Vista passes one security test

Does the multi-layered security protection in Windows Vista work? As I pointed out yesterday, we won't have a definitive answer to that question until months after Vista is officially released. But one current exploit offers reason to be encouraged.
Security experts are buzzing over a zero-day exploit in Internet Explorer that allows an attacker to plant spyware on your computer if you visit a webpage that contains the exploit code, which takes advantage of a vulnerability in the VML Rendering engine. There are workarounds, but so far no official patch is available from Microsoft.
But what happens if you're running Internet Explorer 7 on Windows Vista? To see for myself, I logged on as a member of the Administrators group and used IE7 to visit a test site that hosts a harmless demonstration of the exploit code (courtesy of fellow ZDNet blogger Adrian Kingsley-Hughes). Here's what happened next:
First, the page refused to load, displaying a security warning that the page is attempting to call a previously installed ActiveX control. This is the so-called ActiveX opt-in feature, designed to prevent pages from exploiting newly discovered flaws in obscure controls that had been previously assumed to be safe.
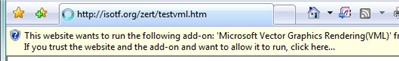
I could have stopped right there. But instead I clicked the Infobar to tell IE7 it was OK to load the control. I got another warning dialog box.
I clicked Run in response to that warning as well, and finally reached a page that triggered this dialog box, in which the third party hosting the test confirmed that the exploit had failed to execute on my machine.
Now, it's important to note that the developers of IE7 clearly had no idea that this vulnerability existed in IE6. But their development process managed to block this particular exploit right out of the box, and the additional layers of security provided important clues that this page was potentially dangerous.
The initial security warnings are hardly perfect. I've seen similar ActiveX opt-in dialog boxes for other built-in ActiveX components. How is an unsuspecting user supposed to know which one is safe and which is dangerous? And the list doesn't work on a per-site basis. If I had visited a site that legitimately used the VML control last week, before this exploit hit the news, I would probably have approved it. And once I had done that, it would have been on the safe list for good. There's no way to undo that decision, as far I can tell. Once you tell IE7 that an installed control is OK, any site can try to use it.
Still, the cumulative effect of these changes is encouraging.
Update 22-Sep 2:15PM PDT: Dwight Silverman has a related story. Did Windows Vista's most irritating feature save my butt?