Business
iOS 4.3.2 ... lots of fixes!
iOS 4.3.2 is out, and there are a lot of fixes.

iOS 4.3.2 is out, and there are a lot of fixes.
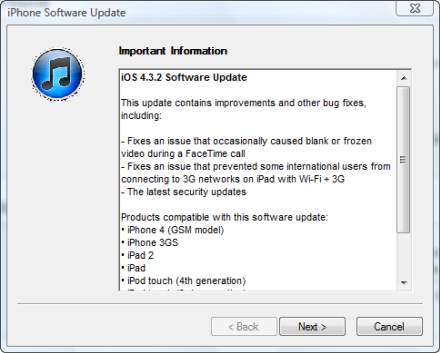
This update contains improvements and other bug fixes, including:
- Fixes an issue that occasionally caused blank or frozen video during a FaceTime call
- Fixes an issue that prevented some international users from connecting to 3G networks on iPad with Wi-Fi + 3G
- The latest security updates
There are a number of security fixes in this update too:
- Certificate Trust Policy Available for: iOS 3.0 through 4.3.1 for iPhone 3GS and later, iOS 3.1 through 4.3.1 for iPod touch (3rd generation) and later, iOS 3.2 through 4.3.1 for iPad Impact: An attacker with a privileged network position may intercept user credentials or other sensitive information Description: Several fraudulent SSL certificates were issued by a Comodo affiliate registration authority. This may allow a man-in-the-middle attacker to redirect connections and intercept user credentials or other sensitive information. This issue is addressed by blacklisting the fraudulent certificates. Note: For Mac OS X systems, this issue is addressed with Security Update 2011-002. For Windows systems, Safari relies on the certificate store of the host operating system to determine if an SSL server certificate is trustworthy. Applying the update described in Microsoft Knowledge Base Article 2524375 will cause Safari to regard these certificates as untrusted. The article is available at http://support.microsoft.com/kb/2524375
- libxslt Available for: iOS 3.0 through 4.3.1 for iPhone 3GS and later, iOS 3.1 through 4.3.1 for iPod touch (3rd generation) and later, iOS 3.2 through 4.3.1 for iPad Impact: Visiting a maliciously crafted website may lead to the disclosure of addresses on the heap Description: libxslt's implementation of the generate-id() XPath function disclosed the address of a heap buffer. Visiting a maliciously crafted website may lead to the disclosure of addresses on the heap, which may aid in bypassing address space layout randomization protection. This issue is addressed by generating an ID based on the difference between the addresses of two heap buffers. CVE-ID CVE-2011-0195 : Chris Evans of Google Chrome Security Team
- QuickLook Available for: iOS 3.0 through 4.3.1 for iPhone 3GS and later, iOS 3.1 through 4.3.1 for iPod touch (3rd generation) and later, iOS 3.2 through 4.3.1 for iPad Impact: Viewing a maliciously crafted Microsoft Office file may lead to an unexpected application termination or arbitrary code execution Description: A memory corruption issue existed in QuickLook's handling of Microsoft Office files. Viewing a maliciously crafted Microsoft Office file may lead to an unexpected application termination or arbitrary code execution. CVE-ID CVE-2011-1417 : Charlie Miller and Dion Blazakis working with TippingPoint's Zero Day Initiative
- WebKit Available for: iOS 3.0 through 4.3.1 for iPhone 3GS and later, iOS 3.1 through 4.3.1 for iPod touch (3rd generation) and later, iOS 3.2 through 4.3.1 for iPad Impact: Visiting a maliciously crafted website may lead to an unexpected application termination or arbitrary code execution Description: An integer overflow issue existed in the handling of nodesets. Visiting a maliciously crafted website may lead to an unexpected application termination or arbitrary code execution. CVE-ID CVE-2011-1290 : Vincenzo Iozzo, Willem Pinckaers, Ralf-Philipp Weinmann, and an anonymous researcher working with TippingPoint's Zero Day Initiative
- WebKit Available for: iOS 3.0 through 4.3.1 for iPhone 3GS and later, iOS 3.1 through 4.3.1 for iPod touch (3rd generation) and later, iOS 3.2 through 4.3.1 for iPad Impact: Visiting a maliciously crafted website may lead to an unexpected application termination or arbitrary code execution Description: A use after free issue existed in the handling of text nodes. Visiting a maliciously crafted website may lead to an unexpected application termination or arbitrary code execution. CVE-ID CVE-2011-1344 : Vupen Security working with TippingPoint's Zero Day Initiative, and Martin Barbella
Products compatible with this software update:
- iPhone 4 (GSM model)
- iPhone 3GS
- iPad 2
- iPad
- iPod touch (4th generation)
- iPod touch (3rd generation)