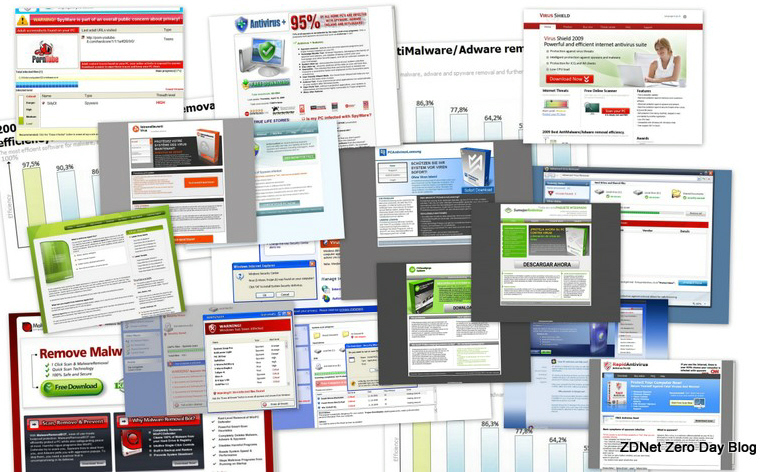
Google: Scareware accounts for 15 percent of all malware
In an upcoming research entitled "The Nocebo Effect on the Web: An Analysis of Fake AV distribution", Google's Security Team is about to release the results from their 13 month study into the growth of fake security software, also known as scareware or Fake AV.
- The analysis is based on 240 million web pages used as a sample
- 11,000 domains involved in Fake AV distribution discovered based on the sample
- Fake AV currently accounts for 15% of all malware Google detects on the web
- Fake AV attacks account for 60% of the malware discovered on domains that include trending keywords
- Fake AV is responsible for 50% of all malware delivered via Ads
What's the first thing that makes an impression based on these findings? It's the small number of domains they were able to identify, despite the fact that 60% of the domains hijacking trending topics serve scareware, and that 50% of all malware delivered through malvertising is fake AV.
- Go through related posts: The ultimate guide to scareware protection; FBI: Scareware distributors stole $150M
This number is the effect of the active evasive practices applied in order to trick Google's crawlers, by serving them legitimate content, and the malicious one to the unaware end user.
Cybercriminals have been abusing Google Trends (Cybercriminals syndicating Google Trends keywords to serve malware; Syndicating Google Trends Keywords for Blackhat SEO) for scareware or malware serving purposes for years.
The same, although in smaller proportions, has been taking place through legitimate ad networks (Malware-infected WinRAR distributed through Google AdWords; Scareware Campaign Using Google Sponsored Links), with malvertising (the practice of serving malicious content through legitimate ad networks) already trending.
How are cybercriminals tricking Google's crawlers in the first place? In the very same way search engine optimization scammers have been doing since the early days of the Web - through content cloaking, through Google's playbook by using noindex, nofollow, noarchive tags, and through one of the most effective practices used by blackhat SEO campaigners these days - the http referrer:
- "var ref,i,is_se=0; var se = new Array("google.","msn.","yahoo.","comcast.","aol."); if(document.referrer)ref=document.referrer; else ref=""; for(i=0;i<5;i++"
Pragmatic tips for preventing scareware infections:
- Go through ZDNet's Guide to Scareware Protection, explaining the basics of what scareware is, the tactics used by the cybercriminals to spread it, as well as the main characteristics of the scam. Even better, share the link to the guide with your social circle in an attempt to raise awareness on one of the most prolific monetization tactic cybecriminals use these days.
- In 99% cases of the scareware infection attempts, the user is in control of situation. The remaining 1% are the campaigns where scareware is pushed through client-side exploits, or through a botnet the user is unknowingly participating in. Since scareware is relying entirely on the use of social engineering and legitimately looking "You're Infected!" pop-ups, learning the characteristics of the scam would help you to spot and avoid executing the binary it's enticing you to do.
- Although perceived as a prank by some, scareware has been converging with ransomware for a while now. Realizing the mess that could take place with a scareware variant locking down your PC, or encrypting key files on it, is logically supposed to increase the end user's vigilance in those cases where their Internet Security Suite doesn't alert them in the first place.
- Don't bother attempting to verify the legitimacy of Mega Antivirus Solution 2010, since cybercriminals systematically rebrand the same piece of scareware with a different name. In fact, a common practice these days is to see scareware A using a blackhat SEO campaign by promising to remove scareware B. Use a basic tcp wrapper hosts.deny: ALL approach - automatically assume the worst, and basically check whether the software pretending to be legitimate is actually real.
- Browsing the Web in a sandboxed environment, using least privilege accounts, and ensuring you are free of client-side exploitable flaws will mitigate a huge percentage of the risk.
Google is set to release their complete report at the end of the month. The company is the best position to make an impact in the fight against scareware through the SafeBrowsing project, now an inseparable part of modern browsers. An update will be posted as soon as the research becomes public.