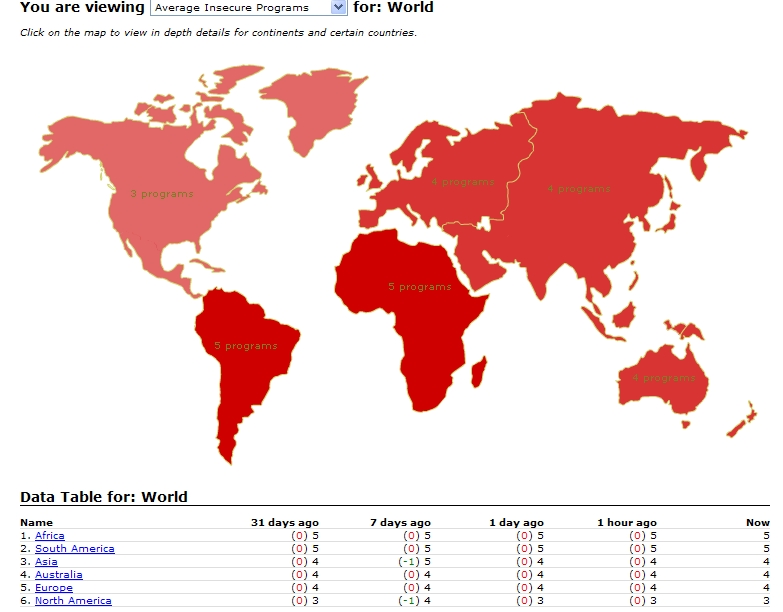
Secunia: Average insecure program per PC rate remains high
The WorldMap of patched and unpatched PCs is released prior to an updated version of Secunia's Personal Software Inspector, with the latest version finally filling a niche left open potentially undermining the usefulness of the handy tool in general - measuring the exploitability of cross-browser plugins such as Adobe Flash Player, QuickTime, or Sun's Java.
Let's take a look at some of their stats.
The fact that US based PC users have more than 2.7 billion vulnerable programs installed are shocking! And quite frankly I am very surprised, we had an idea it would be bad, but couldn't imagine the enormous scope of this problem. And to make things even worse, the picture formed in the US is the same all over the world. PC users need to patch! They need to patch all their vulnerable programs and they need to do so as fast as possible after the patch has been issued from the vendor. Failing to do so is playing Russian Roulette with your IT security – it is only a question about time – and luck – when your system will be compromised.
Despite the fact that according to Secunia's WorldMap there are countries like Burkina Faso with 20 insecure programs per PC, or Cuba with 15, it only takes a single unpatched application or a browser plugin in order for the cybercriminal to successfully exploit the host on-the-fly through a mix of popular exploits (Cybercriminals release Christmas themed web malware exploitation kit) embedded within a particular kit.
Prior to the official announcement of PSI 1.5, Secunia stated that "patching is more important than having an Anti-Virus program and a personal firewall."
What do you think? Talkback.