Hackers can remotely steal fingerprints from Android phones

Our fingerprints might not be as safe as we think they are.
New research, set to be announced at the Black Hat conference in Las Vegas on Wednesday, by FireEye researchers Tao Wei and Yulong Zhang outlined new ways to attack Android devices to extract user fingerprints.
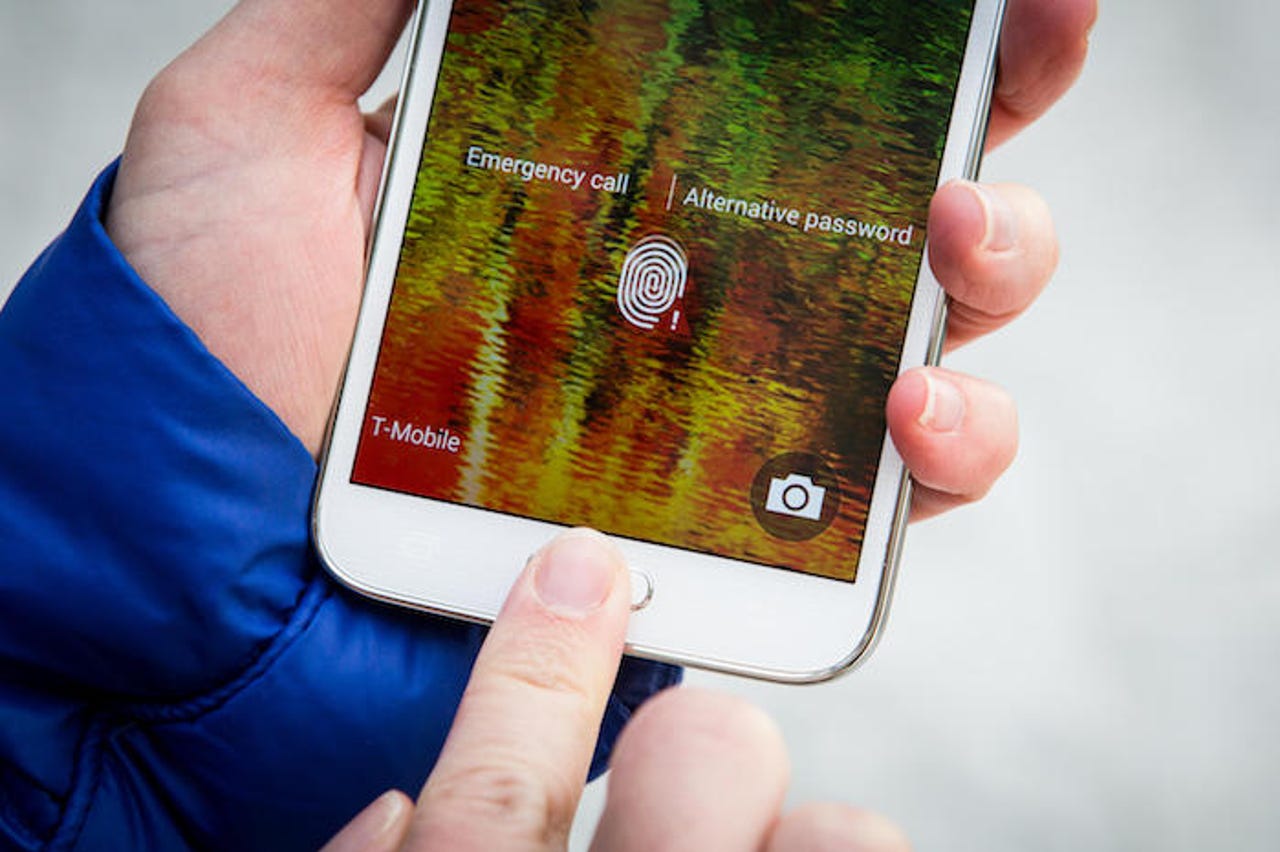
The threat is for now confined mostly to Android devices that have fingerprint sensors, such as Samsung, Huawei, and HTC devices, which by volume remains low compared to iPhone shipments. But down the line by 2019, where it's believed that at least half of all smartphone shipments will have a fingerprint sensor, the threat deepens.
Of the four attacks outlined by the researchers, one in particular -- dubbed the "fingerprint sensor spying attack" -- can "remotely harvest fingerprints in a large scale," Zhang told ZDNet by email.
The attack, which was confirmed on the HTC One Max and Samsung's Galaxy S5, allows a hacker to stealthily acquire a fingerprint image from an affected device because device makers don't fully lock down the sensor.
Making matters worse, the sensor on some devices is only guarded by the "system" privilege instead of root, making it easier to target. (In other words: rooting or jailbreaking your phone can leave you at a greater risk.) Once the attack is in place, the fingerprint sensor can continue to quietly collect fingerprint data on anyone who uses the sensor.
"In this attack, victims' fingerprint data directly fall into attacker's hand. For the rest of the victim's life, the attacker can keep using the fingerprint data to do other malicious things," Zhang said. And that's a big problem. Fingerprints might be commonplace in mobile payments and unlocking devices, but they have been used more in the past five years also for identity, immigration, and for criminal records.
Affected vendors have since provided patches after being alerted by the researchers.
The researchers did not comment on which vendor is more secure than others. But, Zhang noted that Apple's iPhone, which pioneered the modern fingerprint sensor, is "quite secure," as it encrypts fingerprint data from the scanner.
"Even if the attacker can directly read the sensor, without obtaining the crypto key, [the attacker] still cannot get the fingerprint image," he said.
The problem isn't just limited to mobile devices. The researchers warned that many of the attacks they note in their talk also apply to high-end laptops with fingerprint sensors.
The researchers advised users to use devices that were regularly updated, and only install apps from reliable sources.