Meet Coldroot, a nasty Mac trojan that went undetected for years

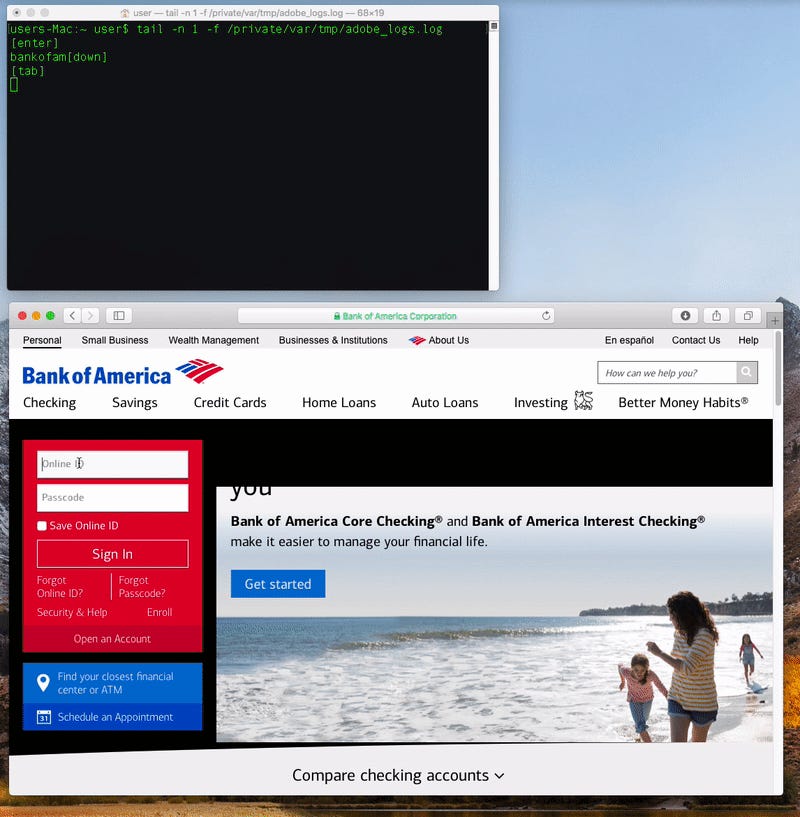
A Mac malware that can silently, remotely control a vulnerable computer and steal passwords from a user's keychain has gone largely unnoticed by antivirus makers for two years -- even though the code is readily available to download.
Security
Patrick Wardle, chief research officer at Digita Security, revealed in a blog post Tuesday details of Coldroot, a remote access trojan.
These kinds of malware are installed and access deep parts of the operating system in order to gain full, remote control of the system at any given moment -- as if an attacker was sitting at the computer in person.
But after tearing down the malware in a new analysis, he found that none of the antivirus makers listed on online malware scanner VirusTotal were able to detect the malware at the time of his research -- even though its code was published in 2016.
Though the malware is "not particularly sophisticated," said Wardle, "it's rather 'feature complete'."
According to Wardle, the malware when activated can record and steal passwords, list files, rename and delete files, download and upload documents, remotely view the desktop in real time, and shut down the system.
The malware masquerades as a document, which when opened, presents a prompt for the user's password. In the hope that a user will naively enter their credentials, the malware will silently install and contact its command and control server to await instructions from an attacker.
But in order to get access to wider parts of the system to carry out nefarious tasks, the malware needs to gain access to the Mac's accessibility functions. In order to do that, a user would have to manually add the malware to the list in the system preferences -- something nobody would willingly do.
Instead, the malware modifies macOS' privacy database which lets the malware interact with system components to the system. Once the malware is hooked in, the trojan will persist on the computer with full system access each time the system is restarted.
Apple patched against the malware in macOS Sierra by protecting the database with system integrity protection, which won't automatically grant the malware accessibility rights -- even with a user's password.
Wardle said his free to download Mac security tools will help to protect against these kinds of attacks.
Wardle confirmed to ZDNet that he reached out to antivirus makers, which should soon -- if not already -- start detecting the malware.
"It is a good illustrative example that hackers continue to target macOS!" he said.