China suffers 'largest' cyberattack; Censorship makes it difficult to gauge attack scope

Parts of China went offline on Sunday after the state Internet watchdog admitted the country had suffered "the largest denial-of-service attack it has ever faced."
But the motives, depth, and scope of the attack remains unclear, in part due to the heavy state regulation and censorship policies enacted by the country's ruling party.
According to The Wall Street Journal, which first reported the story on Monday after speaking to CloudFlare chief executive Matthew Prince, the company saw a 32 percent drop in traffic for thousands of websites on the Chinese '.cn' domain. Prince noted that this dip of traffic was "likely representative" of the overall drop in the country.
As for motives, he suggested the attack could boil down to a single individual, and would not necessarily require much technical sophistication or resources.
The attack occurred roughly between 2 a.m., followed by a more intense attack at 4 a.m. (Chinese) on Sunday local time, according to the Chinese Internet Network Information Center (CINIC). The regulator did not offer any suggestions on either motive or the identity of the attacker.
By Monday, the attack had ceased and many are now able to access websites on Chinese domains as normal.
Attack confirmed, but tight-lipped on suspects
The Chinese government has been accused of attacking a number of Western media outlets and U.S. government networks over many years. Most recently, The New York Times and The Wall Street Journal suffered attacks at the hands of Chinese hackers — claims Chinese officials denied.
As a result, a number of suspects in this alleged cyberattack rise to the top of the table.
Foreign states such as the U.S. or the U.K. have been known to launch cyberattacks (and have the domestic legality to initiate such a response) if they fear they are currently or are about to fall victim to an attack themselves.
Also, the trial of former police chief Bo Xilai, which now enters its fifth day as of Monday, could also act as motive for some amid a crackdown on social media.
This is just one example of China's ongoing bid to silence critics and opponents of the government's ruling party, making it difficult for journalists to even source commentary from users in the country.
Censorship makes attack scope difficult to gauge
China may have a vast population but it still has a developing landline and Internet infrastructure, which has yet to reach the 50 percent population reach mark, according to the CINIC in January.
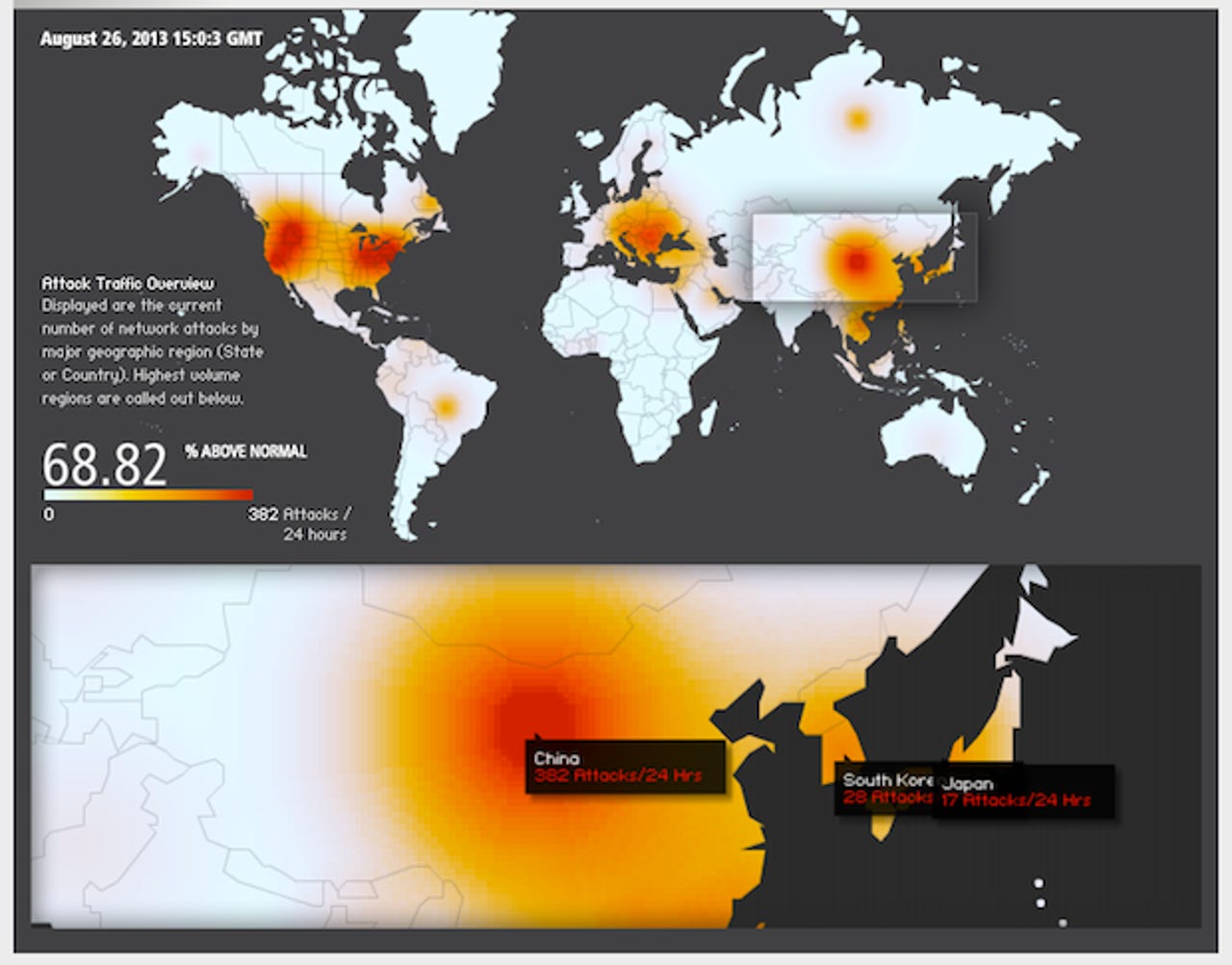
Akamai's real-time Web monitor lit up in China, representing a massive spike in cyber-attack traffic. The report said there were 379 attacks in the past 24 hours, the highest number of attacks per country on the map. Other hotspots include eastern and southern Europe, as well as five U.S. states, including New York, Delaware, Indiana, Idaho, and California.
Google, often an authority under these kinds of circumstances, paints a different picture — one of very different results to Akamai. For almost three years, Google's traffic in the country has been almost zero — except for a sudden spike during mid-2013 for about two weeks.
The search giant infamously pulled out of the country in 2010 as a result of an attack on its networks by the Chinese. The country's government strenuously denied the allegations, in spite of a bevy of evidence to suggest otherwise.
China's government has yet to say anything. Though, in times similar to this weekend, the ruling party has been quick to accuse without sufficient evidence to support such claims. Whether it's even a cyberattack remains unclear. It could be, as has been the case before, propaganda in order to deflect away from more embarrassing circumstances.
But with deep-rooted censorship engrained in the government's mantra and a determined selectiveness with the truth, we may never know the actual truth of what happened in this latest attack.