Immunity launches exploit for 'unlikely' Windows worm hole

A workable exploit attack for a TCP/IP vulnerability in Microsoft's Windows has been launched into the wild courtesy of security firm Immunity.
On Jan. 17, it became clear that you shouldn't dawdle on deploying Microsoft's MS08-001 patch. That patch, issued Jan. 8, fixed a Transmission Control Protocol/Internet Protocol (TCP/IP) processing vulnerability that was critical for XP and Vista. After security firm Immunity issued a proof of concept, Microsoft acknowledged the vulnerability, but said an attack was "unlikely."
With Microsoft's assessment it basically threw down the gauntlet. A few days later Immunity is at it again--this time with a workable exploit.
Immunity ships exploits for its paying subscribers has issued a flash movie detailing the exploit in action. It isn't 100 percent reliable, but the odds are better than unlikely now.
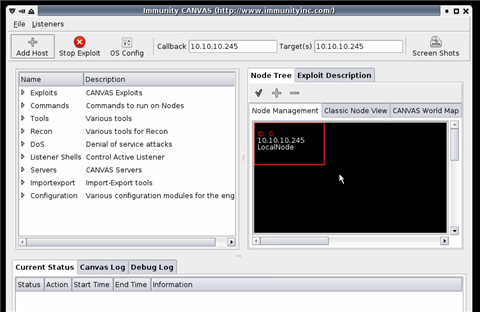
Here are a few screens from the movie:
And.
Your turn Microsoft. Ryan Naraine has more.