Baidu Browser transmitting IMEI, location, URLs visited, CPU model number: Citizen Lab

The Baidu Browser for Android and Windows has been found by Citizen Lab, a research group within the University of Toronto, to be sending a large amount of users' personal data back to its servers.
Citizen Lab said in its report that the Android version of Baidu Browser is sending a user's GPS coordinates and last update time, search terms entered into the address bar, and URLs visited without any form of encryption. The browser also sends the phone's unique IMEI number and nearby wireless networks, along with MAC addresses and signal strengths under a poorly implemented encryption scheme.
The Android version of the browser was also found to be vulnerable to man-in-the-middle attacks when looking for updates; however, this issue was later fixed.
For its Windows version, Citizen Lab said the browser also sends address bar search terms in the clear back to Baidu servers, but also used its easily breakable encryption scheme to transmit a trove of personal information, including: Hard disk drive serial number, model number, and controller version number; the computer's MAC address; URLs visited, including page title; CPU model number; and file system volume serial number.
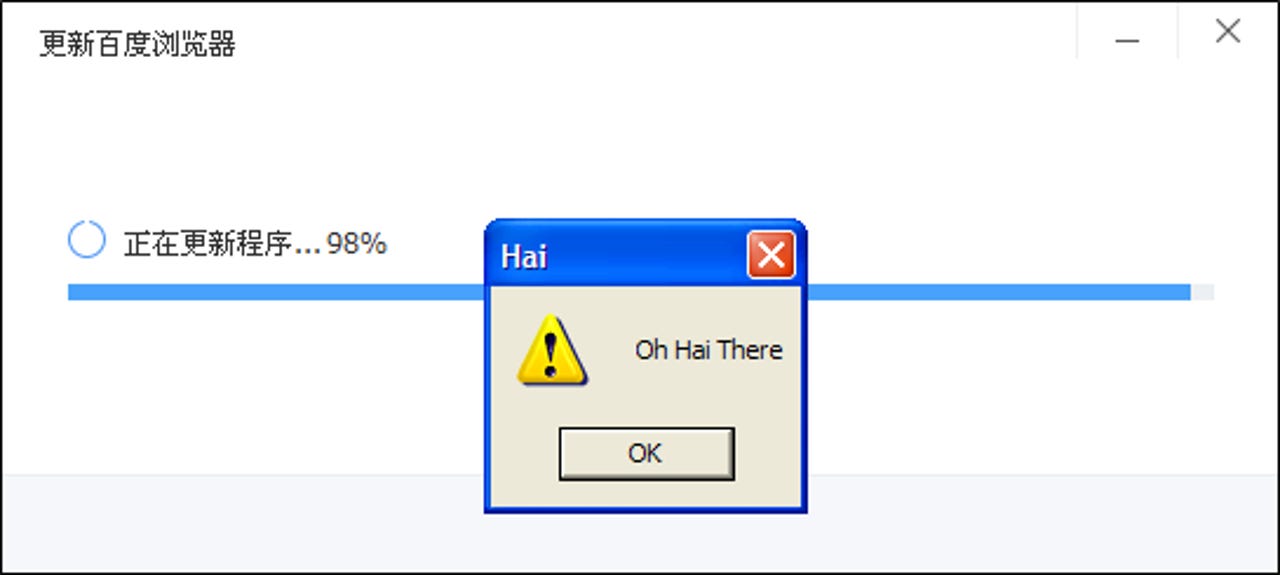
Citizen Lab demonstation of a man-in-the-middle attack on Baidu Browser's self-updater.
The Windows version was also found vulnerable to insecurely updating itself, but now checks the signature of the downloaded file.
Baidu is one of the most visited sites on the internet, with the company dominating search in China as well as investing in other technology areas, including artificial intelligence and global ride-sharing service Uber.
In response to questions posed by Citizen Lab [PDF], Baidu said the data it collects is stored in its datacentres, which are "equipped with state-of-the-art security".
"Baidu endeavors to collect data in a way consistent with the highest standards of security and user privacy in the industry," the company said. "Pursuant to applicable laws, regulations, and policies as well as Baidu's own stated terms of service, we guarantee protection of user data.
"While Baidu will sometimes share certain non-sensitive user data with commercial parties pursuant to applicable laws, regulations, and policies, and will do so based on the nature of the relationship the company has with those parties, we will strictly protect all personal data, and will not share certain sensitive personal data with any third parties."
Latest news on Asia
The company did not reveal in its answers why it collects the data it does, repeatedly saying instead that it is strengthening its security.
Citizen Lab delayed its announcement in order for Baidu to resolve the issues it had found, but analysis after the updates were released showed that little progress was made, except for changes to the update procedures and transmitting personal information on start-up on the Android version over SSL instead of in the clear.
Both versions of the browser, according to Citizen Lab, continue to leak sensitive data and address bar searches.
The issues were pinned by Citizen Lab to be a result of using the Baidu SDK. Popular Android file explorer app, ES File Explorer, faced similar concerns in late 2014 for using the SDK for anonymous statistics collection, but said the claims were groundless.
"Any app that uses this SDK for statistics and event tracking sends messages to Baidu's servers containing the same sensitive information in unencrypted and easily decryptable form that we saw the Baidu Android browser sending when it starts up. This includes the phone's unique IMEI number, current GPS location, and nearby wireless networks," Citizen Lab said in its analysis.
Jeffrey Knockel, senior researcher at the Citizen Lab, said in a statement that most users would have no knowledge that their data is being transmitted, and would therefore be unable to stop it from occurring.
"The extent of these issues and the ease with which they were found suggests that security researchers need to better engage with software companies in foreign markets," Knockel said.
Last year, Baidu partnered with Amazon to preinstall its apps on Fire Tablets in China, while this year it drew criticism after administration of its health forums were found to be sold to commercial organisations and personnel, including unlicensed hospitals and doctors.
In 2014, Baidu apologised after it was caught cheating in an international supercomputer image-recognition test, and has been banned from participating in the event.