Exploit beamed via NFC to hack Samsung Galaxy S3 (Android 4.0.4)

AMSTERDAM -- Using a pair of zero day vulnerabilities, a team of security researchers from U.K.-based MWR Labs hacked into a Samsung Galaxy S3 phone running Android 4.0.4 by beaming an exploit via NFC (Near Field Communications).
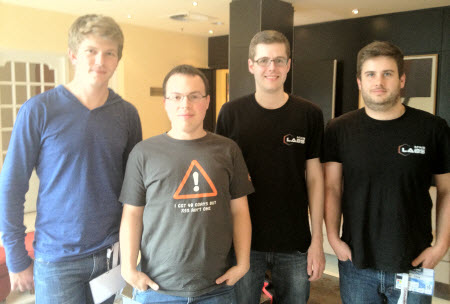
The team -- Tyrone Erasmus, Jacques Louw, Jon Butler and Nils (yes, that Nils) -- carted off a $30,000 cash prize as part of the EuSecWest mobile Pwn2Own hacker contest.
According to Erasmus, the exploit was delivered via NFC, the short-range wireless technology allows the sharing of small payloads of data between an NFC tag and an Android-powered device. The hackers exploited a weakness in the way NFC is implemented in the Galaxy S3 to deliver a malicious file that was automatically opened by the Android document viewer.
Once the file opened, the team exploited a zero-day flaw in the document viewer to launch a code execution attack. A second Android privilege escalation vulnerability, also zero-day, was then used to get full rights on the device.
[ SEE: Mobile Pwn2Own: iPhone 4S hacked by Dutch team]
With escalated rights, the team had access to all the data on the Samsung S3, including the e-mail and SMS databases, the address book, the photo gallery and access to third-party app data.
"We can do anything on the phone with our Trojan running in the background," Erasmus said in an interview after the successful hack. "The user is oblivious to it because NFC allows us to open the malicious document without any user interaction."
Although the MWR team used NFC to deliver the exploit, Erasmus warned that the same vulnerability could be exploited in drive-by downloads via malicious websites or via rigged e-mail attachments.
He said the winning exploited bypassed several Android security mitigations including the limited ASLR (Address Space Layout Randomization) and DEP (Data Execution Prevention). Once the mitigations were bypassed, Erasmus and his team installed a customized version of an Android pen-testing framework called Mercury.
With Mercury, this is the mobile equivalent of Metasploit, the team could sent exfiltrate user data from the device to a remote listener, including dumping SMS and contact databases, placing a call to a premium rate number or even taking snapshots with the phone's camera.
According to Nils, who is best known for his work hacking into IE, Safari and Firefox at Pwn2Own 2009, the anti-exploit mitigations built into Android 4.0.4 are somewhat trivial to bypass. He specifically pointed to the "incomplete" ASLR implemention that doesn't cover the Android linker and another process that is responsible for starting applications on the device.
He said ther protections which would make exploitation harder were missing. Nils said Google is due to beef up the mitigations in Android 4.1, codenamed Jelly Bean.
Although the vulnerability exists as zero-day across all Android platforms, including version 4.1, Nils said the exploit won't work on Jelly Bean because of the improved mitigations.
MWR Labs plans to release a public version of the customized Mercury app in the next release. The team will also release fuzzing modules to help researchers pinpoing vulnerablities in the Android code.