Don't hand over your own personal WikiLeaks to Strangers

I have a dark sense of humor. But, then I started thinking about it. Yes, it's funny that even people who should know better flunk at information security 101, but he's far from alone. As I talked with my fellow journalists, I heard story after story of people getting review PCs, smartphones, and the like with all the previous user's information still intact.
Don't start feeling smug though about how smarty-pants journalists aren't really that smart. I called a couple of local computer recyclers, and they told me that 70% of the old PCs they get arrive at their door with the previous user's personal and business data just sitting there.
Whoops.
I find it more than a little ironic that no matter how excited we can get about online privacy on Facebook, Wi-Fi security; or Web browser history sniffing, most of us are, well, dumb, when it comes to our own hardware.
For example, when you got rid of your last PC, did you burn out all your data on the disk? Did you even bother to delete the files? According to my friends in the PC recycling business, the overwhelming majority of you don't.
Come on people, if you want to make sure your credit-card numbers don't go missing, don't just hand them over to people on your old hard drive! We're just lucky people seem to be more honest than we give them credit for, because we're certainly handing over our data to strangers every day.
It's not hard to blast your data off a PC. Simply deleting files and directories won't do the job. With normal deletion techniques, your files are still there waiting for someone with any decent un-delete tool.
Serious file deletion and disk clean-up programs, like Darik's Boot And Nuke (DBAN) will do the job. DBAN is an open-source program that you download and burn to a CD or DVD. Then, all you need do is boot it up, and it will delete not only last file on your disk but all the "vacant" space between files, A computer forensics lab will be able to restore your data, but no one else will.
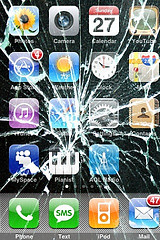
It's a little harder to securely delete the data on a smartphone, but it can be done. Each phone has its own way to perform a "factory wipe." This is also known as a hard reset. Be darn sure you've saved off your personal data before doing this, because you're not getting the data back after you've wiped a phone.
For Android 2.x phones, the generic way to do this is:
Menu > Settings > Privacy > Factory data reset.
On a BlackBerry, it's:
Options > Security Options > General Settings. Hit your BlackBerry Menu key > Wipe Handheld
With an iPhone, you do it with:
Settings > General > Reset > Erase All Content & Settings
If your phone's display doesn't look like what I describe, don't take my word for it. Smartphones and mobile operating system are constantly changing. Instead, check with your phone's support Web site and search for "factory wipe" or "hard reset" and follow their instructions.
You'll also need to zap the data separately on your old phone's Secure Digital (SD) or SDHC (Secure Digital High Capacity) card. Some systems will give you an option to do this. With others you'll need to attach your phone to your PC and mount the drive and erase it. You can also take the SD out of the phone, put in your PC, and format it.
That still isn't going to stop anyone who swipes your laptop or smartphone from getting your data. Preventing that is a story for another day. If you make the effort to really clear out your drives though at least you won't be handing over your data to your computer or phone's next owner.