ICANN: Anycast saved DNS root servers during attack

During the cross-continent attack, which lasted for about two-and-a-half hours on February 6, unknown attackers used hijacked computers in the Asia-Pacific region to bombard six of the 13 root servers with data measuring a whopping 1Gb per second but, because the targets were using the Anycast technology, end users were not affected.
(NOTE: Data measuring 1Gb per second is roughly equivalent to receiving 13,000 e-mails every second, or over 1.5 million e-mails in just two minutes).
The report is disappointingly sparse on details of the origins or tactics used by the attackers. ICANN confirmed suspicions that zombie machines in South Korea formed the botnet that launched the attack but warned that this is mostly "educated guesswork."
"It could just as easily have come from a number of different countries at the same time. It is even possible that the attack originated from outside the region and many of the Internet addresses that the attack appeared to come from had in fact been "spoofed" or faked, ICANN said. "In fact, engineers are fairly sure that it did come from Asia-Pacific, but even so this does not mean that whoever was behind the attack is based in Asia-Pacific because they could just as easily triggered it from anywhere on the network, i.e., anywhere in the world."
South Korean authorities are already on record as saying that the attack commands were sent from a host server in Coburg, Germany.
Some highlights from the ICANN report:
- At least six root servers were attacked but only two of them were noticeably affected: the "g-root", which is run by the U.S. Department of Defense and is physically based in Ohio, and the "l-root" run by ICANN.
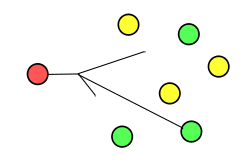
- The reason why these two were particularly badly affected was because they are the only root servers attacked that have yet to install Anycast (a further three root servers without Anycast were not attacked this time).
- The fact that all the root servers have not moved to Anycast was a conscious decision to avoid a single point of failure. There were some concerns that there might be a security risk in allowing a lot of different servers to appear as if they were coming from the same place. And so just a few root servers tried the system first, tested it thoroughly and ironed out any bugs before the next set moved over.
- The operators of the servers that were hit by the attack were aware of it almost instantaneously. Because of the way the attack worked (where a command is given at the same time to a large number of computers to send data to the same place), it arrived like a brick wall, which immediately set off all the alarms built into the networks.
- One possible explanation for the root server attacks is to act as an advertisement for a particular botnet.