How-to Guides
Practical tips, tricks, and advice for getting things doneAnalysis & Opinion
Explore a fresh perspectiveLatest
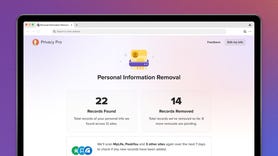
- How to freeze your credit (and why you might want to)
- AI Safety Summit round two draws government, industry leaders to Seoul ...
- Google is shutting down Google One VPN because 'people simply weren't ...
- Sisense's data breach is serious enough that CISA is investigating. Here's ...
- The best VPNs for iPhone and iPad: Expert tested
-
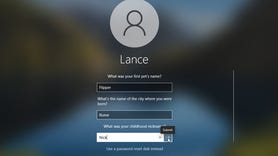
A mass email notification of a data breach overloaded Experian's servers, causing slow performance and access issues for customers trying to enroll in free credit monitoring.