Transmitter.C mobile malware spreading in the wild
NetQuin's CEO, Dr. Lin Yu provides more insight into the nature of the malware, its financial implications for the infected user, as well as thoughts on the future of mobile malware.
Go through the Q&A.
Dancho: What are some of the characteristics of Transmitter.C?
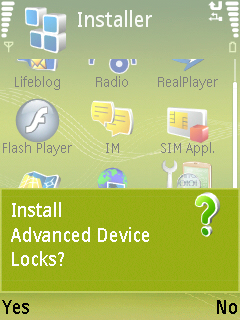
Dr. Lin Yu: As a foreign variant of previous erotic short message virus (Transmitter.A), this virus camouflages in a normal third party mobile phone software " Advanced device locks" to inveigle the users to install it.
After installation, this virus will be automatically started up. Just a minute, it will automatically access network for about 3 minutes. Later, this virus will send short messages externally at interval of 10 - 15 seconds. As can be observed from the communication record, there are large amount of records of sending short messages, all the numbers to which short messages are sent are strange numbers, but it is completely impossible to find the record of short messages that have been sent in the Sent Box.
This virus will run away with user's tariff by sending out short messages at such high frequency. In addition, it is very likely that this virus forcibly subscribes some services for the users, thus consuming user's tariff.
Furthermore, this virus has transmissibility. In the form of obscene short messages, it will inveigle the users to click the links in the contents of short messages. Upon clicking such links, a user will download virus to his/her mobile phone, becoming the next virus-spreader. In addition, this virus can also transmitted in the form of legitimate third party software that is put in the Website and Forum for downloading mobile phone software.
- Go through related mobile malware posts: Attacks on NFC mobile phones demonstrated; New mobile malware silently transfers account credit; New Symbian-based mobile worm circulating in the wild
Dancho: How is Transimitter.C different than any other Symbian malware?
Dr. Lin Yu: As compared with the Symbian malicious software formerly discovered, Transimitter.C has even stronger transmissibility and harmfulness: It not only has the corresponding server end for coordination, but can also be dynamically adapted to the current language of mobile phone and thus send short messages to address lists and strange numbers in different languages Furthermore, utilizing obscene short messages with links, it can inveigle the users to click it for installation. If this virus has been transmitted to mobile phones, it will bring tremendous economic loss and reputation crisis to the users.
Next -->
Dr. Lin Yu: Yes. This virus can camouflage as legitimate software for transmission. Camouflage mode: The executable body of virus attaches at normal software to inveigle the users to install it.
Dancho: Are the malware authors attempting to somehow monetize the campaign and earn profit in the process, or is Transmitter.C basically a proof of concept that can only result in huge phone bills due to the short time interval between sending the SMS messages?
Dr. Lin Yu: This malicious software is designed to realize the object of making commercial profit. Transimitter.C has promoted some malicious links. Very likely, it forcibly subscribes some services for the users, thus consuming the tariff of users; These malicious links may induce a user to download virus to his/her mobile phone, so that this user will become the next virus-spreader.
Dancho: How would you describe the current state of mobile malware? Is the inevitable growth of the micro-payment market prone to increase cybercriminal's interest in mobile malware, or would they go after the intellectual property data stored on the smart devices?
In our opinion, with the intellectualization of mobile phones and the increase in network bandwidth, there will be more and more mobile phone malicious software and their routes of transmission. Furthermore, because many users have get accustomed to saving their privacy information such as bank account, address list and photograph and their mobile phones have payment function, the mobile phone malicious software will generate much more hazards than computer malicious software.
According to the study on the viruses we have captured, most of mobile phone malicious software are still mainly designed to consume the tariff of users by means of automatic networking and automatic transmission of malicious short messages for fee reduction. In addition, few malicious software have turned to steal the privacy information of users. In particular, the privacy information in the users' mobile phones (short message, address list and picture etc.) will become the main targets of attack by malicious software and will be likely transmitted in the modes of short messages and networking, resulting in the disclosure of user's privacy.