LastPass phishing attack avoids two-factor authentication in data theft

[Update 17.00 GMT: LastPass statement]
LastPass is the target of a particular brand of phishing attack which can result in the loss of user credentials and the bypass of two-factor authentication systems.
Sean Cassidy, security researcher and CTO of CTO Praesidio, a cloud cybersecurity startup, revealed at SchooCon 2016 held in Washington, D.C. that the phishing attack, dubbed "LostPass," is sophisticated enough to fool users into handing over their passwords, email, and all the passwords and documents stored in their LastPass vault.
Fairfax, Virginia-based firm LastPass is well-known for offering a file and password vault to keep all of your credentials safely in one place. It is no longer safe to rely upon a single password for multiple online accounts, and the more complex, the better -- but remembering this data can be difficult.
Instead, LastPass capitalizes on users happy to remember just one set of credentials to access everything else.
However, Cassidy said in a blog post that this system, like many others, is not invulnerable to phishing campaigns -- the use of fraudulent emails and Web pages which appear legitimate, but are used solely to steal information and install malware.
The LostPass phishing campaign works because "LastPass displays messages in the browser that attackers can fake," according to the researcher.
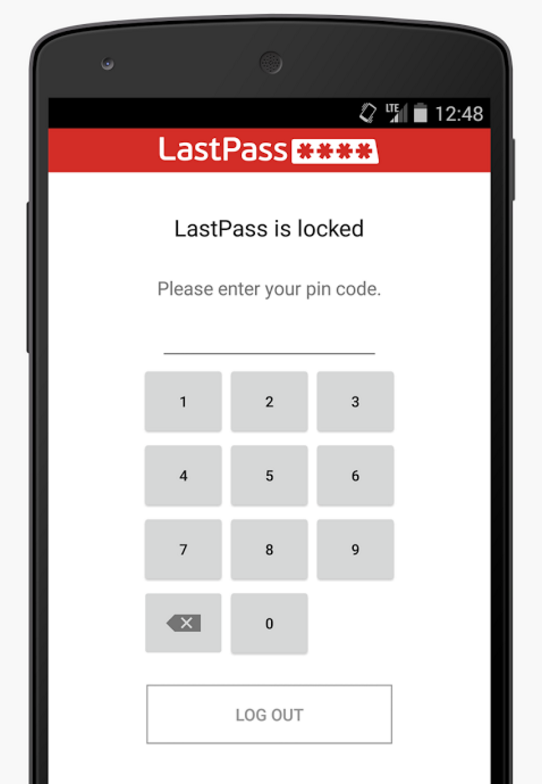
"Users can't tell the difference between a fake LostPass message and the real thing because there is no difference," Cassidy noted. "It's pixel-for-pixel the same notification and login screen."
Even if you enable two-factor authentication, as LastPass has an API which can be accessed remotely and a logout cross-site request forgery (CSRF) flaw, your information is still at risk.
To launch the LostPass attack, the researcher says the intended victim must visit a malicious website or a real website vulnerable to XSS. Once laden with malicious code, the website can then prompt the user with a notification which shows login expiry and an appeal to log in again -- made worse by the CSRF flaw as the website can log the user out of LastPass to make the request appear legitimate.
Security
Once the user clicks a fake image to log back in, a login page which looks identical to LastPass can be used to steal credentials. As the API is open, the attacker's server can go so far as to check to see if the credentials are correct and whether two-factor authentication is needed.
If two-factor authentication is necessary, an attacker can redirect the user to a two-factor prompt.
Cassidy says:
"Once the attacker has the correct username and password (and two-factor token), download all of the victim's information from the LastPass API.
We can install a backdoor in their account via the emergency contact feature, disable two-factor authentication, add the attacker's server as a "trusted device". Anything we want, really."
The researcher says the attack works best against Chrome as LastPass uses an HTML-based login page for this browser.
Cassidy informed LastPass of the security issue in November and acknowledgement was given in December. The company has issued a fix to try and mitigate this attack through an alert which warns users when they type their master vault password into some other websites. However, the researcher is not best pleased with this answer to the issue. Cassidy commented:
"On an attacker-controlled website, it is trivial to detect when this notification is added. Then the attacker can do whatever. In LostPass, I suppress the notification and fire off a request to an attacker server to log the master password."
The attack's code, the LostPass tool, is available via GitHub.
Last month, LastPass revamped the password vault service with the introduction of LastPass 4.0. This attack is specifically designed to work against this latest version.
A LastPass spokesperson told ZDNet:
"Security is our focus here at LastPass. We value the contributions from the research community that help us offer an even more secure service and provide us an opportunity to educate users about security threats."
10 things you didn't know about the Dark Web
Read on: Top picks