ATMZombie Trojan strikes Israeli banks

The ATMZombie Trojan is believed to have stolen hundreds of thousands of dollars from victims using banks located in Israel in a fresh campaign.
ATMZombie, identified in November 2015 by researchers from Kaspersky Lab, has been detected in a cyberattack campaign focused on stealing funds from Israel bank accounts. According to the cyberforensics firm, the malware is not only stealthy and sophisticated but is able to launch Man-In-The-Middle (MITM) attacks to intercept traffic and steal online bank credentials.
The malware uses a common method to infect a victim's machine: phishing campaigns . Rather than send out spam emails en masse, however, the group craft each email or link to a specific victim or bank, which Kaspersky researchers say "requires either very good intelligence-gathering techniques or an insider that can, legitimately or not, get a hold of the list of clients."
Unfortunately, crafted and tailored emails are likely to increase the chance of success in compromising a victim's machine.
In a blog post on Friday, Kaspersky researchers said the malware, once dropped via downloads or malicious links, uses a number of techniques to secure bank credentials from victims. The first method, known as "proxy-changing," is the MITM attack.
This technique involves browser proxy configurations being modified in order to capture traffic sent between a client and server.
But how do you grab this data when so many banks use encrypted channels and legitimate, signed certificates as standard? Realizing this was a missing element of their attack, the cybercriminal group developed and issued their own certificates, which is embedded within the malware dropper and then inserted into the root Certification Authority (CA) list accepted by the victim's machine.
When a PC is infected and the credentials secured, the cybercriminals do not rely on direct wire-transfer or trading to steal cash. Instead, attackers issue a money transfer order to a money mule's phone number, made possible with information such as the victim's personal details, the date, Israeli ID and amount. The group also used other methods to withdraw cash, such as through the Post Office, to stay anonymous and difficult to track.
The highest transaction recorded was $750 -- and while still a lot of money for the average person, this may not have been enough to raise alarms quickly.
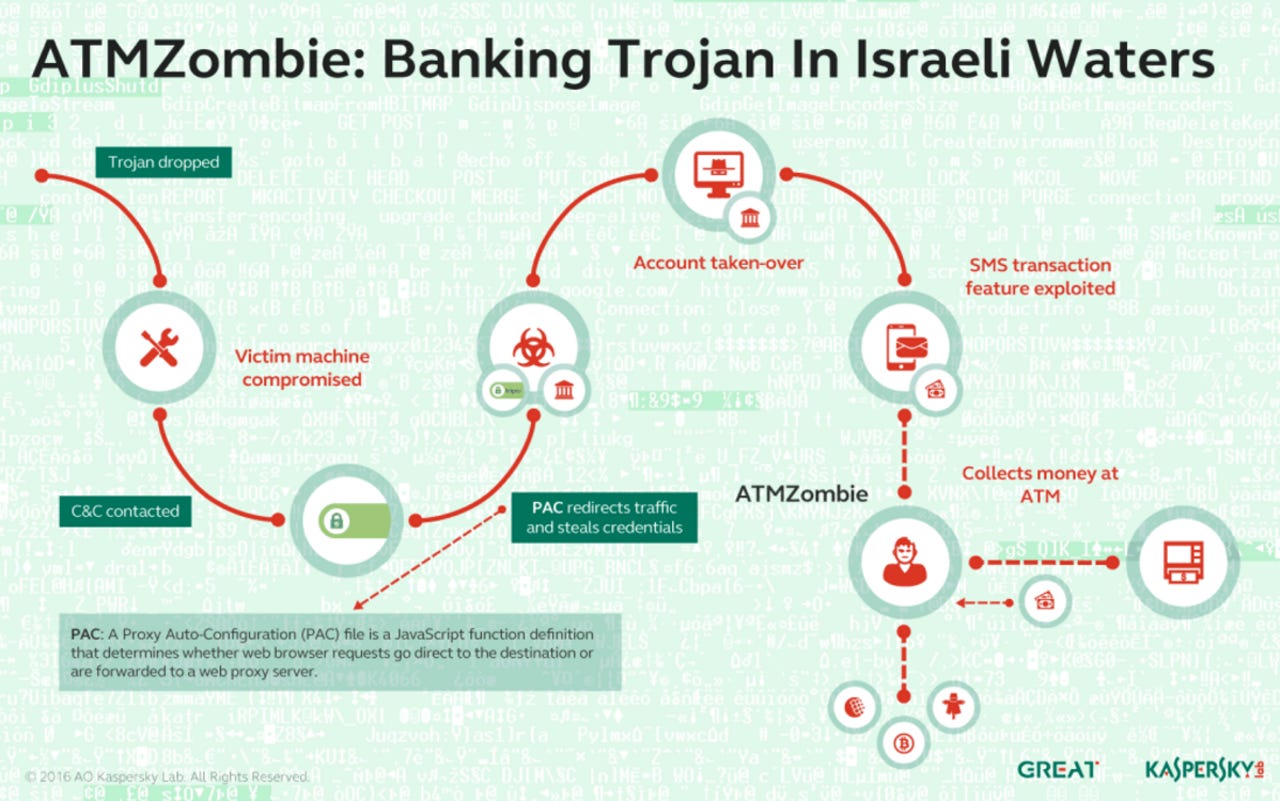
Kaspersky dubbed the money mules as "Zombies," since it was found young people were withdrawing the cash from ATMs in return for a small percentage, but the teens were likely unaware of what the operation was.
Security
"This service might cause its executor to be accused for committing a crime; however, the chance of proving that they were aware of the entire operation is close to none," the team says. "After all, they are not doing anything malicious."
The money stolen from victim accounts is believed to have reached upwards of hundreds of thousands of dollars, but the Israeli banks in question compensated victims, leading to only the financial institution itself losing out.
As far as the company knows, the attack -- which impacted hundreds of victims -- was stopped by the banks once they caught wind of the operation.
The threat actor behind this campaign is believed to be rather deep in the bank Trojan game, as they have also registered malicious domains to host other Trojans; namely Corebot, Pkybot and AndroidLocker.
Top tips to stay safe on public Wi-Fi networks
Read on: Top picks
- How to increase your Bitcoin mining profit by 30 percent with less effort
- SMS Android malware roots and hijacks your device - unless you are Russian
- Bug bounties: Which companies offer researchers cash?
- Shodan: The IoT search engine privacy messenger
- What happens when you leak stolen bank data to the Dark Web?