Facebook fights botnet as malware authors talk trash

Facebook on Tuesday released a detailed account of how it disrupted a botnet dubbed Lecpetex, but the real insight may be the gamesmanship involved with trying to thwart malware.
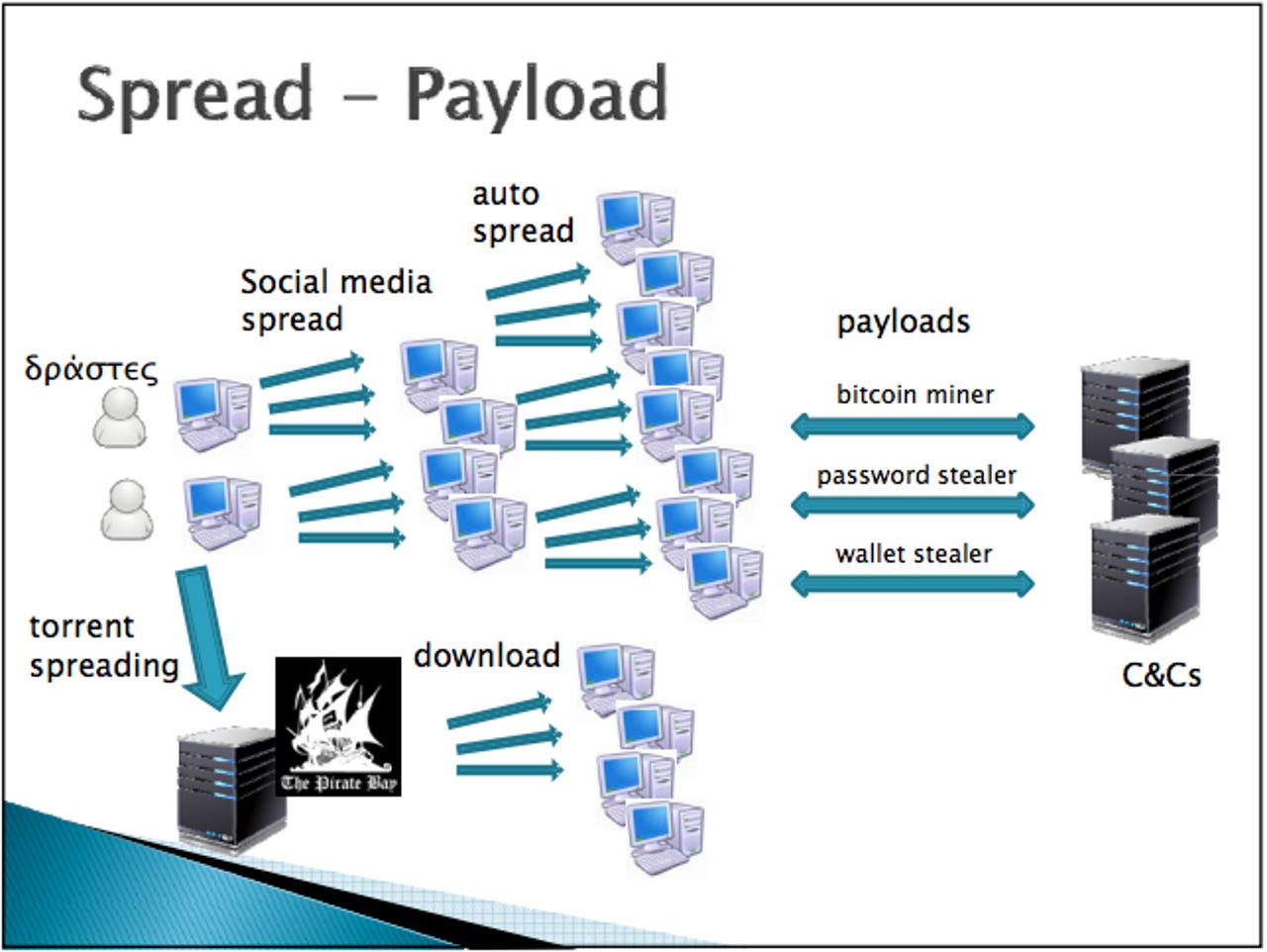
The company's account highlighted how Facebook spotted Lecpetex, which was later named by the Microsoft Malware Protection Center. With help from the Greek police Facebook aimed to stop infections that would lead to social spam. Lecpetex was built to be resilient and adapt to analysis and anything that would disrupt its mission.
Meanwhile, Lecpetex's authors continually changed code so the botnet could send more than 20 waves of spam between December 2013 and June 2014. The techniques used by the botnet weren't terribly fancy because it's the same social engineering story: Botnet sends attachment, user opens and your computer is infected.
Facebook said it started tinkering because anti-virus software wouldn't work and then deployed tools to extract information from Lecpetex. On July 3, Greek police arrested the Lecpetex authors. The timeline is notable because it highlights how takedowns take time and companies need to continue countermeasures for a while.
Here's the timeline:
- December 2013 - First automated identification of a spike in messages from Greece
- April 10-17, 2014 - Coordinated takedown of technical infrastructure including C2's, distribution accounts, testing accounts, monetization accounts
- April 30, 2014 - Referral to Greek law enforcement
- May 2014 - Authors leave notes for us on command and control pages and in their malware; authors switch to disposable email sites and Pastebin for command and control
- May-June 2014 - Facebook adds targeted backend measures to disrupt botnet operations
- June 2014 - Authors add mass email spreading technique to malware (presumably after spamming via Facebook became more difficult)
- July 3, 2014 - Greek law enforcement arrests people alleged to be primary authors
Facebook highlighted the botnet authors' comments left for investigators to find:
In May we noticed the command and control servers had started leaving notes for our team such as “Hello people.. :) <!-- Designed by the SkyNet Team --> but am not the f***ing zeus bot/skynet bot or whatever piece of sh*t.. no fraud here.. only a bit of mining. Stop breaking my ballz..” Around the same time we also noticed that encryption keys used in the malware began to use phrases that appeared to be messages such as “pepeishereagain1” and “IdontLikeLecpetexName.” These changes suggested to us that the authors were feeling the impact of our efforts.
The post provides a lot of technical detail and has the same underlying message: Facebook is serious about security. The biggest takeaway for you is to know the game: Enterprises and crime fighters tout these wins and cooperative efforts to highlight security efforts. The reality is that the wins can be few and far between as the trash talk in between lines of code continues.