Blackmail ransomware returns with 1024-bit encryption key

Virus analysts at Kaspersky Lab (my employer) have intercepted a new variant of Gpcode, a malicious virus that encrypts important files on an infected desktop and demands payment for a key to recover the data.
The biggest change in this variant of the ransomeware is the use of RSA encryption algorithm with a 1024-bit key, making it impossible to crack without without the author's key. Here's the explanation:
We recently started getting reports from infected victims, analysed a sample, and added detection for Gpcode.ak to our antivirus databases yesterday, on June 4th. However, although we detect the virus itself, we can't currently decrypt files encrypted by Gpcode.ak – the RSA encryption implemented in the malware uses a very strong, 1024 bit key.
The RSA encryption algorithm uses two keys: a public key and a private key. Messages can be encrypted using the public key, but can only be decrypted using the private key. And this is how Gpcode works: it encrypts files on victim machines using the public key which is coded into its body. Once encrypted, files can only be decrypted by someone who has the private key – in this case, the author or the owner of the malicious program.
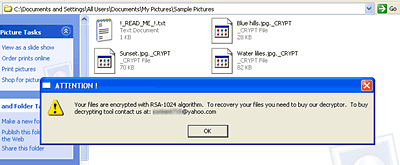
After Gpcode encrypts files on the victim machine, it adds ._CRYPT to the extension of the encrypted files and places a text file named !_READ_ME_!.txt in the same folder. In the text file the criminal tells the victims that the file has been encrypted and offers to sell them a "decryptor":
«Your files are encrypted with RSA-1024 algorithm.
To recovery your files you need to buy our decryptor.
To buy decrypting tool contact us at: ********@yahoo.com»
There are three Yahoo e-mail addresses associated with the new version of the ransomware.
For more on this story, see Slashdot, Network World and Viruslist.com. Here's background on the earlier version of GPcode.