US denies attacking North Korea's internet, but whoever did required little firepower

The jury is still out on whether or not North Korea is a significant threat to the U.S. homeland, weeks after the country allegedly launched a massive cyberattack against Sony for a less-than-flattering movie about its leader.
But if you knew how North Korea's own Internet worked, you might get the impression its cyberattack capabilities were about as powerful as a kid driving a toy truck into the mud.
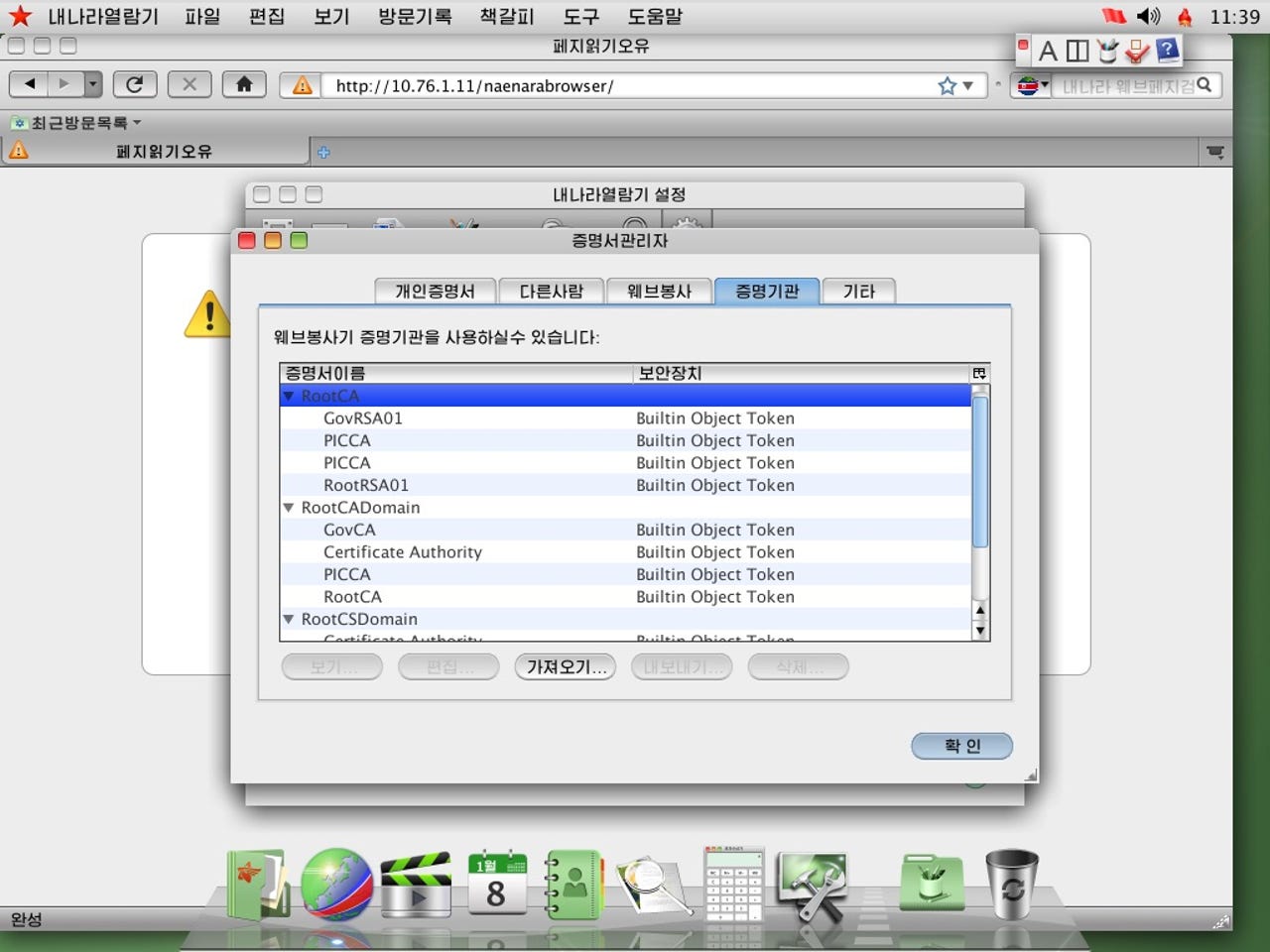
Security researcher Robert Hansen published new details about the country's homebrew web browser, a version of Firefox that comes with Red Star OS, the country's official operating system. The browser, dubbed Naenara, provided Hansen with a starting point to examine how it interacts with other servers within the country.
As you'd expect with any browser, you type in your web address and it turns it into an IP address, but some internal corporate sites (at work, for example) remain on your local network. But according to Hansen, that's where "things start to go off the rails." He said in a blog post published earlier this week that the North Korean government treats "their entire country like some small to medium business might treat their corporate office."
Each time the browser loads, its first request is to a non-routable IP address -- a server that's not reachable from outside the country. That allows the country's government to control what users see and what they don't.
What was dubbed by Hansen as the "mothership" is also a major flaw in its infrastructure, allowing hackers or state-sponsored actors to attack one single point and bring the entire network down.
Just days after the U.S. formally blamed North Korea for the Sony hack, the country's Internet collapsed, sending its few users offline for days. The U.S. government, which under its own laws has the legal weight to launch a retaliatory cyberattack, stayed mum on the outage.
On Friday, sources speaking to the AP news agency denied the U.S.' involvement, leaving unnamed non-state hackers in the frame instead.
Featured
It's no surprise that North Korea's Internet is not as it seems. There are very few people within the country that can access the outside world. In fact, very few North Koreans have ever left the country, let alone are aware there are other countries, people, cultures, and societies outside the walls of the tear-away Communist nation.
That makes surveillance a crucial part of the country's iron grip over its people.
According to Hansen, the single "mothership" server doesn't use HTTPS internally, meaning anything on the country's internal network can be monitored.
Email, calendars, and other personal content is all routed back through the same "mothership" server, Hansen said.
Hansen also said Snort intrusion detection system is installed by default. The free software is designed to prevent network intrusions, but Hansen said this could also be used to "phone home" and serve up what users are doing on the country's network.