Microsoft: Some ransomware attacks take less than 45 minutes

For many years, the Microsoft Security Intelligence Report has been the gold standard in terms of providing a yearly overview of all the major events and trends in the cyber-security and threat intelligence landscape.
While Microsoft unceremoniously retired the old SIR reports back in 2018, the OS maker appears to have realized its mistake, and has brought it back today, rebranded as the new Microsoft Digital Defense Report.
Just like the previous SIR reports, Microsoft has yet again delivered.
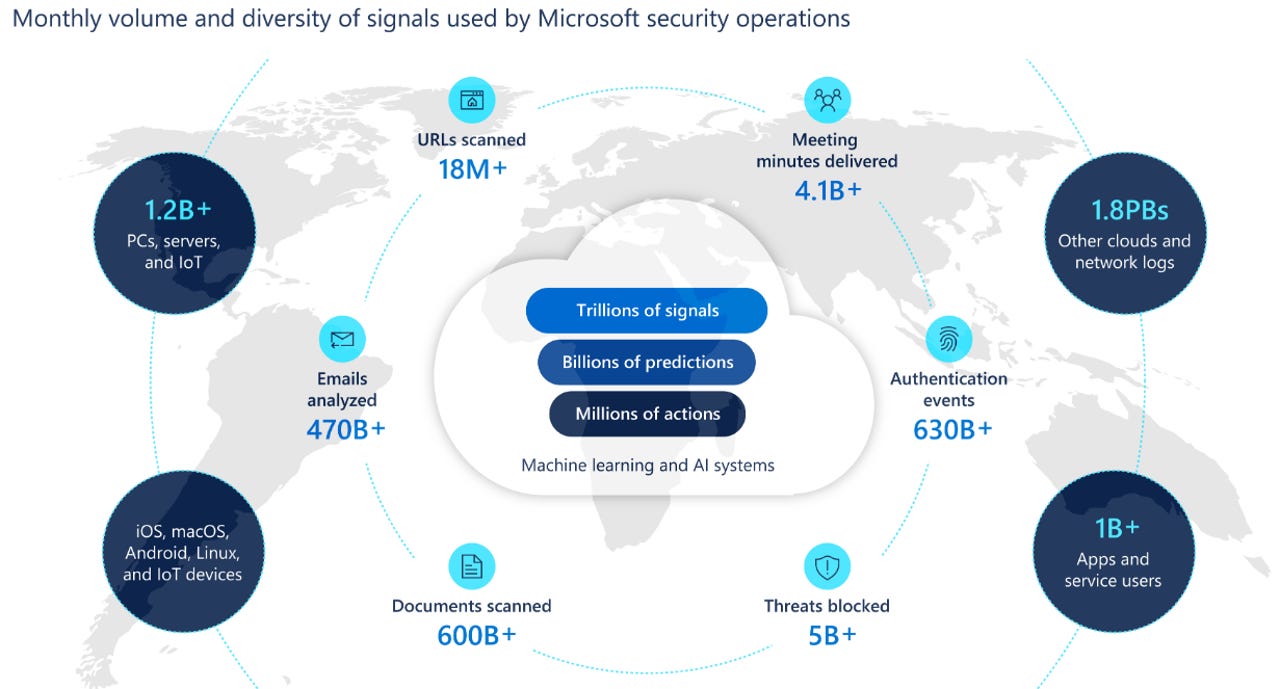
Taking advantage of its vantage points over vast swaths of the desktop, server, enterprise, and cloud ecosystems, Microsoft has summarized the biggest threats companies deal with today in the face of cybercrime and nation-state attackers.
The report is 88 pages long, includes data from July 2019 and June 2020, and some users might not have the time to go through it in its entirety. Below is a summary of the main talking points, Microsoft's main findings, and general threat landscape trends.
Cybercrime
2020 will, without a doubt, be remembered for the COVID-19 (coronavirus) pandemic. While some cybercrime groups used COVID-19 themes to lure and infect users, Microsoft says these operations were only a fraction of the general malware ecosystem, and the pandemic appears to have played a minimal role in this year's malware attacks.
Email phishing in the enterprise sector has also continued to grow and has become a dominant vector. Most phishing lures center around Microsoft and other SaaS providers, and the Top 5 most spoofed brands include Microsoft, UPS, Amazon, Apple, and Zoom.
Microsoft said it blocked over 13 billion malicious and suspicious mails in 2019, and out of these, more than 1 billion contained URLs that have been set up for the explicit purpose of launching a credential phishing attack.
Successful phishing operations are also often used as the first step in Business Email Compromise (BEC) scams. Microsoft said that crooks gain access to an executive's email inbox, watch email communications, and then spring in to trick the hacked users' business partners into paying invoices into wrong bank accounts.
Per Microsoft, the most targeted accounts in BEC scams were the ones for C-suites and accounting and payroll employees.
But Microsoft also says that phishing isn't the only way into these accounts. Hackers are also starting to adopt password reuse and password spray attacks against legacy email protocols such as IMAP and SMTP. These attacks have been particularly popular in recent months as it allows attackers to also bypass multi-factor authentication (MFA) solutions, as logging in via IMAP and SMTP doesn't support this feature.
Furthermore, Microsoft says it's also seeing cybercrime groups that are increasingly abusing public cloud-based services to store artifacts used in their attacks, rather than using their own servers. Further, groups are also changing domains and servers much faster nowadays, primarily to avoid detection and remain under the radar.
Ransomware groups
But, by far, the most disruptive cybercrime threat of the past year have been ransomware gangs. Microsoft said that ransomware infections had been the most common reason behind the company's incident response (IR) engagements from October 2019 through July 2020.
And of all ransomware gangs, it's the groups known as "big game hunters" and "human-operated ransomware" that have given Microsoft the most headaches. These are groups that specifically target select networks belonging to large corporations or government organizations, knowing they stand to receive larger ransom payments.
Most of these groups operate either by using malware infrastructure provided by other cybercrime groups or by mass-scanning the internet for newly-disclosed vulnerabilities.
In most cases, groups gain access to a system and maintain a foothold until they're ready to launch their attacks. However, Microsoft says that this year, these ransomware gangs have been particularly active and have reduced the time they need to launch attacks, and especially during the COVID-19 pandemic.
"Attackers have exploited the COVID-19 crisis to reduce their dwell time within a victim's system – compromising, exfiltrating data and, in some cases, ransoming quickly – apparently believing that there would be an increased willingness to pay as a result of the outbreak," Microsoft said today.
"In some instances, cybercriminals went from initial entry to ransoming the entire network in under 45 minutes."
Supply-chain security
Another major trend that Microsoft chose to highlight was the increased targeting of supply chains in recent months, rather than attacking a target directly.
This allows a threat actor to hack one target and then use the target's own infrastructure to attack all of its customers, either one by one, or all at the same time.
"Through its engagements in assisting customers who have been victims of cybersecurity intrusions, the Microsoft Detection and Response Team has observed an uptick in supply chain attacks between July 2019 and March 2020," Microsoft said.
But Microsoft noted that while "there was an increase, supply chain attacks represented a relatively small percentage of DART engagements overall."
Nonetheless, this doesn't diminish the importance of protecting the supply chain against possible compromises. Here, Microsoft highlights dangers coming from the networks of Managed Service Providers (MSPs, third-parties that provide a very specific service and are allowed to access a company's network), IoT devices (often installed and forgotten on a company's network), and open-source software libraries (which make up most of a company's software these days).
Nation-state groups
As for nation-state hacking groups (also known as APTs, or advanced persistent threats), Microsoft said this year has been quite busy.
Microsoft said that between July 2019 and June 2020, it sent out more than 13,000 nation-state notification (NSN) to its customers via email.
According to Microsoft, most were sent for hacking operations linked back to Russian state-sponsored groups, while most of the victims were located in the US.
These email notifications were sent for email phishing attacks against its customers. Microsoft said it tried to counter some of these attacks by using court orders to seize domains used in these attacks.
Over the past year, Microsoft seized domains previously operated by nation-state groups like Strontium (Russia), Barium (China), Phosphorus (Iran), and Thallium (North Korea).
Another interesting finding of the Microsoft Digital Defense Report is that the primary targets of APT attacks have been non-governmental organizations and the services industry.
This particular finding goes against the grain. Most industry experts often warn that APT groups prefer to target critical infrastructure, but Microsoft says its findings tell a different story.
"Nation state activity is more likely to target organizations outside of the critical infrastructure sectors by a significant measure, with over 90% of notifications served outside of these sectors," Microsoft said.
As for the techniques that have been preferred this past year (July 2019 to June 2020) by nation-state groups, Microsoft noted several interesting developments, with the rise of:
- Password spraying (Phosphorus, Holmium, and Strontium)
- Use of penetration testing tools (Holmium)
- The use of ever-more-complex spear-phishing (Thallium)
- The use of web shells to backdoor servers (Zinc, Krypton, Gallium)
- The use of exploits targeting VPN servers (Manganese)
All in all, Microsoft concludes that criminal groups have evolved their techniques over the past year to increase the success rates of their campaigns, as defenses have gotten better at blocking their past attacks.
Just like in years prior, the entire cybersecurity landscape appears to be sitting on a giant merry-go-round, and constant learning and monitoring is required from defenders to keep up with the ever-evolving attackers, may them be financially-motivated or nation-sponsored groups.