Joomla patches eight-year-old critical CMS bug

Joomla has patched a critical bug which could be used to steal account information and fully compromise website domains.
This week, the content management system (CMS) provider issued a security advisory detailing the flaw, which is found in the LDAP authentication plugin.
Lightweight Directory Access Protocol (LDAP) is used by Joomla to access directories over TCP/IP. The plugin is integrated with the CMS.
Joomla considers the bug a "medium" severity issue, but according to researchers from RIPS Technologies, the problem is closer to a critical status.
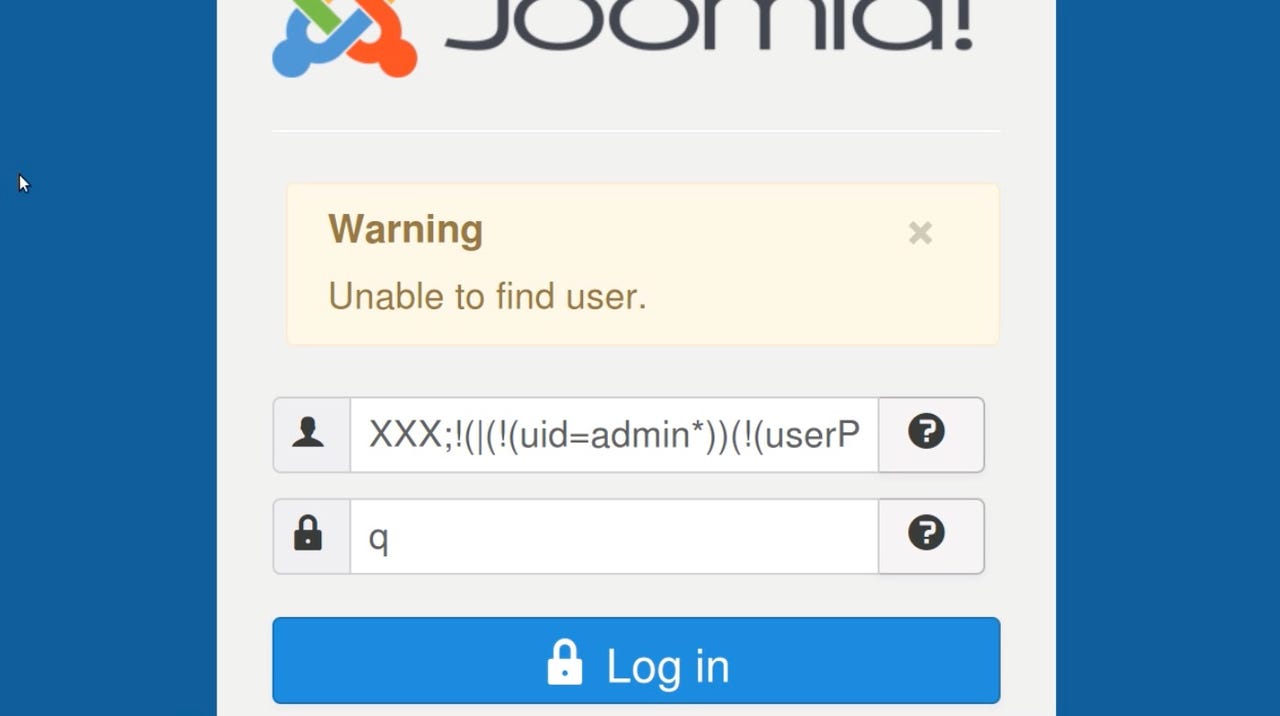
In a blog post, the team said the previously unknown LDAP injection vulnerability, in the login controller of the plugin, "could allow remote attackers to leak the super user password with blind injection techniques and to fully take over any Joomla <= 3.7.5 installation within seconds."
Through the flaw, CVE-2017-14596, a remote attacker is able to extract authentication credentials from the LDAP server, including the super user username and password, as long as Joomla is configured to use LDAP for authentication.
The vulnerability formed as user input is mixed unsanitized with the LDAP query markup that is passed to the LDAP search function.
The attacker does not need any privileges to exploit the bug, which has been present in the plugin for the past eight years. It is not known if the issue has been exploited in the wild.
"As one of the most popular open source CMS applications, Joomla receives many code reviews from the security community," RIPS commented. "Yet alone one missed security vulnerability in the 500,000 lines of code can lead to a server compromise."
After the vulnerability was disclosed to the Joomla team and confirmed in July, a fix has been released through the latest Joomla release, version 3.8.
Previous and related coverage
- Thousands of WordPress websites defaced through patch failures
- Ransomware springboards from WordPress to Joomla domains
- Wordpress, Joomla domains under attack through jQuery JavaScript library