Apperian powers liberated enterprises

I spoke with Apperian's SVP of Engineering, Carlos Montero-Luque and Director of Product Marketing, Stephen Skidmore about their take on BYOD. I was surprised to learn that their approach is much different than that of "traditional" BYOD program implementations. BYOD for them is a business trend that creates more of a partnership between the end user and the corporate network. Apperian's Mobile Application Management suite removes the contention and the stress between the two realms.
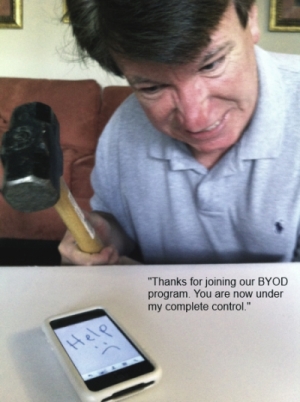
One of the problems with BYOD programs is that users can feel that their device is being invaded, usurped or ripped from their ownership and controlled by the company. While company IT managers and administrators feel that they're basically enabling rogue devices and allowing users to compromise security and disrupt balance in the network.
Users want to use their devices without obstruction or "Big Brother" looking in on what they do in their non-work time and IT managers and administrators don't want users burning work time on updating their Facebook statuses or Tweeting that "Work is boring."
Fortunately, there is a happy medium that doesn't include compromise for either party.
Apperian takes a new view of BYOD and the Mobile Enterprise: Liberation of the Enterprise through intelligent mobile application management. What this means for the device owner, you, is that your device isn't beaten into a mobile device management template that's supposed to magically manage hundreds or thousands of individual users. Mobile Device Management might place user-owned devices into a corporate "Sea of Tranquility" but often does little to quell the device owner's apprehensions. Apperian beats the corporate sledgehammer into a tool that's useful for both the device owner and the owner's employer.
And, it's not just about a kinder, gentler BYOD conversion, it's about making the experience good for everyone involved: The company, the device owner and the mobile device software administrator. Apperian provides all of the "expected" security features such as remote device lock, remote wipe and remote App delete.
One particular feature set of note is Apperian's ability to gather data and manage Apps for
- Malware
- Sources of Data Leakage
- Adoption
- Usage
- Activity
- Compliance
Apperian is almost like a private iTunes for your company.
Enabling mobile workers is no longer about just managing their devices – it is about empowering the workforce through transformative business apps. The Apperian EASE® platform provides the features you need to securely manage your corporate mobile apps and data.
Here is a list of Apperian's Mobile Application Management features:
- Cloud-based
- User-controlled access
- Customizable App catalog
- "App wrapping" security
- Over-the-air App updates
- Unified admin console
- App behavior inspection
- User and App reporting
- MDM-free App deleting
- Crowdsourcing and App ratings
Their list of big business names is convincing too: Estee Lauder Companies, Cisco, NVidia, AT&T and Proctor & Gamble to name a few.
Adding more fuel to the Apperian fire is their recent (July 18, 2012) announcement that Appthority Platform™ is now integrated into its Enterprise App Services Environment (EASE) service. Addressing the BYOD trend, the addition of Appthority’s automated app inspection platform will help businesses to determine risks in mobile applications before they are deployed.
Integrating Appthority’s app inspection into EASE is another proof point of Apperian’s strategy to provide businesses with a modular solution that incorporates the best products and services to manage their enterprise mobile environments. This approach enables IT managers to apply the exact capabilities they require and to manage it all from a single admin console.
The Appthority Platform™ identifies the risky behaviors behind iOS and Android apps. What may be masquerading as a simple calendar or social networking app may also put sensitive data at risk, track for location or hide mobile malware. Appthority protects companies from risky apps, enabling them to embrace BYOD and use their own mobile devices for work. Appthority is available as a premium feature to Apperian customers.
I came away impressed with Apperian from our discussion and I suggest that, if you're considering a BYOD program for your company--or if your company is considering implementing such a program, suggest that the decision makers take a look at Apperian before trudging down a path that might not work for you or your company.
To be fair, I don't that there is a single correct answer for every company. I think you have to evaluate your administrative, security and user's needs before deciding on a mobile management suite, be it application, device or some other method. The purpose of this post is to make you aware of your options.
One of the key things to consider when down-selecting companies is how you want to manage mobile devices within your corporate boundaries, whether they're physical or virtual. Also consider your users and their needs. Do you want to manage users, Apps, devices, content or a combination of those. Prepare to ask yourself some tough questions such as, "What types of devices are we going to allow?" and "Are there devices or Apps that we will ban when connected to the corporate network?"
The answers might seem easy upon first glance but you have to be careful that you don't alienate your users. As Carlos and Stephen noted in our discussion, users are more tech savvy now than they were a few years ago and that means that they want fewer restrictions not more. They understand the need for security but they won't understand the need for "spying."
It would be productive to have an internal information gathering survey prior to launching a BYOD program so that your users can give their input in a non-threatening and constructive manner.
Remember that the employer-employee relationship is symbiotic. It's like any relationship --it requires some compromise--not on security and functionality but on creating a collective vision that both sides can live with.
From your experiences with BYOD, what are some of the pitfalls that you've seen thus far? What, if anything, has been done to fix them? Talk back and let me know.