A charger that hacks iPhones

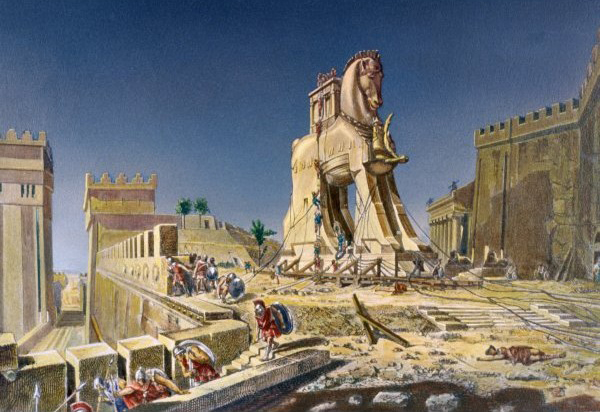
Look out for the latest innovation in Trojan Horses: A charger that can hack iPhones.
Researchers from the Georgia Institute of Technology say they've built a normal looking charger that can take over an iPhone, the BBC reports.
The device connects to an iPhone via a USB slot. It looks like a charger, smells like a charger and tastes like a charger, but its mission is to infect an iPhone with malicious software, which it can do within a minute by attacking the iPhone's iOS operating system.
The researchers will demonstrate the break-in tool at the Black Hat conference, a cat-and-mouse gathering that attracts hackers as well as information security experts. This year's confab runs July 27 through August 1 in Las Vegas.
"This hardware was selected to demonstrate the ease with which innocent-looking, malicious USB chargers can be constructed," the Georgia team wrote in their conference summary. They said they built the device from a rudimentary $45 set of circuits called a BeagleBoard.
"The researchers hid the malicious application they installed by using the same method Apple employs to conceal the location of its own applications on iOS devices," the BBC reported. "The presentation will also make recommendations about how Apple could close the vulnerability."
The practice of invading phones and computers via chargers is called "juice jacking" and is generally not difficult, according to Boston-based security consultant Jonathan Zdziarski, as reported by Mother Nature Network. MNN quoted Zdziarski from TechNewsDaily saying:
"I can speak from first-hand experience to say it is possible to write an application that, when running on the iPhone, can access all of a user's personal information — SMS, photos, etc. — without any special application permissions."
The nefarious attack-an-Apple technology from Georgia exploits the absence of iPhone alerts that inform the user that a USB device has connected. Yes, this skullduggery is as easy as U-S-B.
Photo of 19th century oil painting via Wikimedia.
This post was originally published on Smartplanet.com