'Critical' Vista, IE 7 patches highlight MS security updates

This month's batch of patches from Microsoft includes six bulletins covering at least 15 vulnerabilities, including several critical code execution holes in Windows Vista and Internet Explorer 7.
In all, Redmond pushed out four critical bulletins with fixes for flaws that could put Windows users at risk of complete PC takeover attacks.
The mega IE update addresses a total of six flaws, including one that was publicly discussed prior to Patch Tuesday. Interestingly, all six IE bugs are rated "critical" across the board, except for some versions of Windows Server 2003.
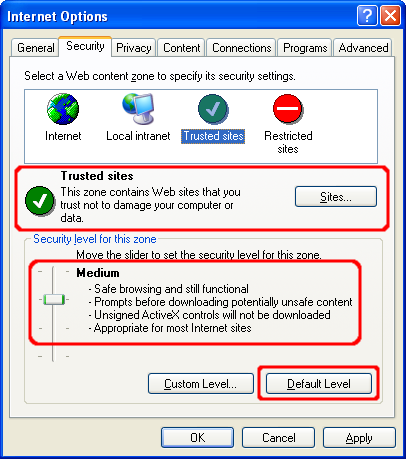
(NOTE: Click on image at right for step-by-step instructions on some key configuration changes you can make to run/use IE securely)
Another high-priority update to pay special attention to is MS07-035, which touches a "critical" vulnerability in the way that the Win32 API validates parameters. This bug does not affect Windows Vista.
Microsoft provides a dire warning:
An attacker could exploit the vulnerability by constructing a specially crafted Web page that could potentially allow remote code execution if a user viewed the Web page. An attacker who successfully exploited this vulnerability could take complete control of an affected system.
Windows Vista is also immune to MS07-031, a "critical" bulletin that covers a flaw in the Secure Channel (Schannel) security package in Windows. "This vulnerability could allow remote code execution if a user viewed a specially crafted Web page using an Internet Web browser or used an application that makes use of SSL/TLS," according to the bulletin. Affected software includes Windows 2000, Windows XP and Windows Server 2003.
However, the built-in Windows Mail client in Vista didn't escape unscathed. The MS07-034 update contains fixes for four vulnerabilities (two publicly discussed before today) that could lead to code execution attacks. This update also affects Outlook Express.
The gaping hole that dings Windows Vista comes with this warning:
A remote code execution vulnerability results from the way local or UNC navigation requests are handled in Windows Mail. An attacker could exploit the vulnerability by constructing a specially crafted e-mail message that could potentially allow execution of code from a local file or UNC path if a user clicked on a link in the e-mail message. An attacker who successfully exploited this vulnerability could take complete control of an affected system.
Windows Vista users will also see an automatic update for MS07-032, a "moderate" bulletin that fixes an information disclosure issue. The bug "could allow non-privileged users to access local user information data stores including administrative passwords contained within the registry and local file system," Microsoft warned.
The last bulletin this month (MS07-030) fixes two "important" bugs in Microsoft Visio 2002 and Microsoft Office Visio 2003.