Google blacklists 11,000 WordPress sites amid malware campaign

More than 11,000 domains have been blacklisted by Google as malicious after a malware campaign compromised sites using the WordPress content management system.
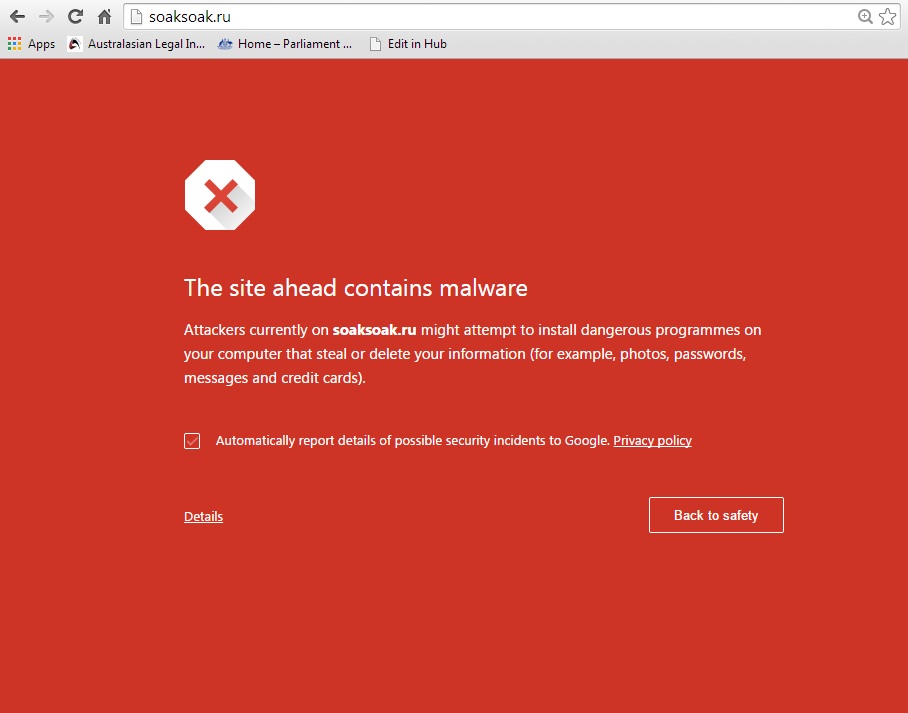
The campaign, dubbed SoakSoak after the first domain used in the malware redirection path soaksoak.ru, has potentially compromised over 100,000 WordPress sites, according to website security company Sucuri.
Sucuri, which disclosed the malware campaign over the weekend, confirmed on December 15 that the malware attack vector is the RevSlider plugin for WordPress.
"The biggest issue is that the RevSlider plugin is a premium plugin, it's not something everyone can easily upgrade, and that in itself becomes a disaster for website owner," said Sucuri's Daniel Cid in a blog post on December 15. "Some website owners don't even know they have it, as it's been packaged and bundled into their themes. We're currently remediating thousands of sites, and when engaging with our clients, many had no idea the plugin was even within their environment."
The company was notified of a serious vulnerability in the premium drag-and-drop plugin in early September, at the time saying that the vulnerability had already been publicly disclosed via some underground forums.
"In this situation, a very popular plugin developer decided it was best not to disclose to anyone, in return patching silently," said Cid in a post at the time. "Mind you, this vulnerability was already disclosed as a Zero Day via underground forums, which you would have thought would incentivise a developer to work quickly and disclose even faster. No, instead a different course of action was taken."
Two months prior to Cid's post, the vulnerability in the Slider Revolution Premium plugin had been publicly disclosed, along with a proof of concept showing how a remote attacker could steal the database credentials and compromise the website via the database.
"This type of vulnerability is known as a Local File Inclusion (LFI) attack. The attacker is able to access, review, download a local file on the server," said Cid. "This, in case you're wondering, is a very serious vulnerability that should have been addressed immediately."
Sucuri estimates that the number of WordPress websites impacted by in-the-wild attacks using the vulnerability could be in the hundreds of thousands, with the company offering the use of its free SiteCheck scanner for infection detection.
The SoakSoak malware campaign is making use of a number of new backdoor payloads, according to Sucuri, some of which are being injected into images to further assist evasion, with others being used to inject new administrator users into the WordPress installs, opening the potential for even more control over the long term.
"Some users are clearing infections and getting reinfected within minutes, and the reason is because of the complex nature of the payloads and improper cleaning efforts," Cid said in his latest post.
Cid said the use of a website firewall would help reduce the potential for attack by the malware.
Sucuri has previously said that since May this year, it has discovered critical WordPress plugin vulnerabilities affecting four plugins that have nearly 20 million downloads.
The company said it has found serious security holes in WordPress plugins WPTouch (5,670,626 downloads), Disqus (1,400,003 downloads), All In One SEO Pack (19,152,355 downloads), and MailPoet Newsletters (1,894,474 downloads).