Vendor claims Acrobat 9 passwords easier to crack than ever
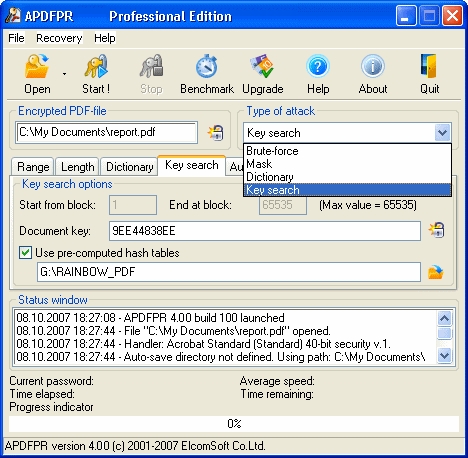
According to the company, Adobe Acrobat 9 passwords are a hundred times easier to crack than the ones in Acrobat 8 :
"ElcomSoft has discovered that the new PDF protection system implemented in Acrobat 9 is even faster to recover than in previous versions. In fact, a hundred times faster. "The new version of Adobe Acrobat is easier to break", claims ElcomSoft CEO Vladimir Katalov, quoting a speed increase of two orders of magnitude for the new format. "The new product has surprisingly weak protection", he adds. According to ElcomSoft's CEO, using 256-bit AES encryption per se is not enough to achieve ultimate security without employing complex approach and consideration of the entire security system. "
Yesterday, Abobe issued a statement commenting on their implementation of the 256-bit encryption, confirming the trade-off that they made so that 256-bit password protected documents could open faster in Acrobat 9, whereas password recovery tools could indeed achieve better brute forcing speed :
"The current specification for password-based 256-bit AES encryption in PDF provides greater performance than the previous 128-bit AES implementation. While this allows for 256-bit AES password protected documents to open faster in Acrobat 9, it can also allow external brute-force cracking tools to attempt to guess document passwords more rapidly because fewer processor cycles are required to test each password guess. These tools operate independently of Acrobat and work directly on a password protected document by repeatedly guessing from lists of dictionary words like "turkey", "potato", and "pie" to see if the document will open."
The single most obvious vulnerability that could undermine any encryption algorithm used, remain the use of weak passwords or passphrases. And in times when the very same vendor that's making the claims is improving the brute forcing speed through GPU acceleration with NVIDIA cards, perhaps allowing third-party password recovery software to perform better at PDF files wasn't exactly the best move in this case.