Researcher: Firefox vulnerable to ID spoofing

Firefox 2.0 has a vulnerability that can leave its users susceptible to an identity theft attack, according to Aviv Raff, a security researcher based in Israel.
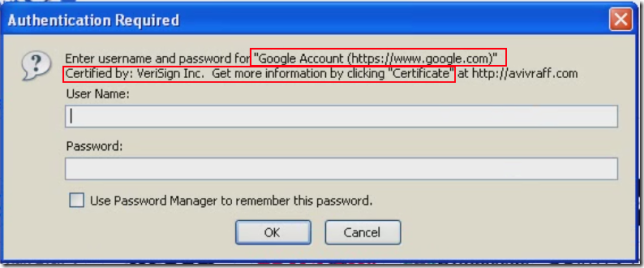
Raff outlined a bug in Firefox that allows spoofing and enables an attacker "to conduct phishing attacks, by tricking the user to believe that the authentication dialog box is from a trusted website." The versions affected include Firefox v2.0.0.11 and prior versions. Ryan Naraine got a private demo of Raff's work and noted that this attack is easy to fall for.
Gallery: How to secure Firefox.
Raff in his post outlines two possible attacks:1. An attacker creates a web page with a link to a trusted website (e.g. Bank, PayPal, Webmail, etc.). When the victim clicks on the link, the trusted web page will be opened in a new window, and a script will be executed to redirect the new opened window to the attacker's web server, which will then return the specially crafted basic authentication response.
2. An attacker embeds an image (pointing to the attacker's web server, which will return the specially crafted basic authentication response) to:
- A mail which will be sent to a webmail user.
- RSS feed which will be consumed by a web RSS reader.
- A forum/blog/social network page.
As for the workaround, Raff suggests avoiding sites that require password authentication and give you a dialog that looks like this. Mozilla last issued a security patch for Firefox Nov. 27.