How-to Guides
Practical tips, tricks, and advice for getting things doneAnalysis & Opinion
Explore a fresh perspectiveLatest
- Brave search engine adds privacy-focused AI - no Google or Bing needed
- Proton VPN review (2024): A very solid VPN with robust leak protection
- Android could soon protect you from malicious apps by quarantining them
- National Guard will use Google's AI for faster disaster response and ...
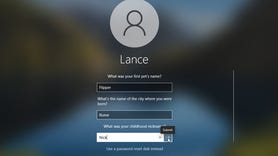
- Criminals want to pay T-Mobile and Verizon staff for SIM swaps. Here's ...
-
The newest version of the Blink Mini sees key improvements that make it worthy even for non-budget shoppers, and it's down to $30 for a limited time.