IE7 or Firefox 2: Which browser is more secure?

Microsoft and Mozilla are on a collision course, both racing to complete major updates to their flagship web browsers scheduled for release this fall. Over the past two years, Firefox has zoomed from nowhere to gobble a significant chunk of market share at Internet Explorer’s expense. The biggest selling point for Firefox is its generally better record on security issues; so it’s no accident that Microsoft has paid significant attention to beefing up security features in Internet Explorer 7.
Both browsers are officially out in widely available public beta releases (Internet Explorer 7 Beta 3 and Firefox 2 Beta 1), so it’s a good time to compare how well each one performs.
For this report, I’ve put together an image gallery that shows exactly how the Windows XP version of each browser performs when faced with common security threats.
And what are those threats? Basically, everyone who spends any significant time on the Internet has to be mindful of the following four threats:
- Exploits that attack unpatched vulnerabilities in program code. This is the worst threat of all, because a successful attack can give an intruder complete control of your computer and every bit of information on it.
- Deceptive downloads. Some of the nastiest bits of spyware and malware walk through the front door, disguised as or piggybacking along with benign or harmless-sounding programs.
- Phishing attempts. The most popular form of browser-based crime in 2006 is the phishing e-mail, which tries to sucker its victim into filling in valuable personal information – bank passwords, credit card details – in a phony web form.
- Hostile add-ons. A rogue program can be merely annoying – hijacking your home page and spewing unwanted pop-ups – or it can take the form of a Trojan horse or dialer that can drain its victim’s bank account.
Some of these threats are technical, but the majority take the form of social engineering. A computer user who has administrative rights over a computer can override any security feature or protective program. The challenge for the browser designer is to give the user enough information so that he or she can make an intelligent decision.
Let’s look at the two new browsers and compare how each one handles different threats.
EXPLOITS
There’s no shortage of vulnerabilities for either IE or Firefox. In the eight months since Firefox 1.5 was released, the Mozilla Foundation has published 56 security advisories, 26 of which involved vulnerabilities that “can be used to run attacker code and install software, requiring no user interaction beyond normal browsing.” Those flaws have been fixed in a series of six maintenance releases.
Counting the security bulletins for Internet Explorer is a little more difficult, because Microsoft doesn’t break them out neatly by product. Independent security researchers who’ve compared the two generally give the edge to Firefox; Secunia, for example, claims that 21 of 105 security advisories for Internet Explorer are currently unpatched, although only one is rated “highly critical.” By contrast, only three vulnerabilities are listed as unpatched for Firefox, and none of them are considered critical.
Brian Krebs, of the Washington Post, compared the records of Mozilla Firefox and IE6 and concluded:
For at least 38 days in 2005, IE was vulnerable to unpatched critical security flaws that were being exploited actively by viruses, worms and spyware. For at least 256 days last year, Internet Explorer contained unpatched vulnerabilities where the exploit method had been publicly disclosed but was not necessarily being used.
For Firefox, there were about 35 days in 2005 where exploit code for a known vulnerability was available for an unpatched flaw, and zero days when a worm or virus was known to be taking advantage of an unpatched flaw.
The theoretical edge goes to Firefox, but both companies have kept busy in recent years making updates available, and there’s no evidence that any widespread outbreak of malware has been attributable to unpatched vulnerabilities in either one.
Will IE7 improve this spotty record? Perhaps. According to Microsoft’s Tony Chor, a Group Program Manager on the Internet Explorer team, part of the problem was old, sloppy code. “Over time, IE had developed 13 or 14 different places in the code where we place URLs. Inconsistent results allowed us to get beat. This is where we rearchitected a big part of IE so that one routine evaluates the URL.” Microsoft is betting that the new URL parser will make it easier for developers to avoid vulnerabilities in the first place and to fix them more quickly when they do appear. But only time will tell whether that effort will pay off as expected.
DOWNLOADS
Both browsers put plenty of speed bumps in the way of any program code you want to download. Whether you use IE7 or Firefox 2, you’ll need at least three clicks (and sometimes several more) to download and install a program.
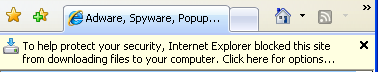
On this score, at least, IE has a better set of features to prevent users from being tricked into downloading a program they really don’t want. In IE7, a download dialog box will only appear if you click a link that leads directly to that download. If a website designer uses script to try to pop up a download box and force you to deal with it, IE intercepts the script and displays a prompt in the Info bar instead.
The Info bar doesn’t interfere with navigation, and you can ignore it completely if you want to. By contrast, Firefox permits web pages to trigger a download dialog box that has to be dealt with.
In addition, IE provides more information about the publisher of a program as well as whether the program is digitally signed. That’s not necessarily a big advantage for users, however, especially when dealing with publishers who are actively trying to deceive them. During the course of testing, I found one program that had been digitally signed using a legitimate certificate but phony information, and two others that had been signed using homemade certificates, including one from – no kidding – Joe’s-Software-Emporium.
PHISHING
Both IE7 and Firefox 2 include features designed to prevent users from being tricked by phishing attempts. Neither set of features is completely new; Microsoft’s version appeared in its MSN toolbar for IE6 last year, while the Firefox equivalent first appeared as the Google Safe Browsing extension and later in the Google Toolbar for Firefox.
Both programs claim to use similar techniques, analyzing the URL, the page content, and the structure of the page. In addition, both programs use external blacklists that are updated regularly. Firefox displays this pop-up balloon:
While IE7 displays a blood-red badge and warning box:
It’s difficult to test any phishing filter with authority. ISPs shut down most phishing sites when they’re reported, so any link that’s more than a day or two old is likely to lead to a 404 error. The two “live” sites I visited in each browser hardly constitute a scientific sample, but it’s still worth noting that IE7 flagged both pages as confirmed phishing sites, while Firefox 2 missed them both. In my experience with IE7 over the past few months, it’s been consistently accurate, flagging suspicious sites with a yellow label and turning them into confirmed sites within a matter of hours. I haven’t spent enough time with the Firefox/Google code to form an opinion.
Update 4-August, 8:30AM PDT: To rule out the possibility that there was something wrong with my initial test platform, I've now retested the anti-phishing features in Firefox 2 Beta 1 on two different machines with four different phishing URLs. All of them were flagged by IE7 Beta 3, but Firefox wasn't able to identify any of them. I repeated the test with the Google Toolbar for Firefox on Windows XP with Firefox 1.5.0.6 with identical results. See this post for more details.
Update 4-August, 3:40PM PDT: A representative of Mozilla's PR agency contacted me and says that the anti-phishing feature in Firefox 2 Beta 1 "was intended to test the core Phishing Protection framework within the browser, not to provide a full list of suspected scam sites."
BROWSER ADD-INS
Last, but certainly not least, is this category, which includes IE7’s infamous ActiveX feature. Conventional wisdom blames most spyware installations on ActiveX prompts and “drive-by downloads,” but that reputation may be based on behavior from a bygone era.
First, some definitions. ActiveX controls are simply binary code that runs inside the browser. It’s a powerful way to bring the power of local computinfg resources into the browser; unfortunately, it’s also been a vector for unscrupulous software makers to push spyware, pop-ups, and home-page hijackers onto unsuspecting users’ machines.
Before Windows XP Service Pack 2, if you used IE to visit any web page that contained an ActiveX control, it could display a dialog box inviting you to install that software, and spyware vendors specialized in making those controls sound like essential system patches. Because the old-style ActiveX dialog box resembled a system prompt, it was easy to trick users into installing unwanted software by pitching it as a required update. And if the user said no, well, pop up that dialog box again, and keep doing it until you wear down his resistance.
In post-SP2 versions of IE, including IE7, ActiveX prompts appear in the Info bar, where they don’t interfere with navigation and can be safely ignored. In addition, a page can prompt the user only once – no more multiple requests to install a piece of software. In fact, the behavior is essentially identical to any other software download
In addition, IE7 adds a mechanism to prevent sites from exploiting controls that are already installed on your PC, such as those included with Windows. The so-called ActiveX opt-in provides a warning message when any page tries to use a control it didn’t install. In IE7, it’s literally impossible for an ActiveX control to do a “drive-by install” – it requires the, um, active participation of the user.
Those changes make it far more difficult for spyware pushers to deceive an innocent and unsophisticated user, but they don’t eliminate ActiveX completely. And that’s probably a good thing. After all, at least a half-dozen high-profile Internet Explorer add-ins, including Macromedia Flash, QuickTime, and the iTunes Music Store use ActiveX controls – not to mention Windows Update and a host of small but useful tools like Crucial Technology’s System Scanner and the test suite from PC Pitstop.
And what about Firefox? It doesn’t do ActiveX, so it’s perfectly safe, right?
Well, not exactly. Firefox has its own add-on model with its own set of security issues. A poorly written or hostile Firefox extension can cause serious problems. The popular Greasemonkey extension had to be yanked last year after security researchers uncovered a serious security flaw. And a security researcher earlier this year wrote a simple extension that sniffs HTML forms in search of passwords and sends the results to an e-mail address specified in the extension. Yes, the user has to choose to install that extension, but the same is true of ActiveX controls. In fact, extensions can even be used to install executable programs, a technique that Sun uses with its Java installation.
As a Mozillazine article noted earlier this year:
[T]he Mozilla Foundation has never claimed that extensions willingly installed by users are safe and it's long been known to the savvy that extensions can do practically anything once they are running on a user's system. However, it's worrying that some users believe that extensions are implicitly safe.
And there’s the bottom line. Come this fall, when both browsers are officially released, the playing field will essentially be level. Both IE7 and Firefox 2 add extra layers of protection and provide additional information to users to help them make intelligent decisions. In the final analysis, though, no browser can force a user to make smart or sane decisions. They can only point the right way.