Rogue security software spoofs ZDNet Reviews
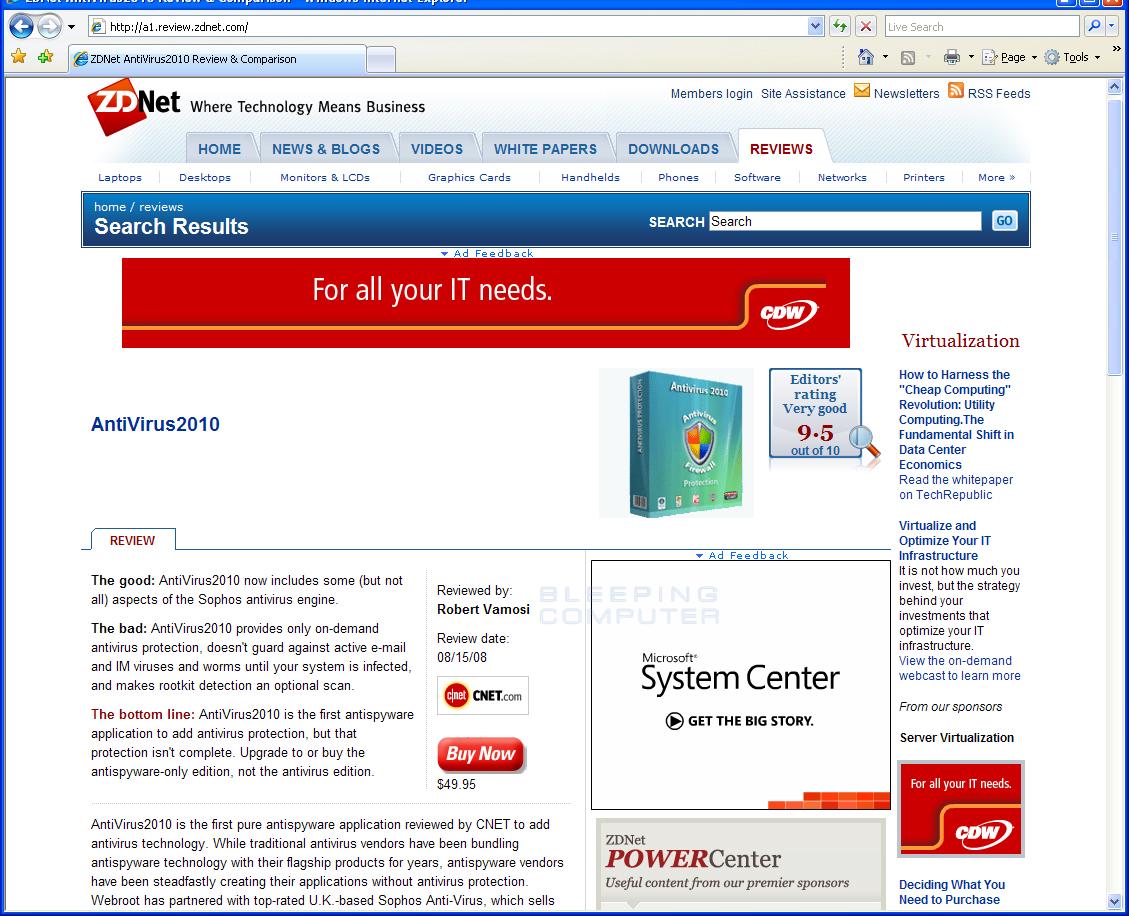
According to Lawrence Abrams from Bleeping Computer the latest rogue security software Anti-virus-1 redirects infected users attempting to visit the sites to a legitimately looking reviews of the scareware. By using this novel approach the rogue software vendor's aim is to add more legitimacy to Anti-virus-1's existence in general. However, if they truly wanted to achieve better social engineering result, they could have at least used a more recent version of the impersonated sites.
Here's how it's done anyway:
Upon installation the software modifies the HOSTS file and redirects affected users attempting to visit the review sites to a centralized location used for the hosting and promotion of even more rogue security software:
O1 - Hosts: 217.20.175.74 www.review.2009softwarereviews.com O1 - Hosts: 217.20.175.74 review.2009softwarereviews.com O1 - Hosts: 217.20.175.74 a1.review.zdnet.com O1 - Hosts: 217.20.175.74 www.d1.reviews.cnet.com O1 - Hosts: 217.20.175.74 www.reviews.toptenreviews.com O1 - Hosts: 217.20.175.74 reviews.toptenreviews.com O1 - Hosts: 217.20.175.74 www.reviews.download.com O1 - Hosts: 217.20.175.74 reviews.download.com O1 - Hosts: 217.20.175.74 www.reviews.pcadvisor.c.uk O1 - Hosts: 217.20.175.74 reviews.pcadvisor.co.uk O1 - Hosts: 217.20.175.74 www.reviews.pcmag.com O1 - Hosts: 217.20.175.74 reviews.pcmag.com O1 - Hosts: 217.20.175.74 www.reviews.pcpro.co.uk O1 - Hosts: 217.20.175.74 reviews.pcpro.co.uk O1 - Hosts: 217.20.175.74 www.reviews.reevoo.com O1 - Hosts: 217.20.175.74 reviews.reevoo.com O1 - Hosts: 217.20.175.74 www.reviews.riverstreams.co.uk O1 - Hosts: 217.20.175.74 reviews.riverstreams.co.uk O1 - Hosts: 217.20.175.74 www.reviews.techradar.com
And whereas modifying the HOSTS file is a bit of a noisy approach to hijack traffic, given the fact that end user managed to get -- ironically -- infected with a non-existent security software on their way to protect themselves from security threats, there's a high chance that this HOSTS modification will remain undetected.
- Go through related rogue security software posts: Sony PlayStation’s site SQL injected, redirecting to rogue security software; Fake Antivirus XP pops-up at Cleveland.com; Google sponsored links spreading (scareware) rogue AV
From a psychological perspective, the rise of rogue security software demonstrantes the end user's impulsive decision making based on the oldest known motivation factor - fear which in 2009 is transformed into fear of losing data. And while in the past cybercriminals used to brandjack legitimate security software, today's revenue-sharing affiliate based model for spreading rogue security software is in fact building new brands that despite their short product cycle are already affecting hundreds of thousands of users.