Backdoor vulnerabilities discovered in Sony IP cameras

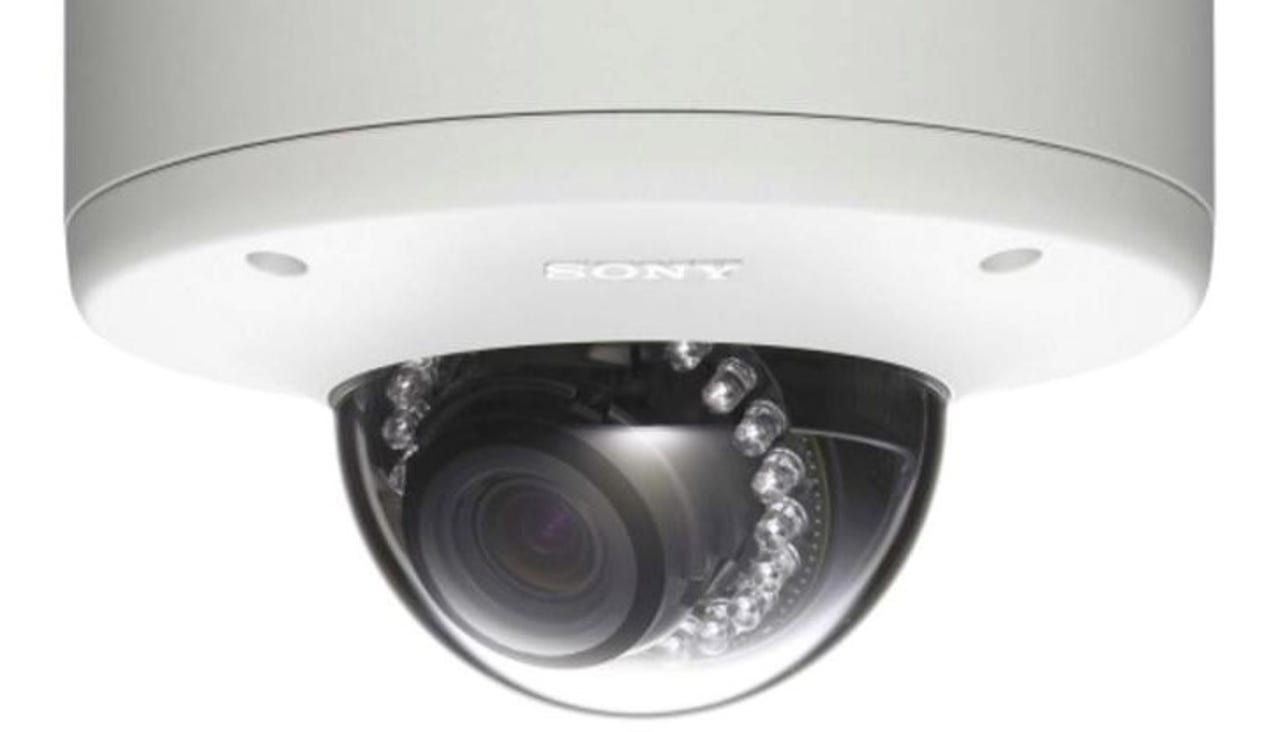
Researchers have discovered backdoors in Sony IPELA Engine IP cameras which could affect as many as 80 models.
Cybersecurity firm SEC Consult said on Wednesday that the security flaw allows attackers to remotely execute code, hijack vulnerable cameras, disrupt device functionality, and spy on users.
In addition, the backdoor grants attackers the opportunity to add compromised Sony IP cameras to botnets as slave nodes, in the same manner that cyberattackers used the IoT-based Mirai botnet to disrupt online services.
Security
The security flaw, deemed critical, lies in backdoors which allow attackers to enable the Telnet/SSH service remotely. Once this backdoor has been used, a secondary backdoor leads the way to a Linux shell with root privileges.
The vulnerability can be exploited through default credentials which are hard coded into the cameras as well as through the Internet if the web gateway of the device is exposed.
It may also be that attackers with physical access to the device can log in through serial ports.
"We believe that this backdoor was introduced by Sony developers on purpose (maybe as a way to debug the device during development or factory functional testing) and not an unauthorized third party," the company says. "We have asked Sony some questions regarding the nature of the backdoor, intended purpose, when it was introduced and how it was fixed, but they did not answer."
The vulnerability was confirmed through an SNC-DH160 camera, alongside the firmware of generation six cameras.
Sony was informed by SEC Consult about the vulnerability in November and the tech giant released updated firmware closing the security hole for the affected models in the same month before the research was made public. The new firmware can be found here.
Separately, the research team from Cybereason also discovered zero-day vulnerabilities in cameras which are based on old Linux software. The bugs have been found in at least 10 different camera models from 10 different vendors including VStarcam, which are sold through Amazon and eBay.
"Unfortunately, even though we've responsibly disclosed the flaws, this may not lead to the vulnerabilities getting fixed," Cybereason says. "The cameras aren't designed to receive software updates so the zero-day exploits can't be patched."