When will Apple patch the Lion flaw that stores passwords in clear text?

There's a major security bug in the currently shipping version of OS X Lion (10.7.3). ZDNET's own Emil Protalinski and Ed Bott exposed it after it was first reported by security researcher David Emery on the Cryptome mailing list.
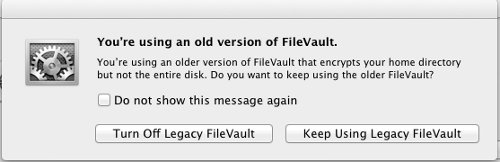
Users of Apple's FileVault encryption that upgraded from Snow Leopard to OS X Lion update 10.7.3 (build 11D50) were apparently victimized by a piece of errant code that turned on a system-wide debug log file containing the login passwords of every user that logged in since the update was applied -- stored in clear text.
The log file in question is accessible outside of the encrypted area giving anyone with administrator or root access the user credentials for an entire encrypted partition. And it gets worse. Even if you're not an admin or root user, all it takes is physical access to the machine and the data's up for grabs. You can also access the log file via FireWire Disk Mode and read the encrypted partition.
Whoops.
Protalinski writes:
Anyone who used FileVault encryption on their Mac prior to Lion, upgraded to Lion, but kept the folders encrypted using the legacy version of FileVault is vulnerable. FileVault 2 (whole disk encryption) is unaffected.
Sophos' Chester Wisniewski writes:
Vulnerable users who do not encrypt their Time Machine backups risk replicating this log file to their backups, which could mean long-term storage of their unencrypted password.
The worst part? The bug was also mentioned on the Apple Support Communities exactly three months ago and was never addressed.
If you're concerned about the bug you can contact: product-security@apple.com. The only fix as of now is to perform a full disk encryption using Apple's FileVault 2 and purge all backups of the vulnerable partition.
Apple: you're on the clock.
Update: Dave Emery explains that it's trivial to test to see if Apple fixed the flaw in OS X 10.7.4 build 11E53 which was released to Apple developers on May 1 if you have a legacy FileVault partition. Lion doesn't directly allow you to create a new FV1 partition in the GUI, although you can do so by hand.
If you have a FV1 partition and feel like testing it, here are the steps. Email me a screenshot of your results and I'll add them to this post.
- Install Snow Leopard on a spare hard drive and allow it to fully update from Apple.
- Using Snow Leopard, activate Filevault on a test account and choose some unique unusual password for the account. This should create a Filevault legacy partition for that account and the associated sparsebundle file.
- Use the Lion installer to install 10.7.3 on the test hard drive upgrading the Snow Leopard to 10.7.3 and preserving the test user legacy Filevault partition - you may be asked if you want to do this.
- Log in and out to the test account a few times...
- Then using terminal (eg a unix shell) grep for the unusual password string in the files in /var/log... (eg grep unusualpassword /var/log/*)
- You should find your unusual password string in one of the files there...
- Upgrade the 10.7.3 to prerelease 10.7.4
- Try the same thing...