Japan ministry information reportedly stolen in cyberattack

Highly confidential documents related to sensitive trade negotiations are suspected to have been stolen from computers at Japan's farm ministry.
According to The Daily Yomiuri on Thursday, citing government sources, a cyberattack originating from abroad obtained more than 3,000 pieces of information from the country's Ministry of Agriculture, Forestry and Fishery, including about 20 top-secret documents on the Trans-Pacific Partnership (TPP) free trade pact negotiations.
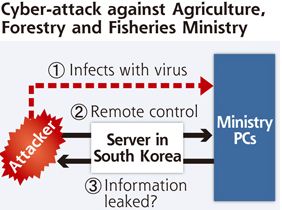
Investigators from the government allegedly found evidence indicating the computers in the ministry had been remotely controlled by and communicated with a server abroad, the sources said.
They also believed the attack targeted documents made just before an Asia-Pacific Economic Cooperation Summit meeting in November 2011, and before a Japan-U.S. summit meeting in April 2012.
It was also likely that the attacker obtained diplomatic policy information, the investigators said.
For example, one document created before the April 2012 meeting between previous prime minister Yoshihiko Noda and United States president Barack Obama, contained a draft statement on the TPP drawn up, with Japan's foreign ministry, which was to be incorporated into a joint statement issued by both leaders.
Computer remotely controlled by South Korean server
It is believed the documents moved from a personal computer issued to an official in charge of the TPP and other international negotiations, to another computer, where the data was compressed to make transmission easier.
The computer then allegedly communicated with a server which had an IP address in South Korea as the operations screen was displayed in the Korean language. Further investigations uncovered that the attacker apparantly manipulated the South Korean server.
The ministry was then warned by Japan's National Information Security Center (NISC) a suspicious transaction had been made. After the warning, the ministry launched an investigation, discovering around early 2012 that a document created in October 2011 was likely to have been transmitted outside the ministry.
The computer infected with a virus was then isolated, but the ministry later found other ministry computers had been infected. It is not known when the computer started to be remotely controlled, but the ministry said it has been stopped.
When approached by the Japan news site, an official from the ministry declined to comment, stating that admitting a virus infection had occured would expose the weakness of the ministry's computer system. However, the official also did not deny material had been stolen.