U.S. is a hotbed of botnet activity, says McAfee

If your computer has, say in the past few months, fallen victim to a botnet, you might be surprised to find out which country its control servers are in.
Why? According to security firm and anti-virus maker McAfee, the U.S. tops the list of countries hosting active 'command' servers, and the second is a former British colony island and popular tourist destination in the middle of the Caribbean, the British Virgin Islands.
And there you were thinking it was somewhere in the Middle East, Russia, or China. Tsk, tsk.
According to the company, McAfee has millions of endpoints and network security appliances sending data back to the company's Global Threat Intelligence unit, combined with good old fashioned pen-to-paper research, to determine exactly what the state of the dark side of the Internet looks like.
Here's the list:
- United States: 631 active command servers
- British Virgin Islands: 237 active command servers
- Netherlands: 154 active command servers
- Russia: 125 active command servers
- Germany: 95 active command servers
- Korea: 81 active command servers
- Switzerland: 77 active command servers
- Australia: 63 active command servers
- China: 48 active command servers
- Canada: 38 active command servers
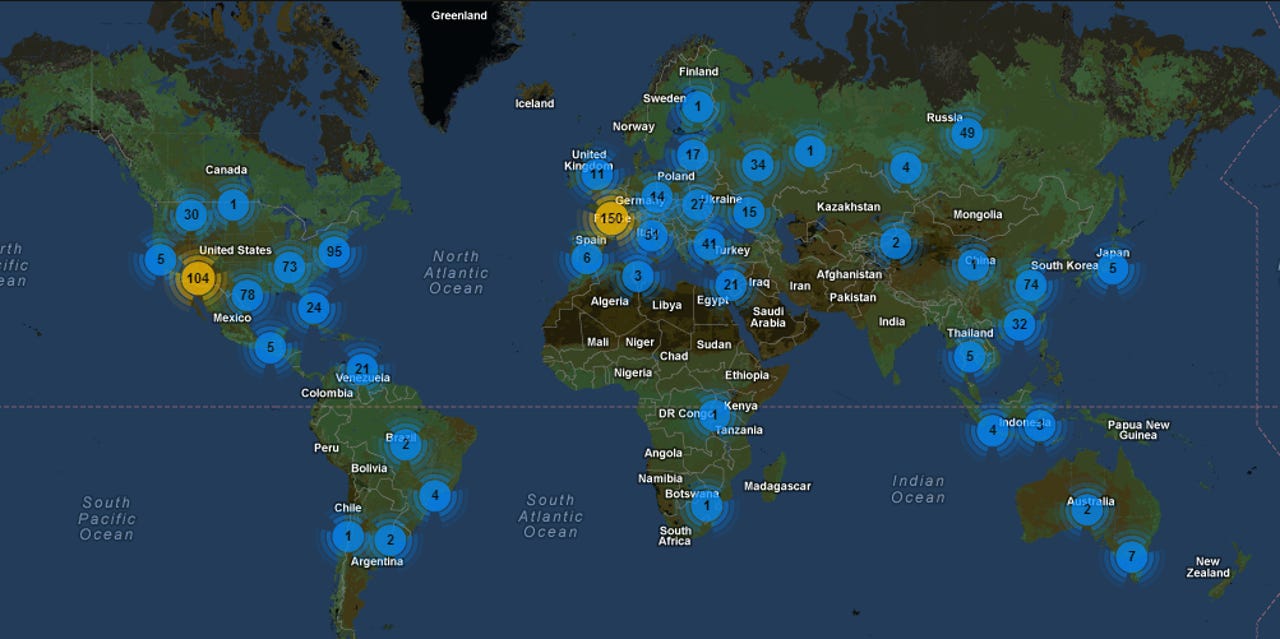
You can see from the image that the countries labeled in yellow are the main hosts of active botnet control servers. There's a focus on two particular areas: Western Europe and the United States.
While there's a relatively equal spread of botnets across Asia, Northern Europe and parts of the Middle East, it's the most developed nations that are most vulnerable—understandably, considering botnets recruit ordinary end-user PCs and Macs that turn into 'zombie' machines in order to carry out distributed denial-of-service (DDoS) attacks and serve up other nasties.
Late last year, the U.S. Department of Justice and the FBI, with help from other international law enforcement agencies, smashed a cybercrime ring that ensnared more than 11 million machines worldwide. Facebook's security teams assisted the Justice Dept. after the social networking giant found variants of the Yahos malware, which affected users of the social network.
It was thought to have been one of the largest botnets in history, pegging in at more than $850 million in total worldwide losses.