Telstra exposes customer information

Telstra has inadvertently exposed customer information to the web after one of its internal tools was indexed by Google and made public.
A Whirlpool forum user discovered the internal tool in a Google search after looking for a customer support phone number they had been given during a phone inquiry with Telstra. The user's post was first spotted by the Sydney Morning Herald.
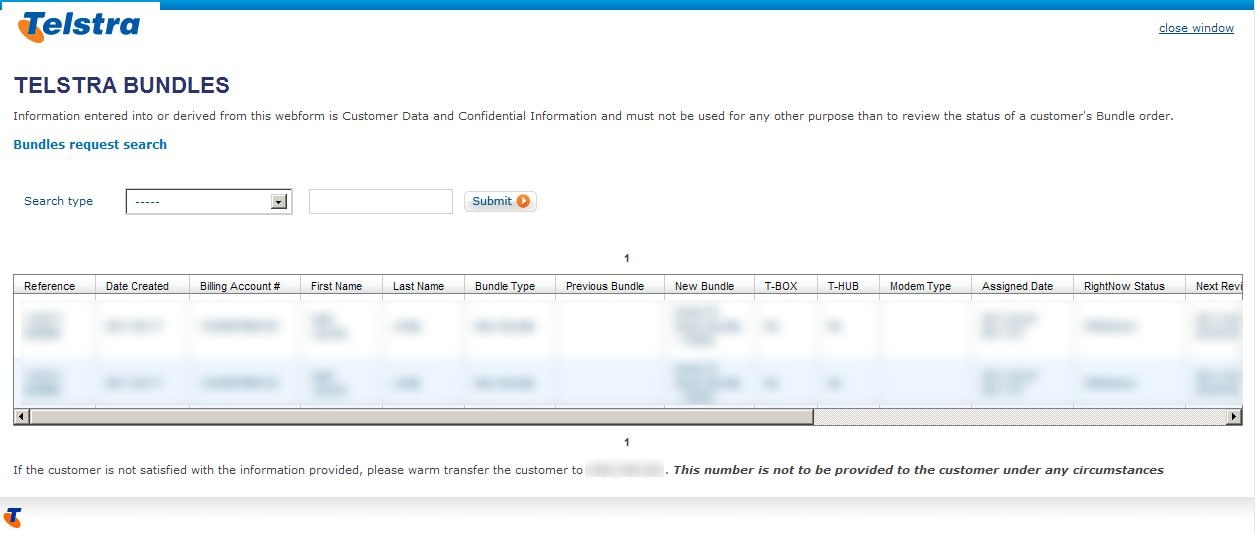
The tool was meant for use by Telstra employees to search customer records by a customer last name, reference number, billing account number or sales force number.
However, despite the page clearly stating "information entered into or derived from this webform is Customer Data and Confidential Information and must not be used for any other purpose than to review the status of a customer's Bundle order", no attempt was made by the tool to authenticate the user.
Using the tool, anyone could access information about a Telstra customer's Bundle orders, including their plan, billing account numbers, first and last names and notes about their account. Users on the Whirlpool forums confirmed that their own details and accurate information such as addresses, passwords and mobile numbers had been stored in their account notes.
At the time of ZDNet Australia's initial inquiries to Telstra, the page was still online and customer details accessible to anyone. Telstra told ZDNet Australia that it was moving on the problem.
Shortly afterwards attempts to access the tool were blocked.
"We apologise to customers who may have been impacted by this issue. Telstra takes its customers [sic] privacy seriously," the company said in a statement. "The site has been disabled and a full investigation is underway. Telstra will brief the Privacy Commissioner."
This was not the only internal tool Telstra uses that was exposed to the web. Additional forms that could have potentially allowed users to administer BigPond email addresses, including transferring them between accounts, were found on the same domain. Instructions on the pages that were intended for Telstra staff read "This form is only to be used by Front of House agents or retail staff".
While the pages are no longer functional, they are still listed in Google's search results, including cached results, at the time of writing.