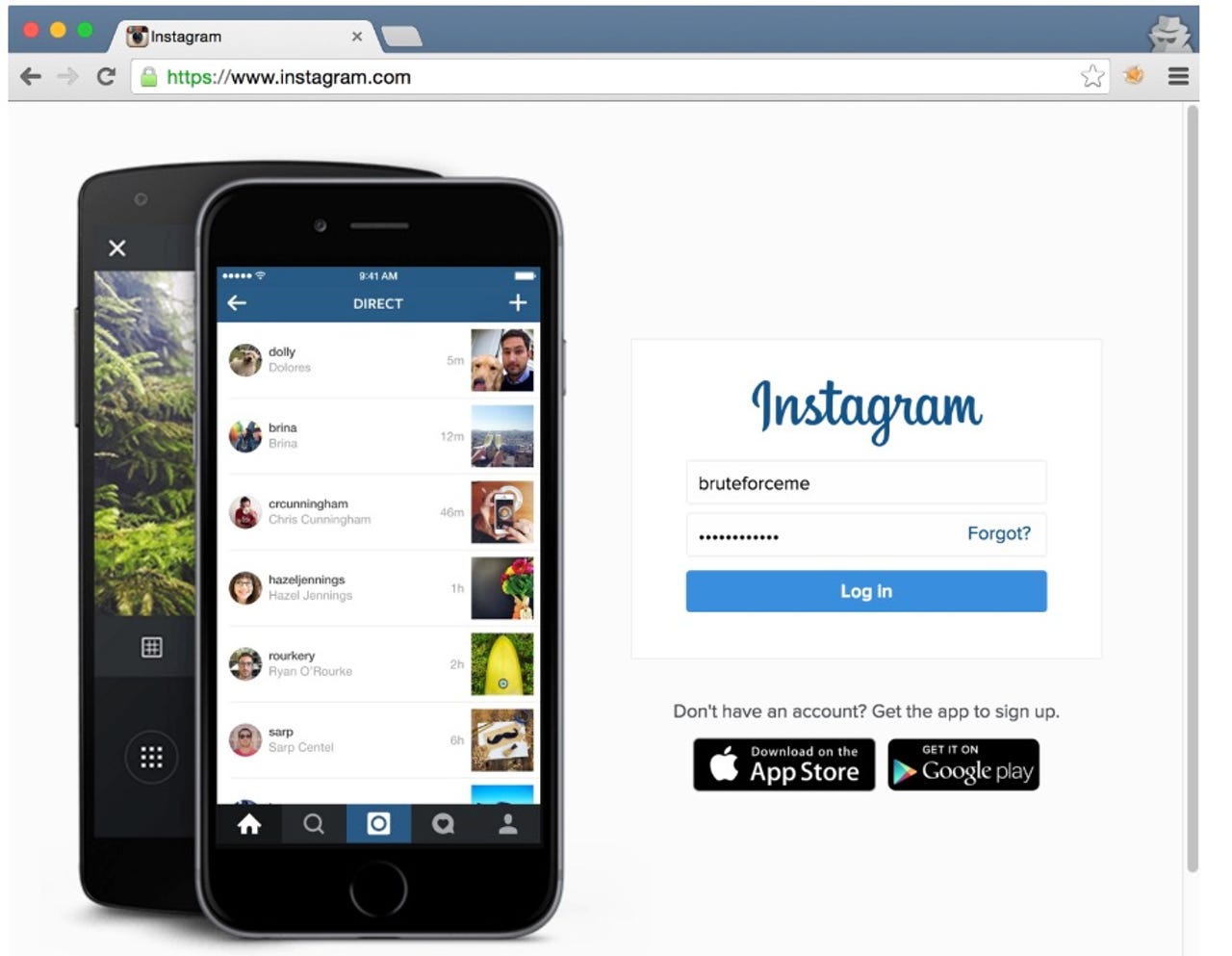
How to break Instagram with brute force

Facebook has patched two severe vulnerabilities which made it possible for a researcher to brute-force attack and compromise user accounts on Instagram.
Belgian security researcher Arne Swinnen, in the hunt for a reward as part of Facebook's Instagram bug bounty program, said in a blog post last week that he discovered two distinct vulnerabilities in the photo-sharing platform.
The security flaws, combined with Instagram's rather weak password policies, permitted attackers to brute-force the user credentials of accounts across the board -- and a general lack of two-factor authentication (2FA) only made matters worse.
The first vulnerability is an implementation bug in Instagram's mobile authentication process. A simple brute-force attack against the Android application's mobile endpoint with Burp intruder software revealed that 1000 guesses could be made from each unique IP address, after which the response changed to "username not found" as a means of limiting password guess attempts.
However, from this point, only the next 1000 guesses were protected by rate limiting. Afterwards, from the 2000th guess, an attacker would receive one successful response from Instagram stating whether the password was correct or incorrect, followed by the rate-limit block of "user not found."
The researcher noted that the only limitation of this attack was that on average, two authentication requests had to be made with each password attempt.
Swinnen created a "quick and dirty" script to exploit the flaw and brute-force the test account. The first 1000 guesses were considered "good" guesses while the following 1000 were considered "unreliable" and were ignored by the script.
The researcher said:
"Although the script made 10001 password guesses for account "bruteforceme", an attacker could simply login from any IP address, including the one that was used to mount the brute-force attack.
This indicated a lack of additional security controls against account compromise, such as account lockout, IP address location-based fraud detection."
The second security problem relates to Instagram's web application and registration endpoint.
When registering for a test account, the researcher found that replaying registration requests resulted in scripting errors which highlighted the credentials oracle. The researcher stripped all the parameters except "username" and "password" and was able to begin cracking the test account.
Security
No account lockout, rate limiting or protection systems were alerted during the brute-force attack. It took 1,001 attempts to confirm the brute-force tactics worked and the account password was discovered.
"Therefore, exploitation of these issues could have resulted in the compromise of millions of the 400+ million active Instagram accounts -- especially those with predictable passwords," Swinnen says. "Of course, targeted attacks against high-profile accounts could have been very effective as well."
The security flaws were submitted by Swinnen on 28 December 2015 and 8 February 2016 respectively. Facebook acknowledged these issues and was able to fix the first vulnerability by tweaking the rate-limiting bug in the mobile authentication endpoint.
The second security problem was patched by introducing rate-limiting on the web registration endpoint. It took a little longer than usual to resolve these problems as the first fix for the second vulnerability did not work.
Eventually, both vulnerabilities were patched properly and details of the flaws disclosed this month. Instagram also introduced an improved password policy and has banned simple passwords such as "123456" and "password." 2FA was introduced on the photo-sharing service in February but is yet to be rolled out globally.
Swinnen was awarded a combined bug bounty of $5,000 for disclosing the vulnerabilities.
10 things you didn't know about the Dark Web
Read on: Top picks