Bank of India site hijacked, launching exploits

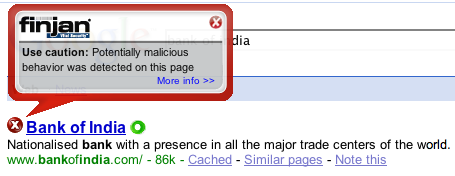
The Bank of India Web site has been hijacked by online criminals and is being used to serve up rootkits and backdoor Trojans on unpatched Windows machines.
Malware hunters at Sunbelt Software are warning that a snippet of code has been planted into the Bank of India Web site to redirect surfers to an exploit server.
There is evidence that the Russian Business Network (RBN), a group known for aggressive malware attacks, is behind this latest high-profile site compromise.
[ SEE: Super Bowl stadium site hacked, seeded with exploits ]
The RBN has been closely linked to the virulent Storm Worm attacks, VML, phishing, child pornography, Torpig, Rustock, and many other criminal attacks to date.
The Bank of India redirect is sending Windows users to a server hosting an e-mail worm file, two rootkits, two Trojan downloaders and three backdoor Trojans.
"Fully patched systems are likely unaffected," Sunbelt Software president Alex Eckelberry said.
A source tracking the attack tells me the IcePack exploit launcher is the back-end being used for this run of drive-by downloads.
[ UPDATE: 9:00 PM Eastern ] This video (.wmv) from Roger Thompson at Exploit Prevention Labs shows the kind of damage that's done when an unpatched machine simply surfs to the Bank of India home page.
It's been almost seven hours since the compromise was discovered but Bank of India is still serving up the malicious redirect code. Malware researchers are working behind the scenes to make contact with the authorities to get the site cleaned and patched.
[ UPDATE #2: August 31, 2007 @ 9:59 AM ] The Bank of India site is now disinfected. This note appears on the home page:
This site is under temporary maintenance and will be available after 19:30 IST
To get a thorough understanding of what was happening at Bank of India during the site compromise, read Dancho Danchev's blow-by-blow of this attack, which used fast-flux networks to run multiple malware campaigns.