All about Infocard

By the end of this month Microsoft's will be releasing a "technical preview" of InfoCard, a new framework for managing identities based on WS-* protocols. Microsoft is also rolling out other related technologies for federation. It's a big deal if the industry can come up with a generally agreed upon, open approach to dealing with the large scale identity management problem. There's a lot of worthwhile reading material to get up to speed on this topic, starting with with various posts and papers on Infocard.
- Microsoft's Vision for an Identity Metasystem [Microsoft]
- The Laws of Identity [Kim Cameron]
- What is Microsoft InfoCard [Johannes Ernst]
- More links at Doc Searls' IT Garage
Bonus material:::
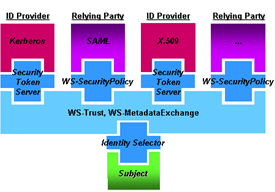
Identity Metasystem Architectural Diagram [Microsoft]
The Laws of Identity
The "Laws of Identity" are intended to codify a set of fundamental principles to which any universally adopted, sustainable identity architecture must conform. The Laws were proposed, debated, and refined through a long-running, open, and continuing dialogue on the Internet. Taken together, the Laws define the architecture of the identity metasystem.
They are:
- User Control and Consent: Identity systems must only reveal information identifying a user with the user's consent.
- Minimal Disclosure for a Constrained Use: The identity system must disclose the least identifying information possible, as this is the most stable, long-term solution.
- Justifiable Parties: Identity systems must be designed so the disclosure of identifying information is limited to parties having a necessary and justifiable place in a given identity relationship.
- Directed Identity: A universal identity system must support both "omni-directional" identifiers for use by public entities and "uni-directional" identifiers for use by private entities, thus facilitating discovery while preventing unnecessary release of correlation handles.
- Pluralism of Operators and Technologies: A universal identity solution must utilize and enable the interoperation of multiple identity technologies run by multiple identity providers.
- Human Integration: Identity systems must define the human user to be a component of the distributed system, integrated through unambiguous human-machine communication mechanisms offering protection against identity attacks.
- Consistent Experience Across Contexts: The unifying identity metasystem must guarantee its users a simple, consistent experience while enabling separation of contexts through multiple operators and technologies.