Google: Spam volume for Q1 back to pre-McColo levels
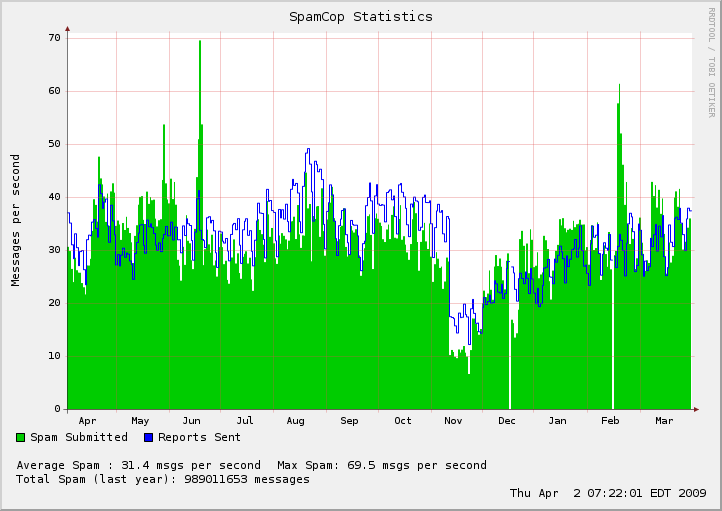
According to Google's Postini Spam data and trends for Q1 2009, during the first quarter of the year the spam volume was the strongest since 2008, increasing with an average of 1.2% per day. Data from Cisco's IronPort and Symantec's Messagelabs confirms the trend.
Spammers have recovered from the McColo shutdown - it's a fact. But with Conficker in a standby mode, it's worth discussing the (mini) botnets currently responsible for the increasing spam volume, and how have spammers adapted in order to improve their resilience to potential attempts to shut down their operations.
According to Marshal's TRACE team, the resurrection of the Rustock botnet accounted for 35% of all the spam they were monitoring in March, with the Mega-D botnet once again topping the chart of spambots. And even though these are the "usual suspects" that migrated to alternative cybercrime-friendly ISPs, partitioned botnets usually remain beneath the radar, to form the foundation for the growing use of managed spam services consisting of a relatively small number of infected hosts.
Spammers are also game changers. For instance, on their way to exploit the trust hierarchy among legitimate email service providers -- think DomainKeys -- vendors of spamming services have looking for ways to become DomainKeys verified spammers since early 2008. With two frameworks currently offered as a managed service, sooner or later spammers will be able to start taking advantage of spam platforms on the basis of legitimate infrastructure. With the efficient abuse of CAPTCHA authentication thanks to outsourcing the process, hundreds of thousands of bogus email accounts at legitimate email service providers are being automatically abused for the purposely of sending spam (Spam coming from free email providers increasing; Gmail, Yahoo and Hotmail systematically abused by spammers).
With decentralization of command and control locations/communications, and standartization of the spamming process with quality assurance in mind in the face of managed spam services, spam, in between the rest of the malicious activities streaming from the infected hosts, are not going away. Interestingly, despite the fact that the money made from spam look like pocket change compared to the money made from rogue security software and the process of monetizing the botnet by partitioning it (Into the Srizbi's botnet business model; Money Mule Recruiters use ASProx's Fast Fluxing Services) cybercriminals won't given up on their equally distributed revenue stream.