Australian control systems exposed online

Several Australian businesses have been exposing their building management systems online, allowing anyone to view information such as the temperature in their office or even whether the exhaust fan in the toilet is running.
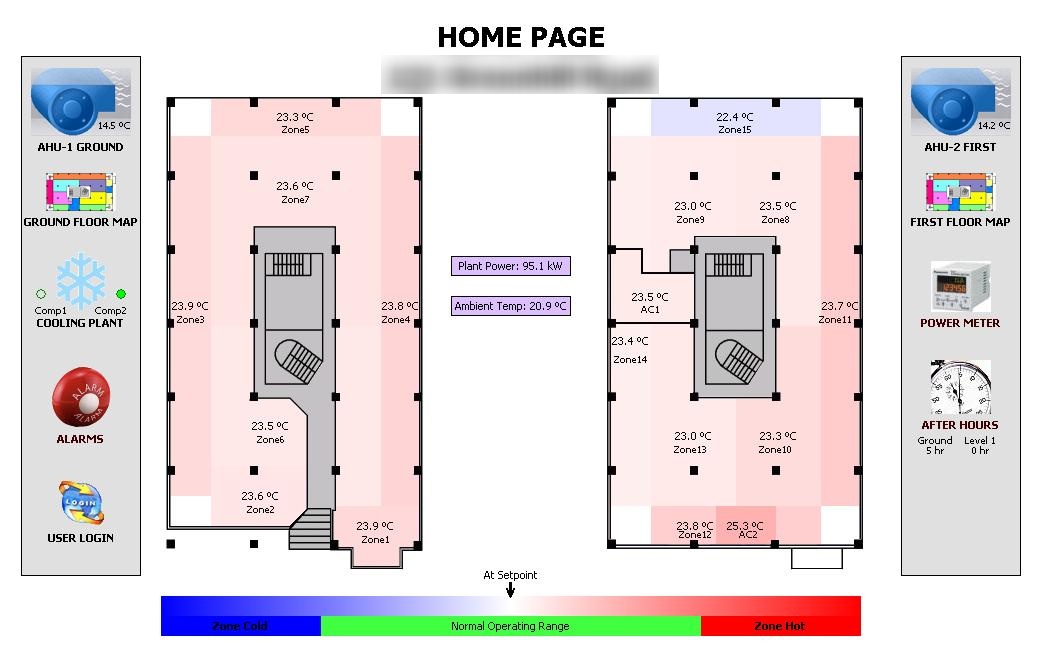
(Screenshot by Michael Lee/ZDNet Australia)
The information comes after Twitter user @ntisec discovered that a simple Google search for part of the URL used by Tridium's building management system (BMS) software called Niagara resulted in a large listing of open systems. He posted his findings to Pastebin, stating that there were simply too many to go through. These included a private branch of a well-known auditing, consulting and financial advisory company, a South Australian hotel, and a large Australian concrete company.
Further searches made by ZDNet Australia revealed even more Australian businesses that had their BMS interface exposed to the web.
These systems required no username or password to access and allowed any member of the public to view information such as floor plans, the temperature in buildings or rooms, scheduled start and stop times for equipment, the state of equipment, and even detailed graphs of room temperatures or equipment use.
In one case, the information provided was detailed enough to make it simple to deduce that someone in a particular office, on a particular floor, regularly came in for a half day on the weekend.
(Screenshot by Michael Lee/ZDNet Australia)
ZDNet Australia contacted two of the contractors that were responsible for the BMS installation at one of the vulnerable sites.
Building Automation Controls manager and director, Rick Manser, said that it is not normal policy for them to allow the public to view BMS information, but a guest account to view information was sometimes requested or enabled retrospectively by its customers.
He said that the BMS software ships with its guest account disabled by default, preventing others from viewing BMS information, meaning that someone must have made the conscious decision to open the information to the web. Although the few systems that ZDNet Australia viewed appeared to be read only, Manser said that administrators could also change the permissions given to the guest account, effectively giving them the ability to not only view information, but to make remote changes as well.
Another contractor who wished not to be named said that their company always asked customers whether they wanted the systems to be made available online, but ultimately, security considerations were the customer's responsibility.
If remote administration were enabled they would allow a user to make simple nuisance changes to room temperatures or shut down equipment completely, but depending on what the building is used for or what systems are connected, this could cause greater damage. The humidity within a museum, for example, could be maliciously altered to destroy millions of dollars worth of artworks.
Both contractors agreed that a better method of implementing the remote monitoring systems would be to require users to connect via a Virtual Private Network, which would have prevented the exposure of sensitive information.
Other organisations using Tridium's BMS include CSIRO Hobart, Tasmanian Ambulance and the Adelaide Commonwealth Law Courts, but these aren't necessarily at risk unless building managers have explicitly decided to make the BMS back-end available online.