How was Comcast.net hijacked?
It's official, even a pothead can social engineer Network Solutions. In an in-depth interview with the hijackers, featuring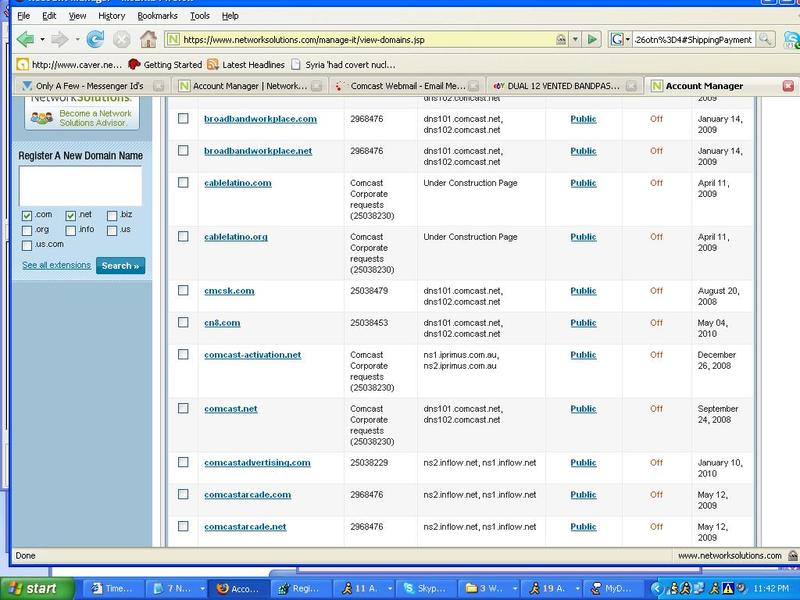
The hackers say the attack began Tuesday, when the pair used a combination of social engineering and a technical hack to get into Comcast's domain management console at Network Solutions. They declined to detail their technique, but said it relied on a flaw at the Virginia-based domain registrar. Network Solutions spokeswoman Susan Wade disputes the hackers' account. "We now know that it was nothing on our end," she says. "There was no breach in our system or social engineering situation on our end."
However they got in, the intrusion gave the pair control of over 200 domain names owned by Comcast. They changed the contact information for one of them, Comcast.net, to Defiant's e-mail address; for the street address, they used the "Dildo Room" at "69 Dick Tard Lane." Comcast, they said, noticed the administrative transfer and wrested back control, forcing the hackers to repeat the exploit to regain ownership of the domain. Then, they say, they contacted Comcast's original technical contact at his home number to tell him what they'd done.
Following ICANN's recently released advisory on preventing the very same impersonation attacks, it appears that even a first-tier domain registrar is still susceptible to registrant impersonation attacks. Makes you wonder on the state of understanding, detecting, and preventing social engineering attacks on the rest of the domain registrars.