Malware tricks Facebook users into exposing credit cards

A new variant of the Ice IX malware tricks Facebook users into exposing their credit card, debit card, and/or social security numbers. The malware does this by displaying a separate Web form inside a browser pop-up window, which looks similar to Facebook's design, when you navigate to the social network's login webpage. One of the version of this malware ask for the following: Cardholder name, Credit or debit card number, Expiry date, Card identification number, and Address on your monthly statement.
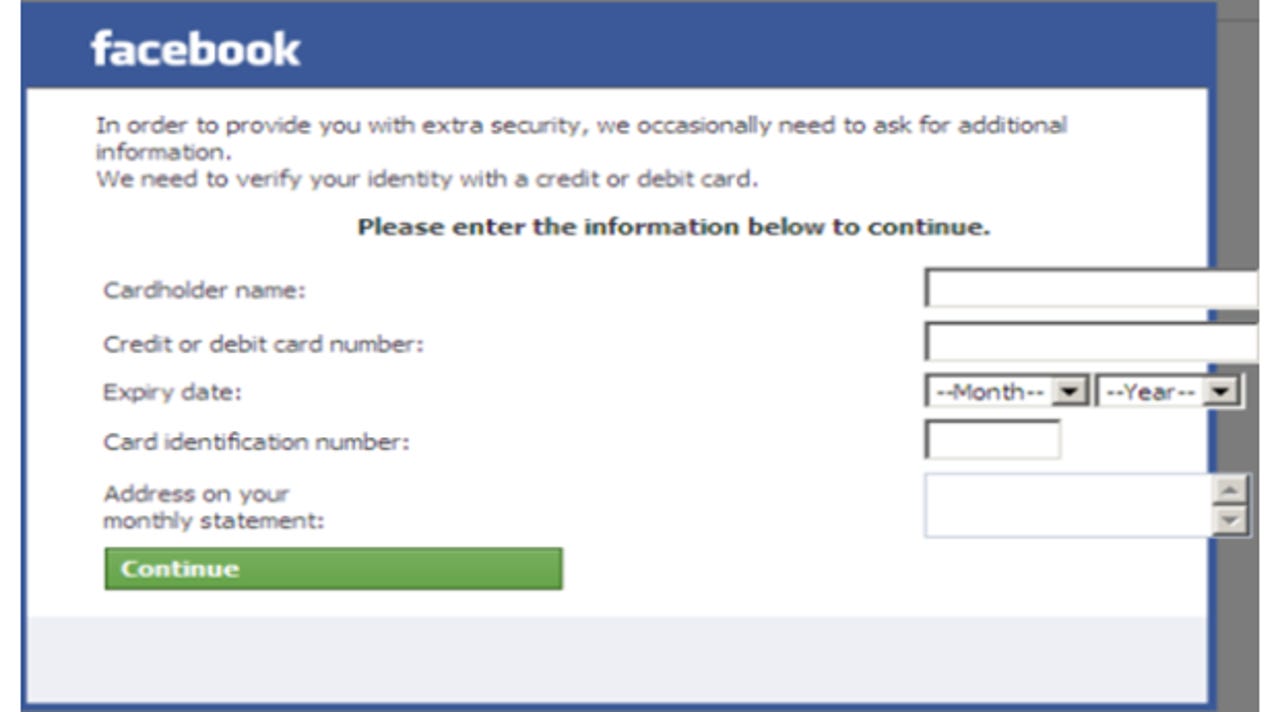
As you can see in the screenshot above, courtesy of Trusteer, the attackers claim the information is needed to verify the victim's identity and provide additional security for their Facebook account:
In order to provide you with extra security, we occasionally need to ask you for additional information. We need to verify your identity with a credit or debit card. Please enter the information below to continue.
In other words, if you don't want to hand over your credit card or debit card, you won't be able to continue to your Facebook account.
The security firm even discovered a "marketing" video circulating in underground forums, presumably used by the creators of the malware to demonstrate how the web injection works as a selling point to anyone who wants to steal the information from unsuspecting Facebook users. The video shows the whole web injection process.
First, a criminal logs in to his or her Facebook account. Next, the pop up presents the aforementioned message, although it also requests a social security number and date of birth. The criminal fills out the fields, and finally the information entered is shown being delivered to his or her messenger application. Once the rogue form is submitted, the malware forwards the sensitive information to its authors via instant message, so it can be abused as soon as possible.
"This video illustrates the seamless sophistication of pre-built webinjects that are readily available for purchase on the internet," Trusteer CTO Amit Klein said in a statement. "It also demonstrates how accomplished criminals are at marketing their malware products. Most of all, this attack highlights how fraudsters are branching out from their 'bread and butter' online banking schemes into lateral applications with much larger user populations. By attacking Facebook and other ubiquitous social networks fraudsters can tap a massive pool of victims. They can also use the information harvested from social network users to perpetuate fraud on multiple in fronts including online banking, retail, and even to penetrate enterprise and government networks."
Facebook will never ask for your credit card number, debit card number, social security number, or any other sensitive information on the site or via e-mail. That being said, while Facebook will never ask for your password over e-mail, in certain cases the company will and does ask for your password even if you are already logged in, as I learned last month.
I have contacted Facebook about this piece of malware and will update you if I hear back.
See also:
- Facebook virus or account hacked? Here's how to fix it.
- Facebook teaches users how to remove adware (video)
- Facebook releases official Guide to Facebook Security
- Sex sells: Men fall for Facebook scams more than women
- Facebook admits it needs to fight scams more efficiently
- Facebook Immune System checks 25 billion actions every day