Black market for zero day vulnerabilities still thriving
Let's take a brief retrospective of the black market for zero day vulnerabilities, and review a recently launched underground shop for zero day vulnerabilities, currently offering 15 zero day vulnerabilities affecting popular web applications in order to execute successful XSS or SQL injection attacks, with prices ranging from $10 to $300.
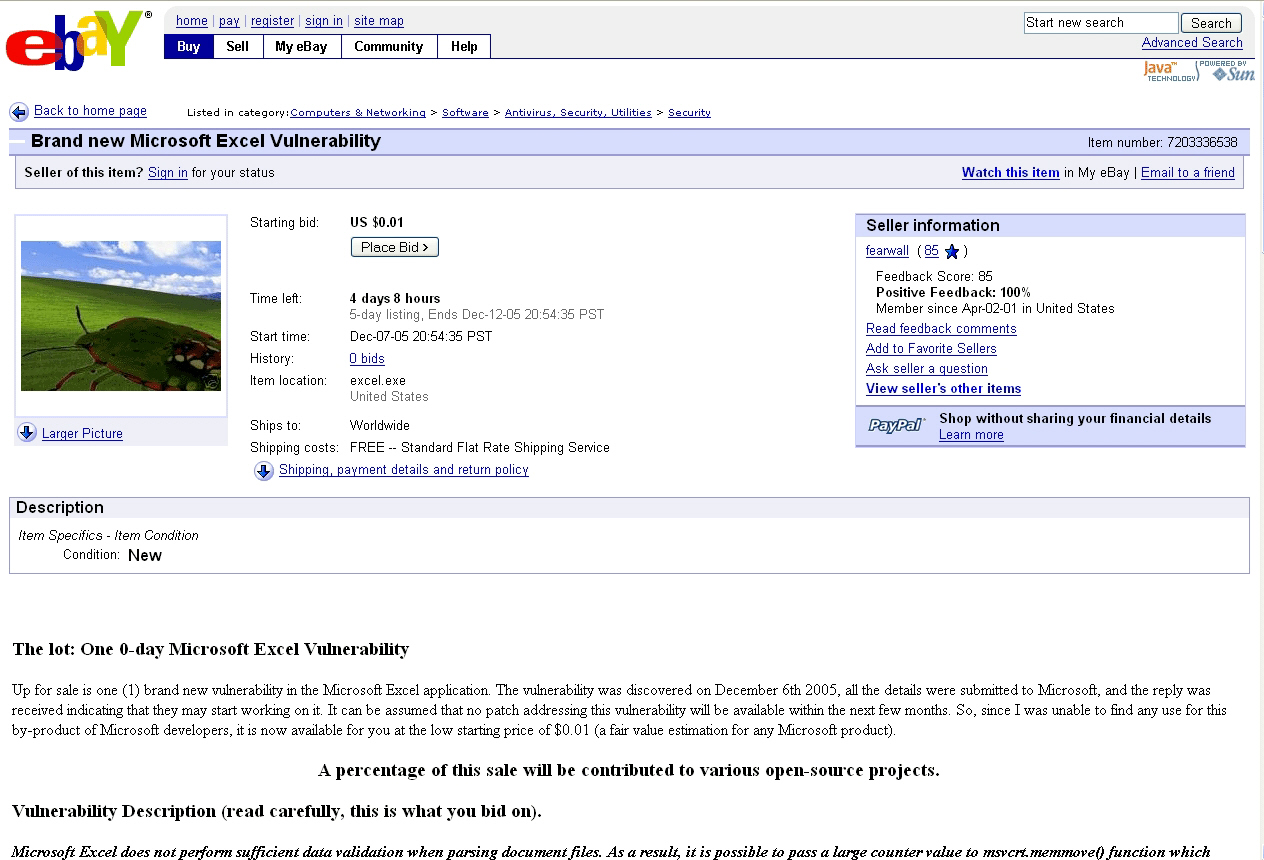
"It seems most likely that the vulnerability was detected by an unnamed person around 1st December 2005, give or take a few days. It took a few days for the exploit enabling random code to be executed on the victim machine to be developed. Around the middle of December, this exploit could be bought from a number of specialized sites. It seems that two or three competing hacker groups from Russian were selling this exploit for $4,000. Interestingly, the groups don't seem to have understood the exact nature of the vulnerability. One of the purchasers of the exploit is involved in the criminal adware/ spyware business, and it seems likely that this was how the exploit became public."
In times when legitimate online auctions for zero day vulnerabilities are admitting that the market model they've introduced is far ahead of its time, their underground alternatives are thriving. Launched in early
Here's a translated introduction to the exploits shop :
"We present you the private exploits shop targeting PHP-applications (Content Management Systems, Guest books, forums, chat rooms, statistics and any other scripts). Our store will be constantly updated so you can expect to find the exploit you were looking for at any given time. If it doesn't you will still be able to request such a vulnerability for a web application of your choice, and our team will provide with you the necessary PoC's and tools to start using it. All exploits are written solely to our command, meaning you're not going to find them anywhere else on the Internet.
Each exploit is accompanied by information on the approximate number of sites running the vulnerable application in Google, the language the exploit is written in, and price. We also have a forum where you can place an order, discuss, complain, express an opinion or ask a question about the exploit purchased. All exploits have a user-friendly Web interface, possibly in the future we'll be releasing win32 console exploits. There are also technical support, patiently waiting for requests from users who have a problem using the exploit. We also conduct audits, security services, tests for entry (this service will be available by the end of August this year).
Watch our virtual merchandise, and if not today perhaps tomorrow you'll find what you're looking for."
As always, you have a pure cybercrime market proposition pitched as a security service. The e-shop is not only offering proof of concept exploits to demonstrate the vulnerabilities, but also, easy to use web based applications for exploitation.
Moreover, this pseudo responsible positioning is flawed right from very beginning since the service administrators have done their homework and are also offering stats from basic search engines reconnaissance -- Google dorks -- so that potential buyers can easily measure the impact of the flaw that they're purchasing. These very same vulnerabilities would later on be abused for blackhat search engine optimization, and injection of malicious scripts redirecting to live exploit serving URLS. Here's their ethical pen-testing pitch :
"Our team is reviewing source code software and finding bugs in the programming, leading to critical consequences and employees of security systems. Thus, we are pleased to offer you the results of their analysis of popular (or little) systems. The results of our study are presented in the form of finished applications in languages php / perl, which aim - to demonstrate the vulnerability of the system to further assist in their neutralization. If you're going to use our software for other purposes than penetration testing, the administration does not take responsibility for your actions.
We also take orders for individual study of your source code, security auditing of servers and sites (penetration tests). Orders for such services are taken at the forum, and the price purely individual and dealt with each customer individually (mainly depends on the number and type of vulnerabilities discovered, as well as the number of code)."
Which products are they targeting? Currently offered zero days affect multiple versions of the following web applications :
- All versions of PHP Fusion - WHMCompleteSolution - PHP Nuke - PunBB - Tiki Wiki - BMForum - Invision Power Board - YaBB - PunBB - e170 Plugin Calendar - vBulletin v3.6 + ICQ Mod - vBulletin v3.6 + GVideo Mod - vBulletin v3.6 + Youtube Mod - vBulletin v3.6 + LJ Mod - Zen Cart
Next to their current inventory, the service is also offering zero day vulnerabilities on demand charging the following prices :
"- Remotely upload shell - $120 - Remote file inclusion on request - $100 - Remote SQL injection - $70 - Passive and Active XSS for $10 and $40 respectively"