Modern banker malware undermines two-factor authentication
Modern banker malware, also known as crimeware, is now fully capable of bypassing the two-factor authentication obstacle by doing a simple thing - patiently waiting for the crimeware-infected victim to authenticate himself in order to abuse the access in real-time.
A recently published article at MIT's Technology Review, details a case where cybercriminals managed to steal $447K despite that two-factor authentication was in place:
Yet the manager's computer had a hitchhiker. A forensic analysis performed later would reveal that an earlier visit to another website had allowed a malicious program to invade his computer. While the manager issued legitimate payments, the program initiated 27 transactions to various bank accounts, siphoning off $447,000 in a matter of minutes. "They not only got into my system here, they were able to ascertain how much they could draw, so they drew the limit," says Roy Ferrari, Ferma's president.
The theft happened despite Ferma's use of a one-time password, a six-digit code issued by a small electronic device every 30 or 60 seconds.
This incident, among the countless number of similar but largely under-reported ones, raises several important questions. Compared to a previous case where a bank was sued for not offering two-factor authentication, should Ferma's bank be sued for actually offering two-factor authentication, but allowing the fraudulent transaction to take place?
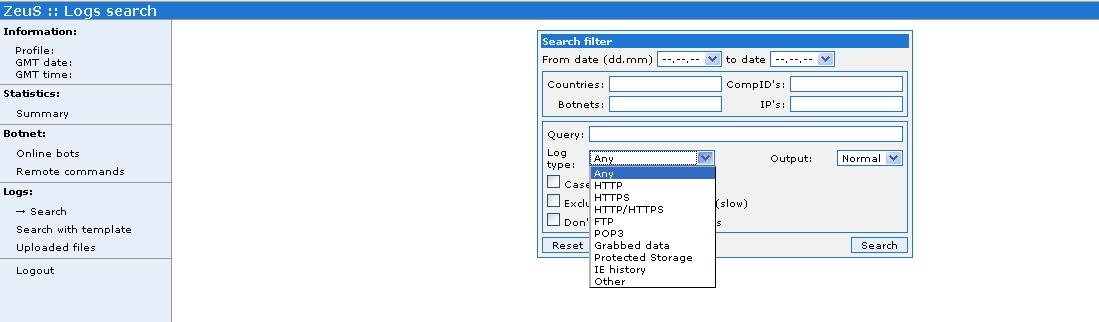
Also, could antivirus software have prevented (No security software, no E-banking fraud claims for you) the infection from taking place? Last seek, Trusteer published an advisory entitled "Measuring the in-the-wild effectiveness of Antivirus against Zeus" according to which the most popular banker malware Zeus, is successfully bypassing up-to-date antivirus software :
Installing an anti-virus product and maintaining it up to date reduces the probability to get infected by Zeus by 23%, compared to running without an anti-virus altogether. The effectiveness of an up to date anti virus against Zeus is thus not 100%, not 90%, not even 50% - it’s just 23%.
Its popularity has also prompted the launch of such services as the the Zeus Tracker, which currently list 537 active crimeware domains, with the majority of them hosted in Russia, the U.S and China, followed by the Netherlands, Ukraine and Germany. The real-time blocklist it generates is in fact so useful, the service came under a DDoS attack in February, 2009.
With banker malware clearly able to operate even on PCs with up-to-data antivirus product, a logical anti-fraud move by a bank's customer would be to reclaim control of their bank account by assuming the worst.
In Ferma's case, depending on whether or not their bank offered such services -- like it should -- the ability to set daily, weekly or monthly account transaction limits may have mitigated the impact of the actual compromise. Moreover, issuing one-time passwords (OTP) over SMS is just the tip of the iceberg when it comes to offering additional alert services. Not only is the availability of SMS alert services (automatic SMS alert for each incoming and outgoing transaction) highly advisable, it can help a crimeware-infected victim quickly get hold of their financial institution's 24/7 fraud report center in order to freeze the transaction and the account itself.
Naturally, cybecriminals have found ways to adapt to these SMS alerts, by exploiting badly implemented processes within particular financial institutions allowing a customer to change the mobile number in any particular moment of time. Due to the fact that, for instance, a Chinese bank wouldn't accept U.S mobile number for SMS alert and one-time password services, cybercriminals are already using services offering to accept and forward any data sent to a particular mobile number within a country where they maintain local numbers for fraudulent purposes.
Multiple-factor authentication simply cannot prevent fraudulent activity if the user is operating from a compromised environment in the first place.