Researchers find 12 zero day flaws, targeting 5 web malware exploitation kits
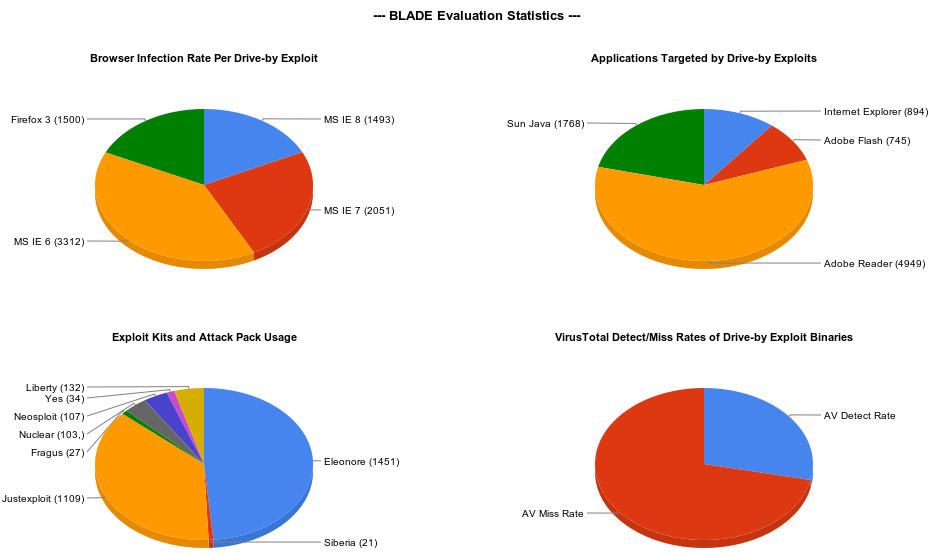
Security researchers from TEHTRI-Security, have found twelve zero day flaws targeting five of the most common web malware exploitation kits such as Neon, Eleonore, Liberty, Lucky and the Yes exploitation kits.
The use of these flaws could lead to hijacking of the admin panel, retrieving the admin password, or injecting content within the panel, potentially not just disrupting the campaign, but exposing the person behind it, or at least offering invaluable clues.
More details:
According to the group, some of the most widely used exploitation kits, are susceptible to the following flaws:
- Vuln in NEON Pack. Permanent XSS+XSRF. - Vuln in NEON Pack. SQL Injection. - Vuln in YES Pack. Remote File Disclosure. - Vuln in YES Pack. Permanent XSS+XSRF admin. - Vuln in YES Pack. Remote SQL Injection. - Vuln in Lucky Sploit Pack. Remote control. - Vuln in Liberty Pack. Permanent XSS+XSRF. - Vuln in Liberty Pack. SQL Injection. - Vuln in Eleonore Pack. Another SQL Inject. - Vuln in Eleonore Pack. XSRF in admin panel. - Vuln in Eleonore Pack. Permanent XSS. - Vuln in Eleonore Pack. Remote SQL Inject.
These offensive tactics against cybercriminal are in fact nothing new. However, guess who pioneered the practice first? The cybercriminals themselves, allocating time and resources to finding remotely exploitable flaws within popular malware/web malware exploitation kits.
- Related posts: Pinch Vulnerable to Remotely Exploitable Flaw; Help! Someone Hijacked my 100k+ Zeus Botnet!; Firepack remote command execution exploit that leverages admin/ref.php; The Zeus Crimeware Kit Vulnerable to Remotely Exploitable Flaw; Cybercriminals release Christmas themed web malware exploitation kit; The Neosploit cybercrime group abandons its web malware exploitation kit
Back in March, 2010, security researchers at the Vienna University of Technology, were able to easily extract 33GB of raw crimeware data, following a simple methodology - the lack of OPSEC (operational security) on the command and control servers responsible for maintaining the ZeuS crimeware campaigns.
And although they were surprised to find out how easily they could extract the data of the affected customers, they also admitted that it's fairly logical to assume that the cybercriminals are doing exactly the same against each other.
Basically, the service:
creates a trusted and effective mechanism for participating researchers to report stolen account credentials discovered online – such as username and password log-in information for online services or compromised credit card numbers – to the appropriate institution responsible for that account. Through a centralized alerting system powered by Microsoft technology developed specifically for this program, Internet Fraud Alert will quickly inform companies about compromised credentials, allowing them to take the appropriate action to protect their customers.
The current tactical advantage of the security community, is the fact that not all cybercriminals are willing to invest money into purchasing the latest exploitation kit/ZeuS crimeware versions. Which, just as we see from the perspective of the legitimate user (Does software piracy lead to higher malware infection rates?), creates a lot of exploitation points.
What do you think? Has to the time come to go offensive against cybercriminals on a large scale, by exploiting the very same exploitation kits that help them infect hundreds of thousands of people every day?
What should be the main emphasis of the practice? Tracking them down, or contributing to the growth of services such as the Internet Fraud Service Alert, leading to timely response to cybercrime incidents affecting the customers of the companies, participating in the project?
Talkback.