the Russian president Vladimir Putin was elected for another term, the Internet was high up on his agenda, including how to prevent ordinary people from rebelling by seeing dissidents' and protesters' Web sites, among other things.
It was designed as a Web blocking bill -- pornography, drug references and "extremist ideas," but it was ill defined and poorly written and could have given the Kremlin wide-ranging powers to block out vast swathes of the Russian Web. It was, in effect, no different from the U.K.'s Digital Economy Act or the SOPA bill that went before the U.S. House earlier in the year.
Ultimately it was passed by the country's Duma but with a number of clarifications and changes that allowed certain content to be blocked, but ultimately "harmful content" was defined properly in the act following widespread criticism that the ambiguous wording would give the judiciary and government powers that could block sites that it found politically undesirable.
DNSChanger, the 'Internet Armageddon': A busted flush?
DNSChanger was a worry for many, after the malware infected more than 45,000 machines around the world. It changed DNS settings on the infected computer in order to serve up adverts, which would then revenue for the malware writers. Though U.S. federal regulators discovered the malware, it was not immediately shut down. The whole thing had a 'Y2K feel' to it, meaning many would suddenly lose access to the Web once the malware network was shut down.
The FBI kept the machines going for a while so there would be no abrupt halt to Web access by those who were infected. Even social network Facebook and search giant Google notified users visiting their sites if they were infected with the malware. But once the FBI shut down the servers after months of warning, it turned out to be a "disaster" waiting to happen that never actually was.
It wasn't "Internet Armageddon," rather just a bad hair day for a few thousand.
Malaysia's answer to SOPA
You can probably see a running trend here. First SOPA and PIPA, then CISPA, and across the pond and past Europe we had the Russian blacklist. And it didn't stop there.
In Malaysia, a new amendment to the Malaysian Evidence Act, dubbed 114A, would mean Web site administrators, Web hosting providers, Internet providers, and those who own a computer or mobile device "on which [content] was posted" would be held accountable for any "illicit" material -- such as defamatory, seditious, or libelous content -- posted online. What if someone steals your smartphone and posted something 'grossly offensive'? The phone owner would be liable. It wasn't fair and people rightfully became angry.
There were claims that the Malaysian government wanted to bring out the new amendments to help silence political opponents during the upcoming election. However, the government denied this. The Internet blacked out in Malaysia just as it did around the world earlier in the year to protest the changes.
Wikileaks discovers 'global spy ring' that wasn't
As part of The Global Intelligence Files released by Wikileaks, the TrapWire system was uncovered. Nobody quite knew what it was, but it was dubbed a "global surveillance system" that could monitor potentially almost anyone at any given time.
In short, the potential for abuse was huge and it became a global concern for ordinary citizens over the course of the week the news came out and more information about the system became available by the whistleblowing organization. However, it wasn't actually as scary as people thought.
It was developed and maintained by a private company and owned by a mysterious parent company -- ergo the two companies avoided public scrutiny and accountability -- but used by other private industry firms along with various governments on both sides of the Atlantic.
However, it turned a lot of the information was the chief executive and other executives boasting about the system's capabilities, which were vastly overblown and overrated at the best of times. The controversy became somewhat of a dud, but it gave a valuable insight into what governments attempt to (and often succeed at) find out about us as ordinary people.
Philippines next in the cybersecurity legislative line
And next, as if you thought there couldn't be any more in terms of cybersecurity and cybercrime legislation, the Philippines was next to crack down on Internet freedom in the country.
Signed into law in September by the country's president, it aims to combat pornography, hacking, identity theft and spamming after the country's law enforcement agencies complained that it did not have the legal or practical tools to combat the rapidly rising rate of cybercrime.
In a statement by the president's spokesperson, the law was defended: "The Cybercrime Act sought to attach responsibilities in cyberspace… freedom of expression is always recognized but freedom of expression is not absolute," showing just where the government's priorities are. Hackers in protest of the law defaced many government Web sites in the process.
However, after only one month, the country's Supreme Court suspended the law while it was determined if it violates civil rights.
White House network breach
Another day, another attempt on the President's networks -- but in this case, the hackers got through. Don't worry: no damage was done and thankfully the network that was broken into was an unclassified network with no sensitive material up for grabs -- even if the attack was aimed at the White House Military Office, home of the so-called "nuclear football," that carries the codes to the U.S. government's nuclear arsenal.
Thankfully, no classified or secret materials were taken. What caught out the home of U.S. politics was "spear phishing," where an email attachment laden with malware was sent to a specific target, in the hope that malware would be installed on the computer allowing in a backdoor to the network. If it makes you feel any better, the vast majority of highly sensitive material are sent over classified networks that aren't even connected to the wider Web, making breaches like this almost impossible.
Global regulators shut down PC 'tech support' scam
Some good news if you've ever received a call from some random guy claiming to be from Microsoft, and also claiming that you have malware on your computer -- even though you inexplicably own a Mac. They don't know that, but they're trying to sell you fake antivirus programs that you likely don't even need in order to make a quick buck.
U.S. officials, working alongside Canadian, Australian, New Zealand, Irish, and British regulators and authorities cracked the so-called "tech support scam" and frozen financial assets.
It was a coup for cyberscammers worldwide who plagued the vulnerable -- and everyone else for that matter -- with cold calls claiming they were someone that they were not. Thankfully not everyone fell for the scam, but tens of thousands clearly did.
EU officials hacked during conference visit
EU officials were hacked during a conference in Azerbaijan, said European Commission vice-president Neelie Kroes in a blog post. According to Kroes' spokesperson Ryan Heath, the attack took place while they were at their hotel, and were subsequently warned by Apple after the technology giant said an "unauthorized party" might have accessed their computers.
It's not clear who may have been behind the attack, but Heath "[presumed] it was some kind of surveillance," to see what the officials were up to. Kroes was speaking at a conference in Baku, the country's capital, where she was particularly critical of her guests, after claiming the government "[violates] the privacy of journalists and their sources."
"So much for openness," she wrote.