RIM: Disable JavaScript in BlackBerry Browser

Research in Motion (RIM) is urging BlackBerry users to disable JavaScript in the smartphone's browser to block exploits from a security vulnerability showcased at this year's CanSecWest Pwn2Own contest.
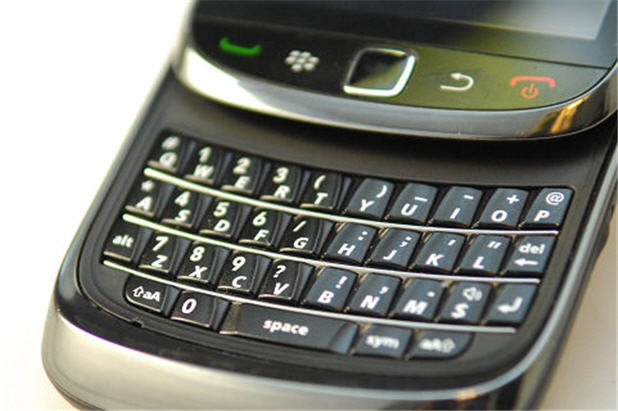
The vulnerability, which exists in the open source WebKit browser engine provided in BlackBerry Device Software version 6.0 and later, was exploited to hack into a BlackBerry Torch 9800 smart phone to steal the contact list and image database.
In response to the hack, RIM issued a security advisory to acknowledge the flaw and suggest a temporary mitigation until a comprehensive patch is issued.
From the advisory:
The issue could result in remote code execution on affected BlackBerry smartphones. Successful exploitation of the vulnerability requires the user to browse to a website that the attacker has maliciously designed. A successful exploit could allow the attacker to use the BlackBerry Browser to access user data stored on the media card and in the built-in media storage on the BlackBerry smartphone, but not to access email and other personal information on the file system of the BlackBerry smartphone.
The company suggests that users of the BlackBerry Device Software version 6.0 and later disable the use of JavaScript in the BlackBerry Browser to prevent exploitation of the vulnerability. The issue is not in JavaScript but the use of JavaScript is necessary to exploit the vulnerability.
RIM said it is investigating the issue to determine the best resolution for protecting BlackBerry smartphone users but did not provide a timeline for issuing a fix.