Son of Stuxnet within a year: expert

Stuxnet, the sophisticated malware targeted at Iran's nuclear program last year, represents the start of an arms race in the security of industrial control systems. Stuxnet-inspired malware could appear within a little as a year, said a leading critical infrastructure security expert, and traditional "air gap" protection won't be the answer.
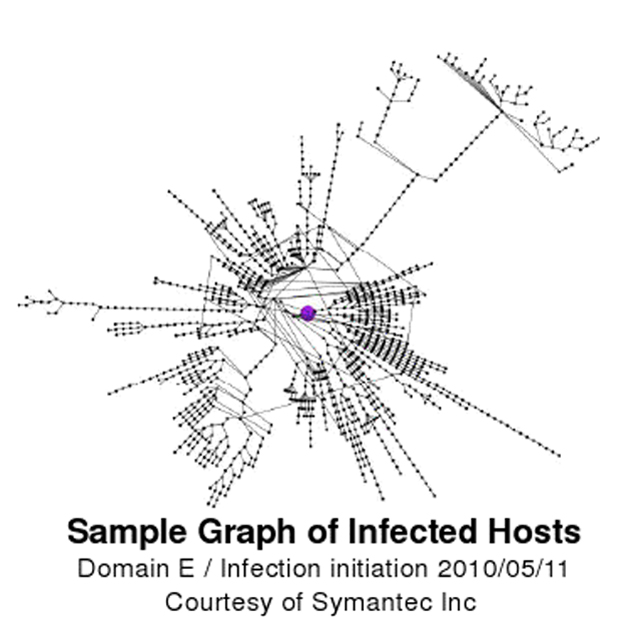
Sample graph of Stuxnet-infected hosts (Credit: Symantec/Byres Security)
Eric Byres of Byres Security has studied Stuxnet extensively. He told the AusCERT information security conference that even with an air gap separating the protected network from the outside world, all manner of data still has to flow across that gap — including project data, software updates and patches, antivirus signatures and documentation. "Even the best attempt to completely air-gap, I believe, is just an illusion. I really don't think air gaps are viable," he said.
There was speculation in the information security world that Stuxnet was brought into the Iranian facility via a USB memory stick, leading to recommendations that organisations seal the USB ports of their computers or remove them entirely. However, Byres thinks that's misguided.
Just one potential USB-free penetration technique would be to mimic a vendor's documentation. Since Siemens made the SCADA controllers targeted by Stuxnet, an attacker could mock up a Siemens disc, package it in a Siemens sleeve and deliver it to the target organisation's IT manager. The disc would include real documentation PDF files, but infected with Stuxnet.
Another security researcher told ZDNet Australia that a disc-of-documentation attack is already known to have been tried in the wild, but that attack wasn't successful.
Byres described Stuxnet as "cruise missile grade software", with a very low defect rate, much better than most commercial software.
"I run a development team, and I know that if I put five or six developers into a room with no supervision not much useful's going to come out," he said. Byres believes the Stuxnet development team must have included at least 12 people, including subject-matter experts on industrial controllers and uranium enrichment, and quality assurance. "I'd hire these people."
"I really believe that Stuxnet has changed the landscape," Byres said. "Not because Stuxnet is going to attack any one of us, but that it's acted like a training ground. It's shown the bad guys, whether it's type one, two or three, script kiddie, organised crime or nation state ... it's shown them what can be done. It's an educational experience."
Stuxnet has also shown us that it's possible to accurately target control systems, rather than relaying on collateral damage from a broader attack.
"I really believe that there's so much information shared out there that we will see a Son of Stuxnet coming over the horizon in the next year or two."
The chemical, oil and gas industries will cope with this emerging threat well, Byres said, because they already have a culture of risk management. But other sectors will need to convince their management to take responsibility.
"Somebody created an arms race. It might not even be the obvious people because in this game obfuscation is the number one trick," Byres said. I think we're in trouble."
(Front page image credit: Power to the people image by Adrian Boliston, CC2.0)