Have a heart (attack): Defibrillators, pacemakers vulnerable to hackers

Researchers have discovered that an implantable heart device, a combination of a defibrillator and pacemaker, is vulnerable to hackers.
According to a study, authored by researchers at the University of Washington, University of Massachusetts Amherst and Harvard Medical School, hackers could get wireless access to a heart device and shut it down (a power denial of service attack) or deliver jolts of electricity. In either case, it wouldn't be fun for whoever had the pacemaker.
While this hack isn't likely given that the New York Times reports you need $30,000 worth of gear to make it happen it does raise a few eyebrows.
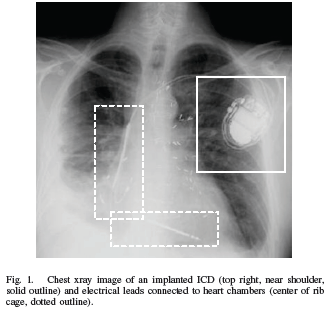
Our study analyzes the security and privacy properties of an implantable cardioverter defibrillator (ICD). Introduced to the U.S. market in 2003, this model of ICD includes pacemaker technology and is designed to communicate wirelessly with a nearby external programmer in the 175 kHz frequency range. After partially reverse-engineering the ICD's communications protocol with an oscilloscope and a software radio, we implemented several software radio-based attacks that could compromise patient safety and patient privacy. Motivated by our desire to improve patient safety, and mindful of conventional trade-offs between security and power consumption for resource constrained devices, we introduce three new zero-power defenses based on RF power harvesting. Two of these defenses are humancentric, bringing patients into the loop with respect to the security and privacy of their implantable medical devices (IMDs). Our contributions provide a scientific baseline for understanding the potential security and privacy risks of current and future IMDs, and introduce human-perceptible and zero-power mitigation techniques that address those risks. To the best of our knowledge, this paper is the first in our community to use general-purpose software radios to analyze and attack previously unknown radio communications protocols.
The researchers say that these attacks would also be possible in any implantable device such as a drug pump and neurostimulator that can be programmed from outside the body. To simulate a pacemaker in a human, researchers put the device into a bag of bacon and ground beef.
In an FAQ on the study researchers note:
We only studied a single implantable medical device. We currently have no reason to believe that any other implantable devices are any more or less secure or private.
The study doesn't describe specific attack vectors since hacking implantable medical devices is obviously a sensitive issue. In other words, researchers wanted to prove a theory without giving nut jobs any ideas. The study does note that buffer overflow attacks and insecure software updates are possible. Think patch day for your pacemaker.
However, these hacks don't necessarily have to kill. You can just swipe critical medical information. Here are some of the possibilities:
There are two primary hacking techniques in the study (the report has much more detail):
The researchers reverse engineered wireless transmissions.
We began by capturing RF transmissions around 175 kHz. Using an oscilloscope, we were trivially able to identify transmissions from our ICD and the commercial ICD programmer. We saved traces from both the oscilloscope and the USRP. We processed these RF traces in software (using Matlab and the GNU Radio toolchain) to recover symbols, then bits. Finally, by analyzing these bits we discovered key aspects of the ICD's protocols and the data that it and the programmer transmit.
Eavesdropping via commodity software.
We built an eavesdropper using the Universal Software Radio Peripheral (USRP) in concert with the open source GNU Radio libraries. For the initial analysis in Section III-A, we simply used programs included with GNU Radio to capture and store received radio signals, then wrote code in Matlab and Perl to analyze those signals. To eavesdrop in real time, we integrated the necessary functions back into the C++ and Python framework of GNU Radio. This section describes the eavesdropping process in detail and shows the results of our passive attacks.
As for defenses, researchers note that nothing is perfect. For instance, just using a cryptographic key (think WEP key for your pacemaker) would raise its own issues. According to the study:
Providing security and privacy on an IMD involves health risk factors and tight resource constraints. Traditional approaches could potentially introduce new hazards to patient safety. For instance, protecting an IMD with a cryptographic key may provide security, but the unavailability of a key could hinder treatment in emergency situations. Another risk to IMD availability is excessive power consumption by mechanisms other than those needed for the device's primary function. For instance, the energy cost of performing computation for cryptography or radio communication could directly compete with the energy demands of pacing and defibrillation. Effective mechanisms for security and privacy should not provide new avenues for an unauthorized person to drain a device's battery. For instance, spurious wake-ups or a cryptographic authentication process itself could cause a device to enter a state that consumes excessive amounts of energy.
However, there are a few potential defenses, but they are experimental. Two key characteristics are that the defenses can't drain power or introduce other points of failure. After all, I'd rather have a pacemaker work than be able to fend off a hacker.